The article shows a patchless AMSI bypass using Page Guard exceptions and VEH to intercept AmsiScanBuffer, force an early clean return, and avoid direct code patching.
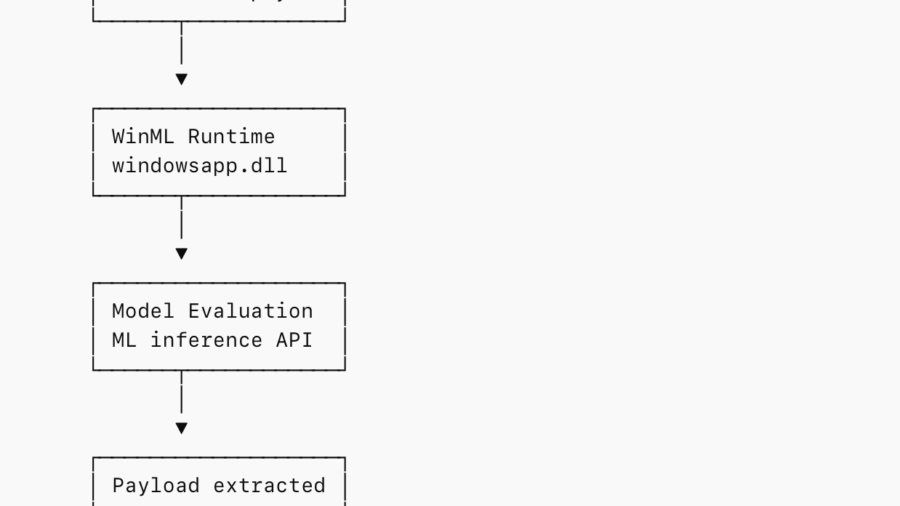
Abusing WinML for In-Memory Staging and EDR Evasion
The research shows how attackers can embed payloads inside ONNX ML models and load them via Windows WinML APIs, staging malware entirely in memory while blending into legitimate machine-learning application behavior.
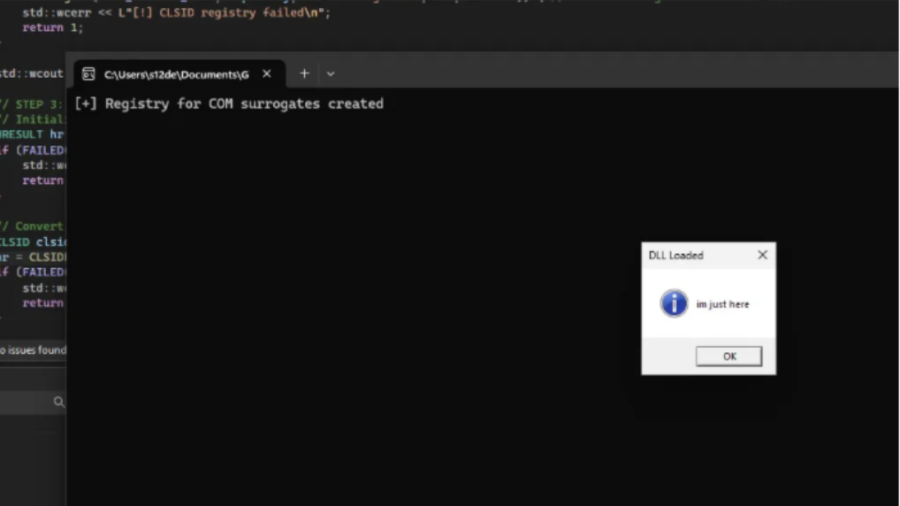
COMouflage: Stealthy DLL Surrogate Injection for Process Tree Evasion
COMouflage is a stealthy Windows injection technique that abuses COM DLL Surrogates to execute malicious DLLs inside dllhost.exe, making svchost.exe appear as the parent process and hiding the attacker’s process from detection.
