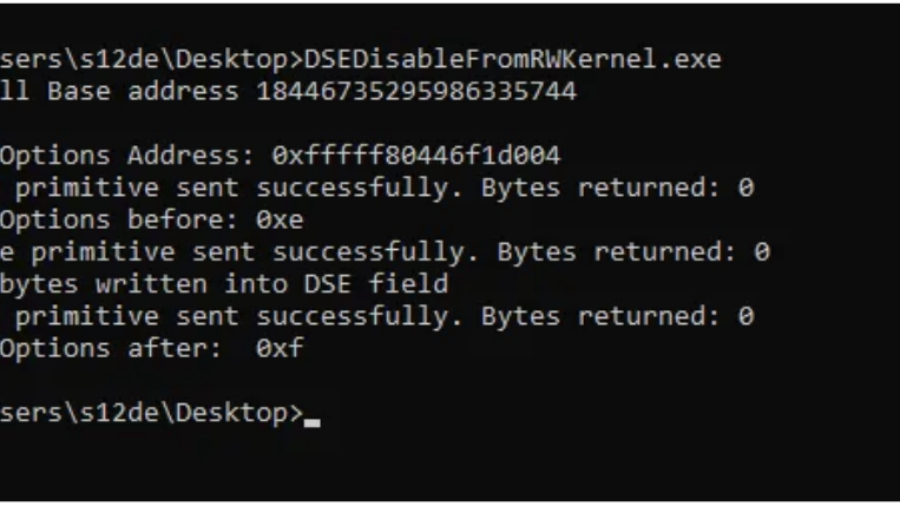
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
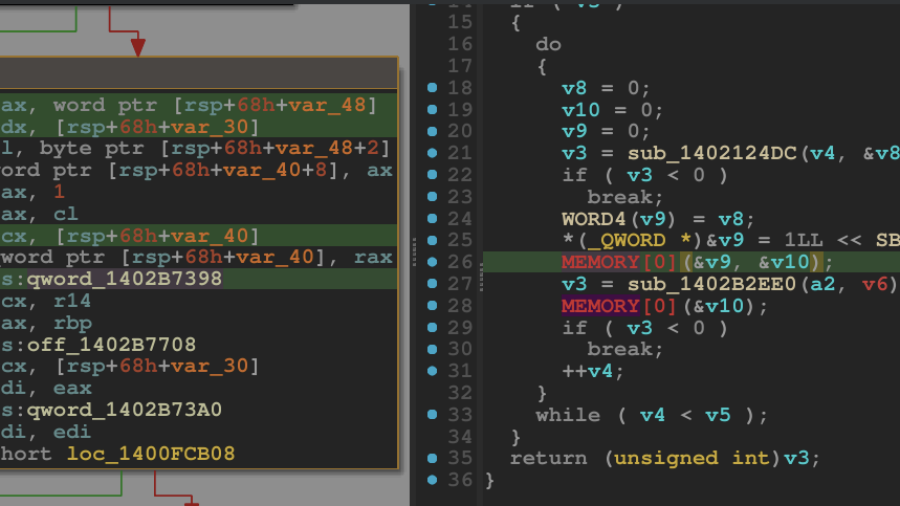
Breaking the Shield: Unpacking a VMProtected Windows Kernel Driver
A technical walkthrough showing how to unpack a VMProtected Windows kernel driver using WinDbg and dynamic analysis. The guide demonstrates restoring the hidden Import Address Table and dumping a clean driver for reverse engineering.
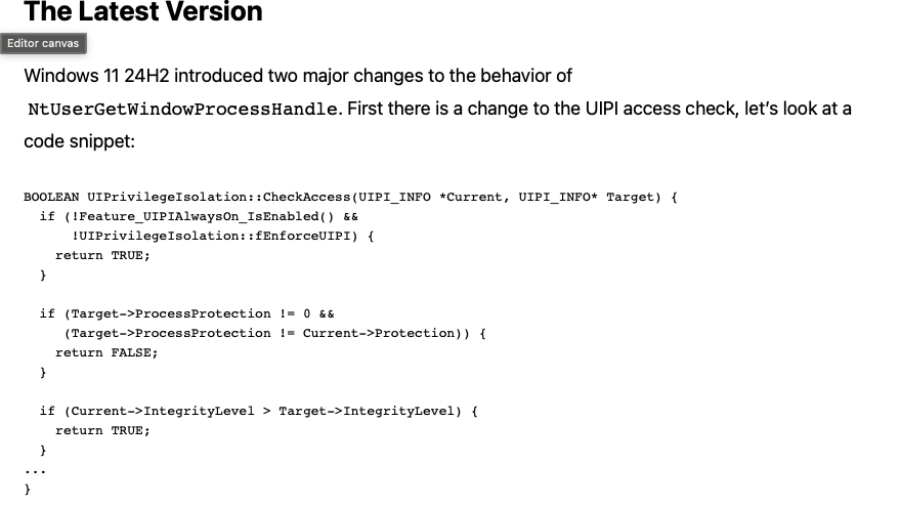
A Deep Dive into the GetProcessHandleFromHwnd API
The article analyzes the Windows GetProcessHandleFromHwnd API and its evolution from a hook-based implementation to a kernel Win32k function that could open powerful process handles, enabling security bypasses such as CVE-2023-41772.
