“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
Windows Defender ACL Blocking: A Silent Technique With Serious Impact
The article analyzes a technique that disables Microsoft Defender by modifying file ACLs to block security services from accessing critical system DLLs. This silent method prevents Defender from starting without triggering obvious alerts.
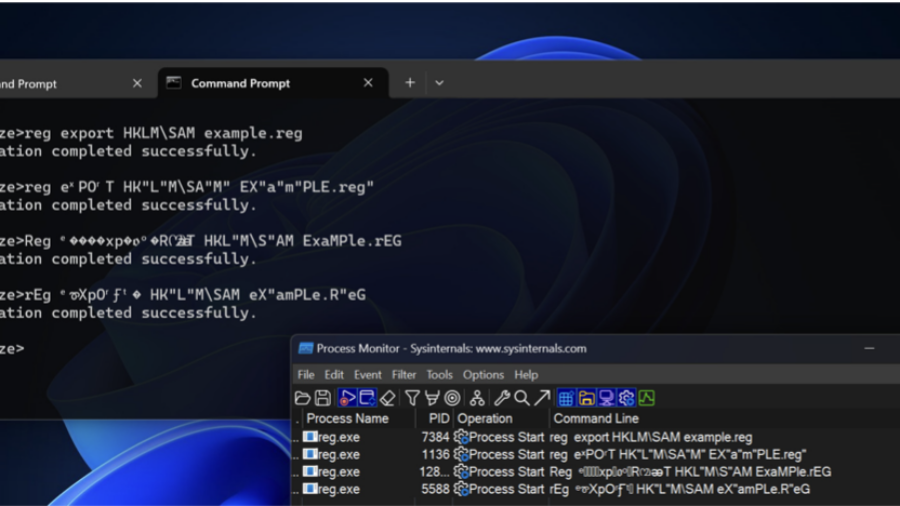
Bypassing Detections with Command-Line Obfuscation
How attackers can bypass AV and EDR detections by obfuscating command-line arguments. By exploiting parsing quirks in executables, small changes to parameters can hide malicious intent while the command still executes normally.
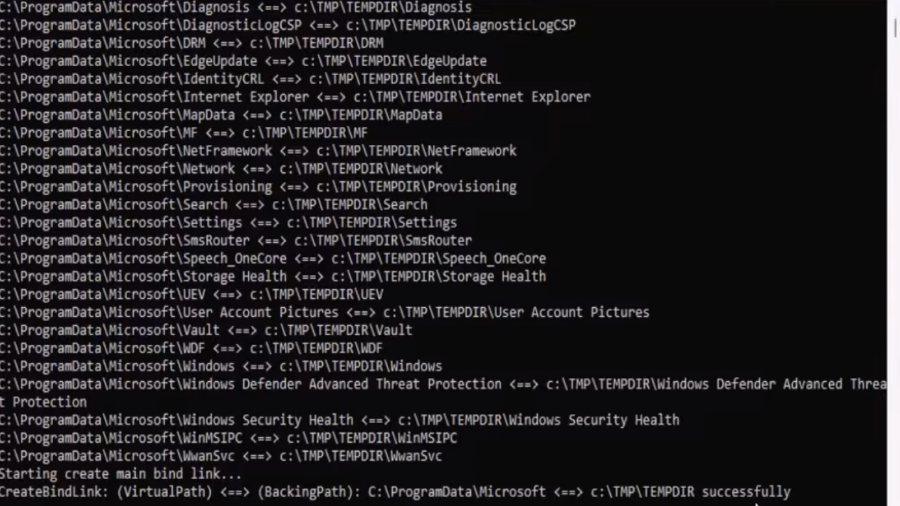
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
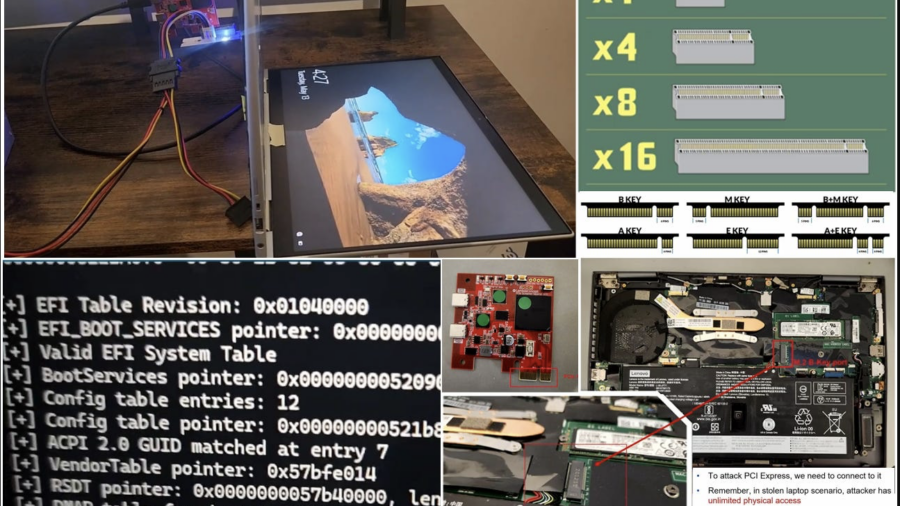
Hacking a stolen laptop: bypassing Windows security (BitLocker etc.) using PCI connector.