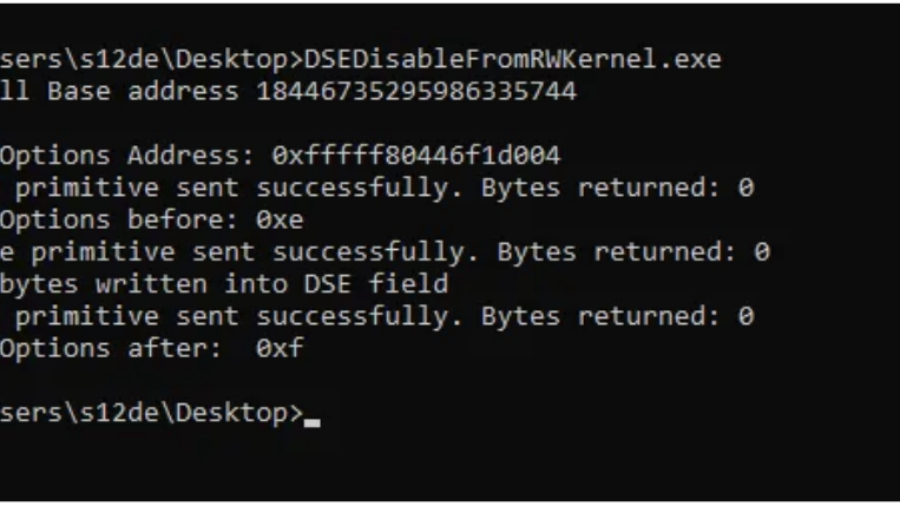
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
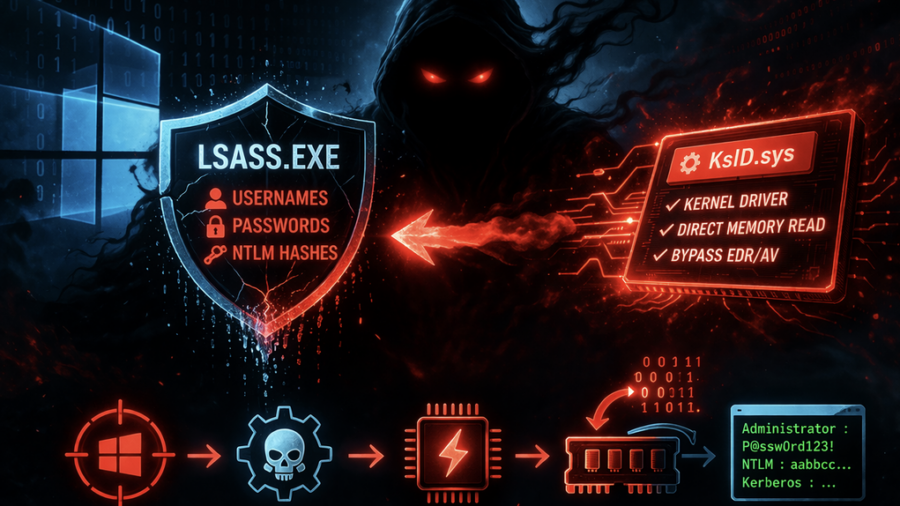
Ghost in LSASS: Inside the KslKatz Credential Dumping Framework
KslKatz is a Windows credential-dumping tool that reads LSASS memory using a kernel driver to bypass user-mode protections. It merges techniques from KslDump and GhostKatz to extract authentication secrets with improved stealth.