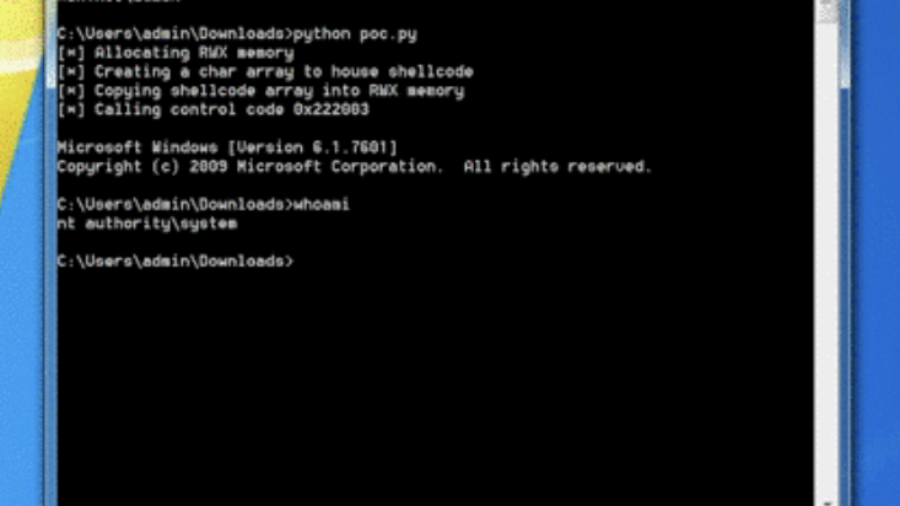
0x00 – Introduction to Windows Kernel Exploitation
The article introduces Windows kernel exploitation and explains how to build a research lab using tools like WinDbg and the HackSys Extreme Vulnerable Driver (HEVD) to study kernel vulnerabilities and exploit development.
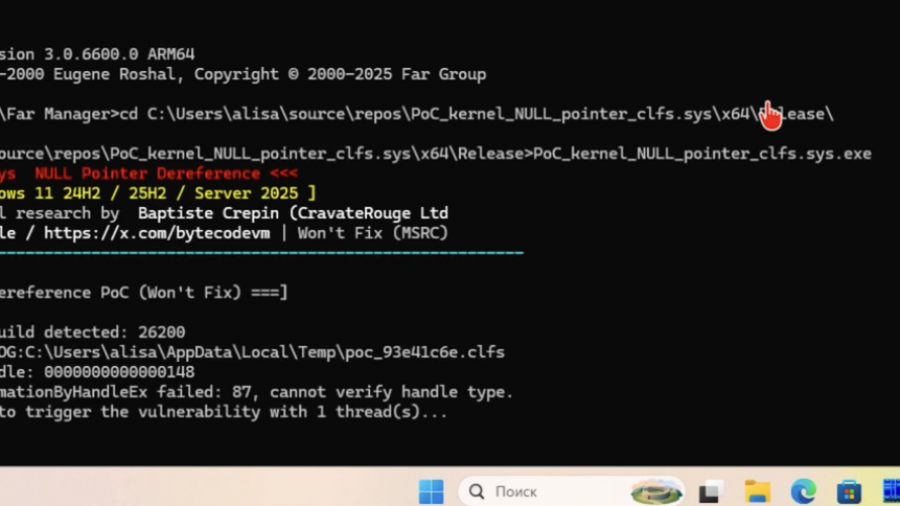
Won’t Fix: Kernel DoS in clfs.sys via NULL FastMutex Dereference
The article examines a Windows kernel bug in clfs.sys where a NULL pointer is dereferenced during fast mutex acquisition, causing a kernel crash and denial of service due to improper validation of a FAST_MUTEX pointer.
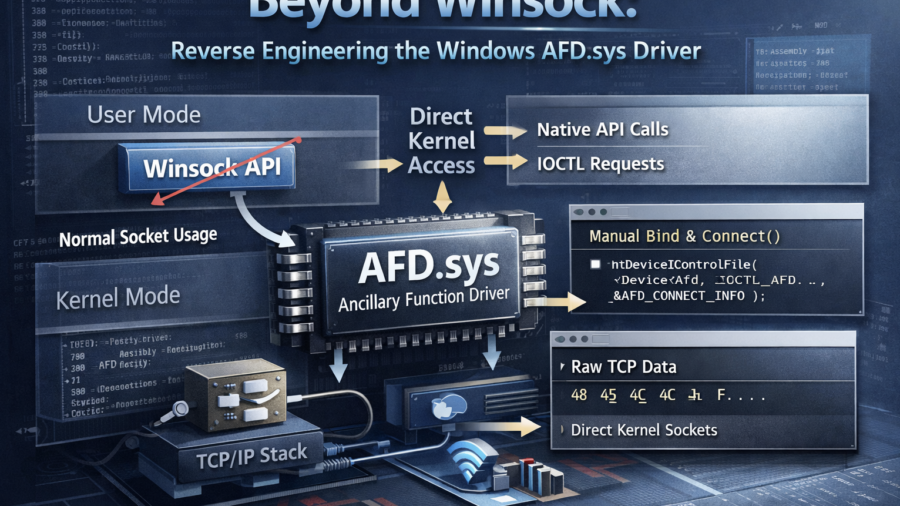
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.
