The article explains Microsoft’s ODR mechanism for native MCP registration, enabling AI agents to discover and invoke system tools through the Model Context Protocol, preparing Windows for secure agent-driven workflows and integrations.
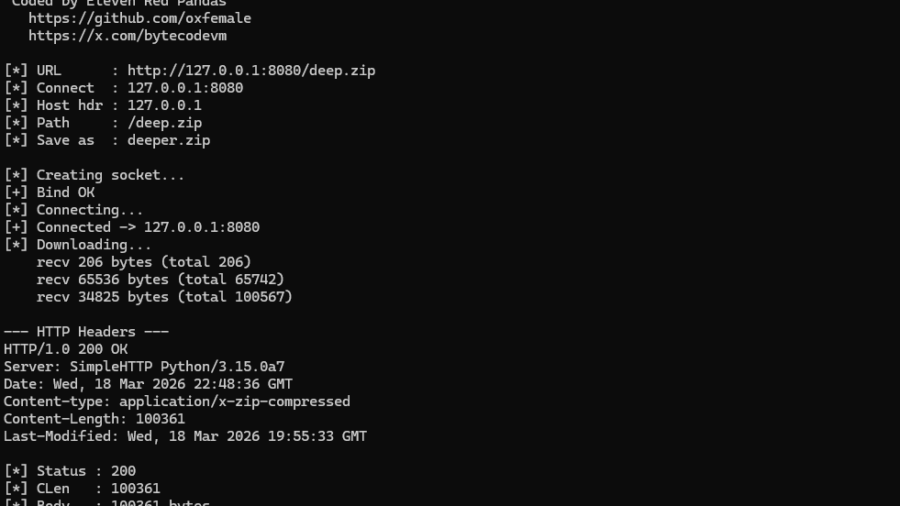
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
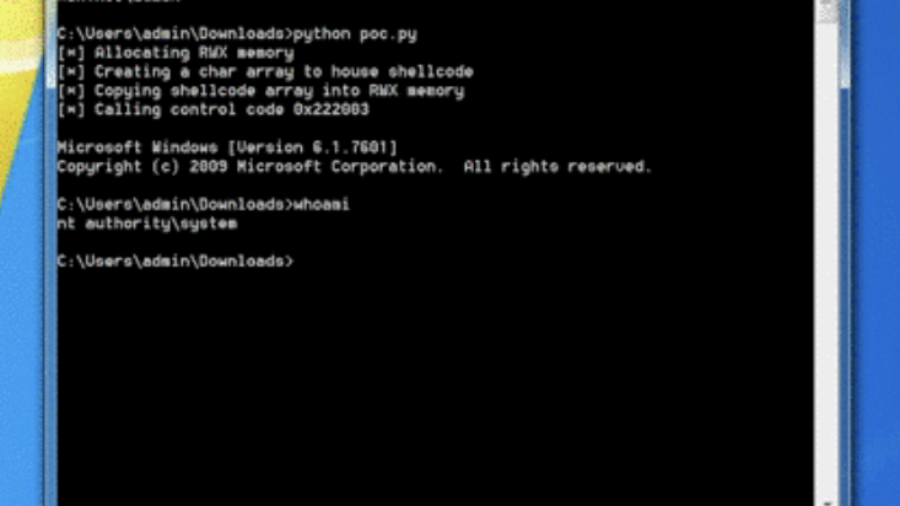
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