The article outlines security researcher Pierre-Nicolas Allard-Coutu’s demonstration of attacking a stolen Windows laptop using a PCIe connector to bypass protections like BitLocker, TPM, and Kernel DMA Protection, showing how to gain SYSTEM access.
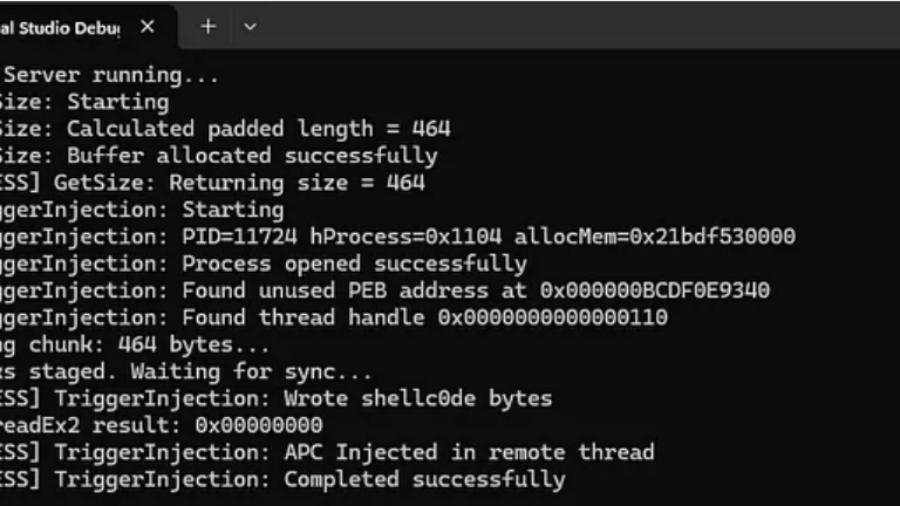
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
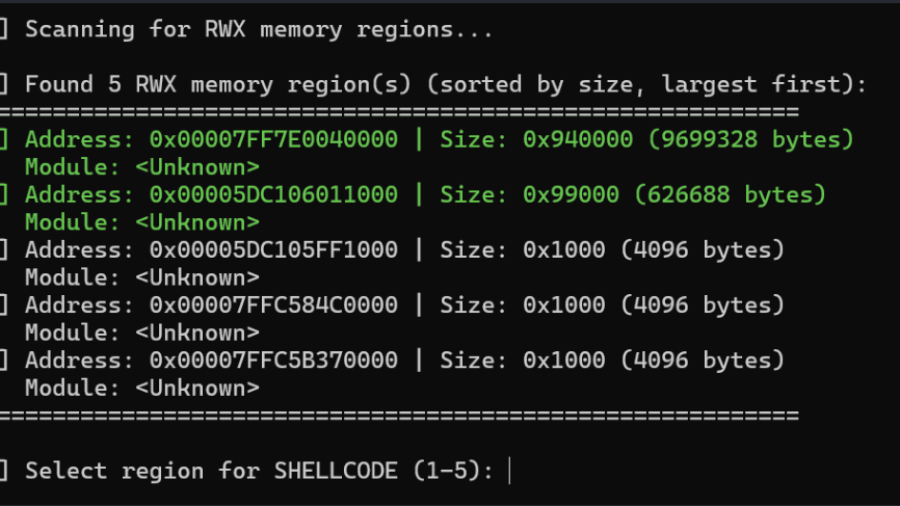
Living off the Process
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.