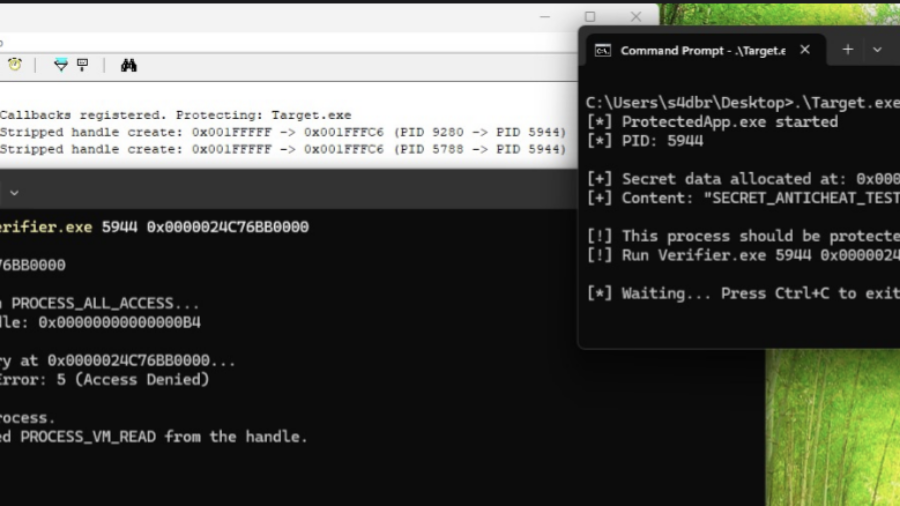
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
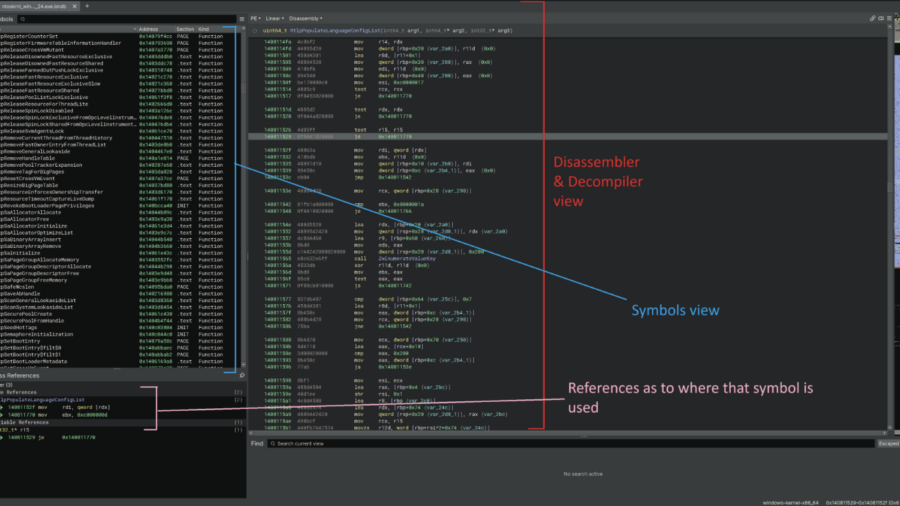
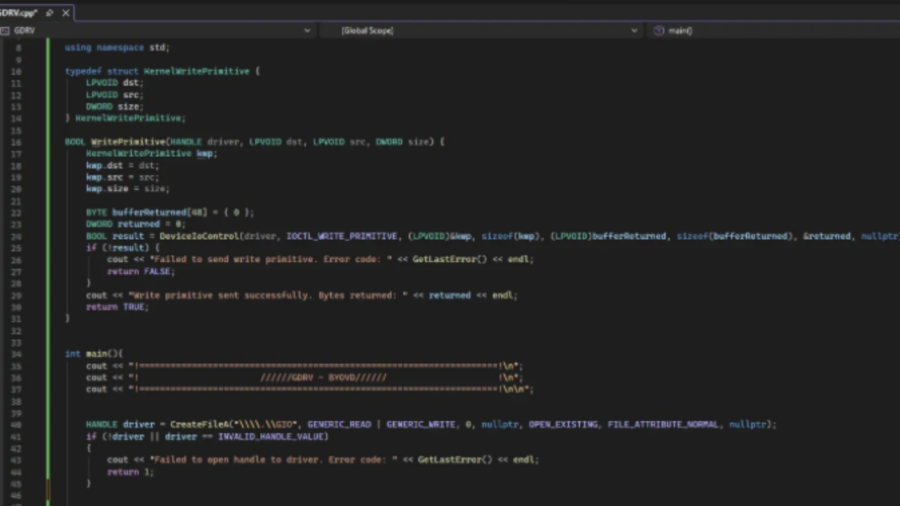
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.