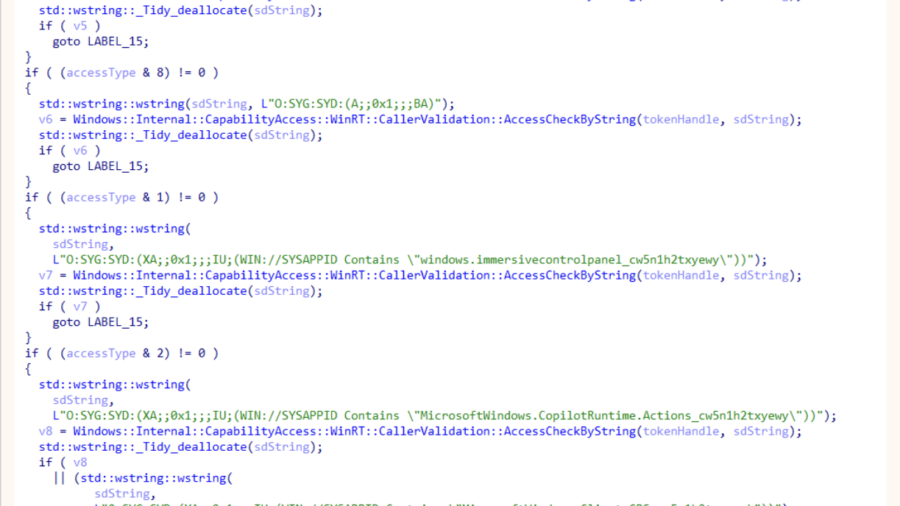
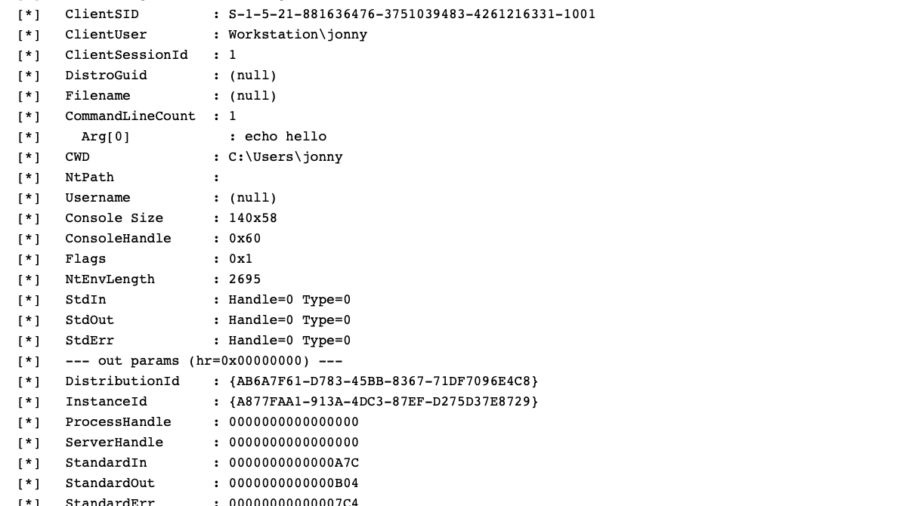
WSL, COM Hooking, & RTTI
The article demonstrates how to hook COM methods in Windows Subsystem for Linux by leveraging C++ RTTI metadata to reconstruct class layouts and locate virtual methods, enabling precise COM instrumentation without symbols.
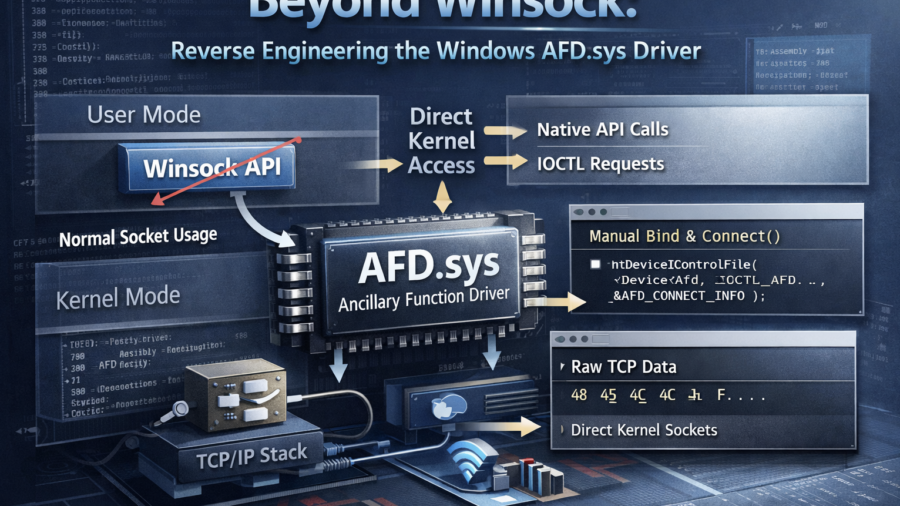
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.
