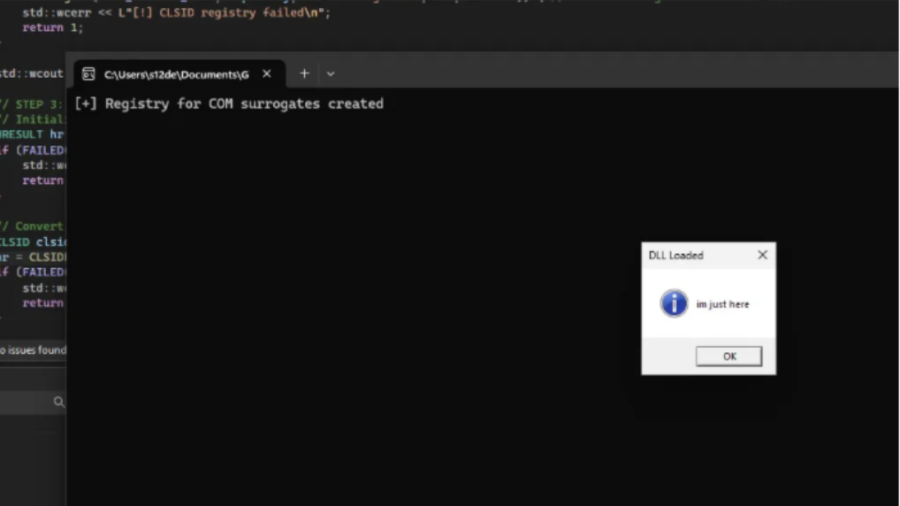
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
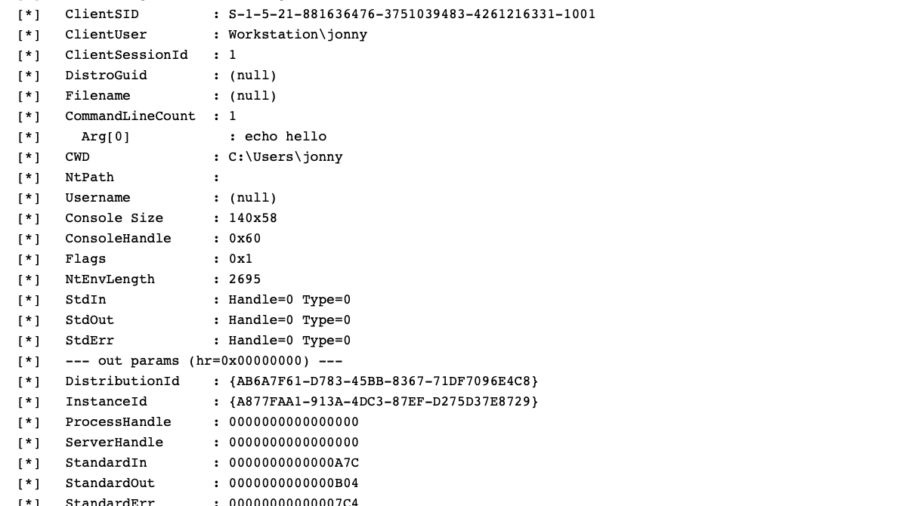
Inside WMI: Tracing Windows Management from Consumers to COM Providers
The article explains WMI internals, showing how Windows management queries travel from applications to the WMI service, repository, and provider hosts, and how COM/DCOM mechanisms execute underlying system operations.
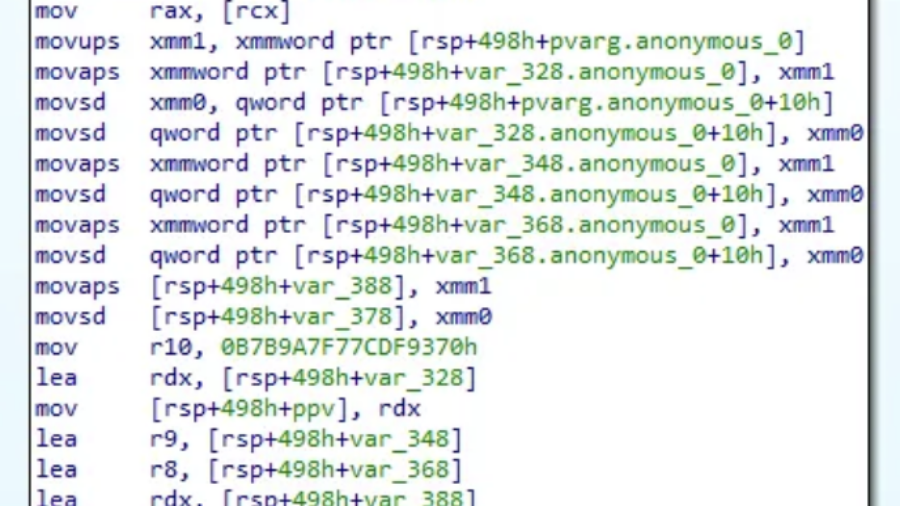
WSL, COM Hooking, & RTTI
The article demonstrates how to hook COM methods in Windows Subsystem for Linux by leveraging C++ RTTI metadata to reconstruct class layouts and locate virtual methods, enabling precise COM instrumentation without symbols.