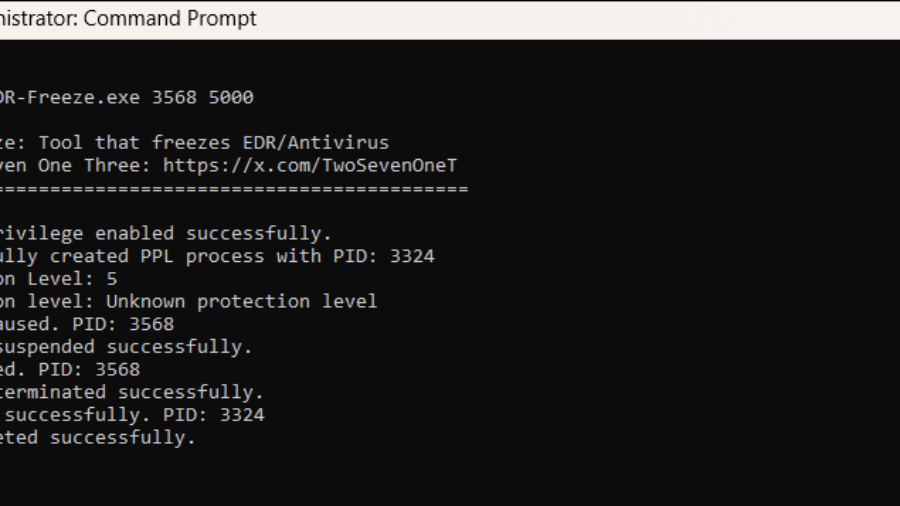
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.
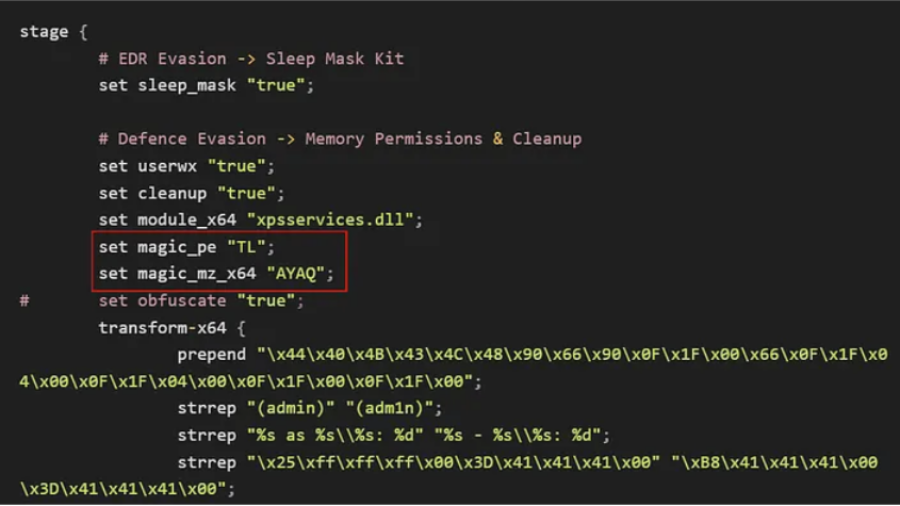
Bypassing Elastic EDR to Perform Lateral Movement
Article demonstrates how lateral movement can still be achieved in a lab with Elastic EDR and Microsoft ASR enabled by modifying payload delivery and execution techniques, bypassing common detection patterns and highlighting gaps in behavior-based defenses.
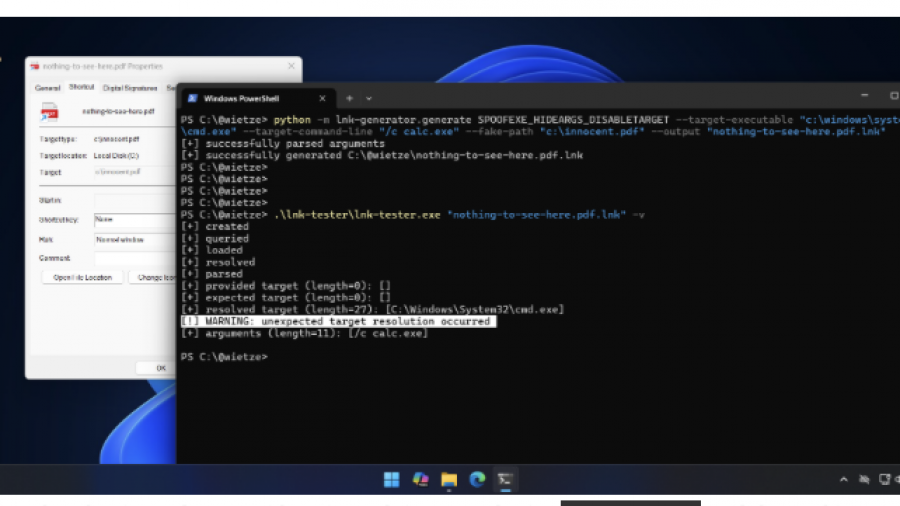
Trust Me, I’m a Shortcut
LNK shortcut abuse remains effective because shortcuts are trusted and rarely inspected. The technique enables stealthy execution and strong phishing scenarios. Its future use is likely in initial access and evasion until detection improves.