Ghost in the PPL – LSASS Memory Dump
The article explains a technique for dumping memory from the protected LSASS process (PPL). It analyzes limitations of PPL protection and demonstrates how MiniDumpWriteDump and existing process handles can be used to extract credential data.
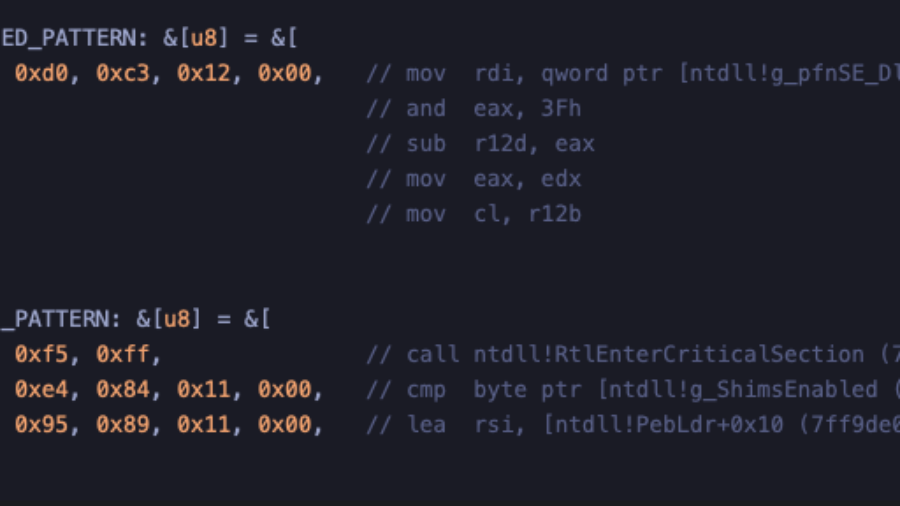
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
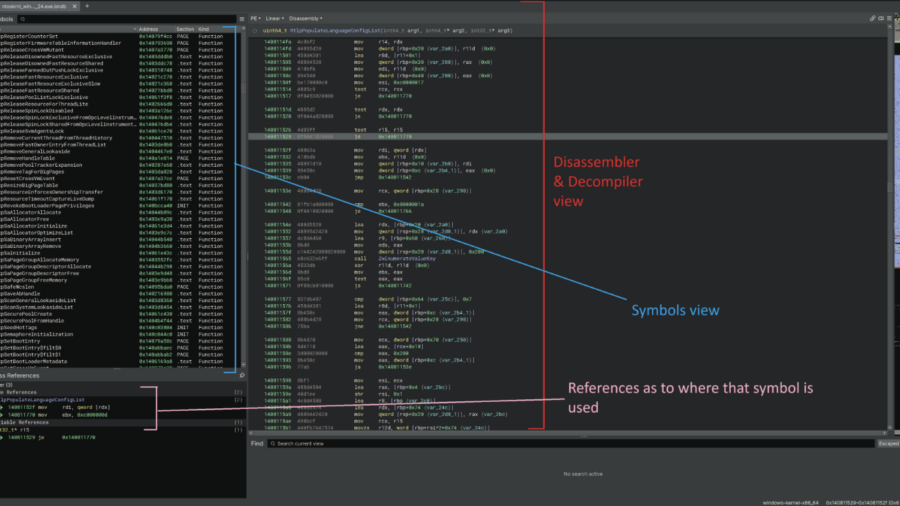
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
Defeating a 40-year-old copy protection dongle
Reverse engineering a vintage hardware copy-protection dongle used by 1980s enterprise software. By analyzing the DOS program and emulator environment, the author discovered the dongle check and bypassed it with a tiny patch.