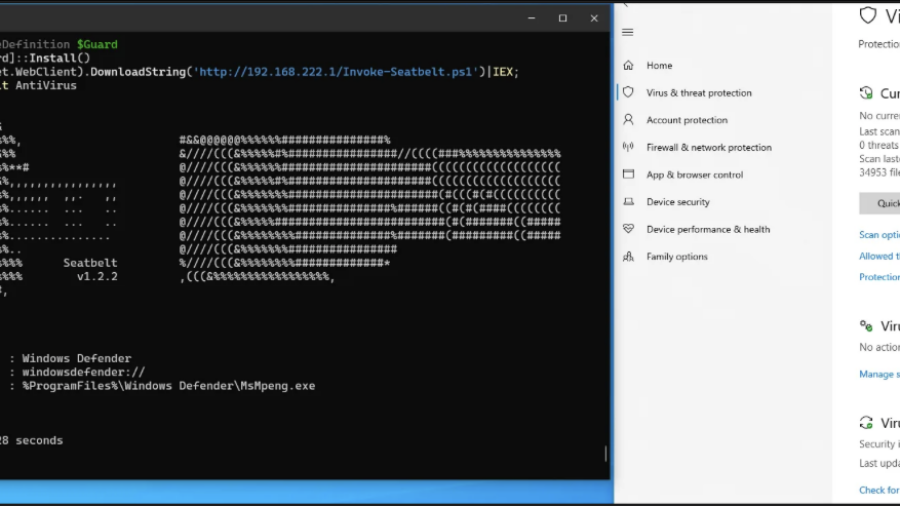
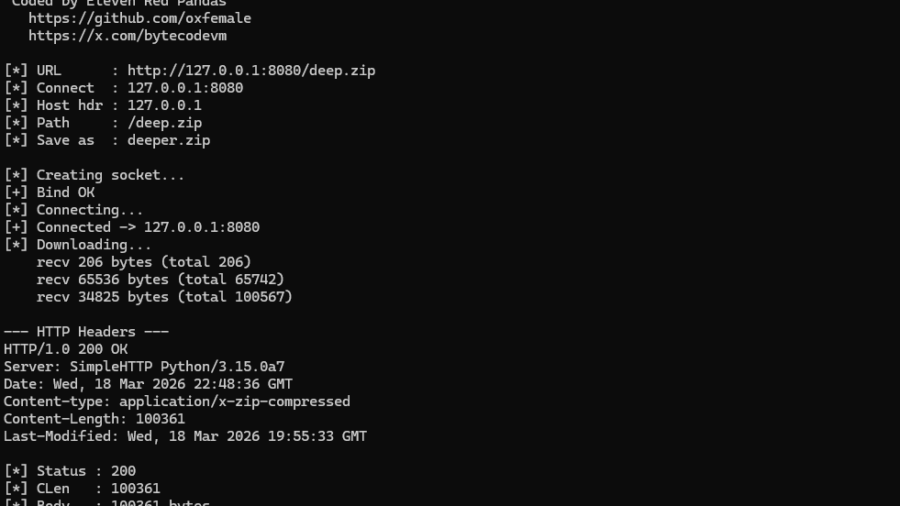
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
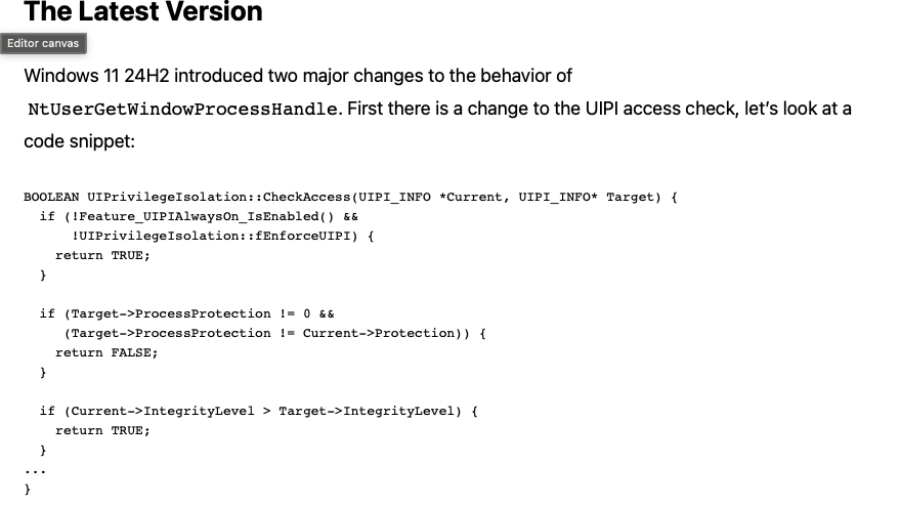
A Deep Dive into the GetProcessHandleFromHwnd API
The article analyzes the Windows GetProcessHandleFromHwnd API and its evolution from a hook-based implementation to a kernel Win32k function that could open powerful process handles, enabling security bypasses such as CVE-2023-41772.
LOLExfil: Stealthy Data Exfiltration Using Living-Off-the-Land Techniques
The article introduces LOLExfil, a Living-Off-the-Land data exfiltration technique that abuses legitimate system tools and trusted services to stealthily extract data, blending malicious activity with normal system behavior.
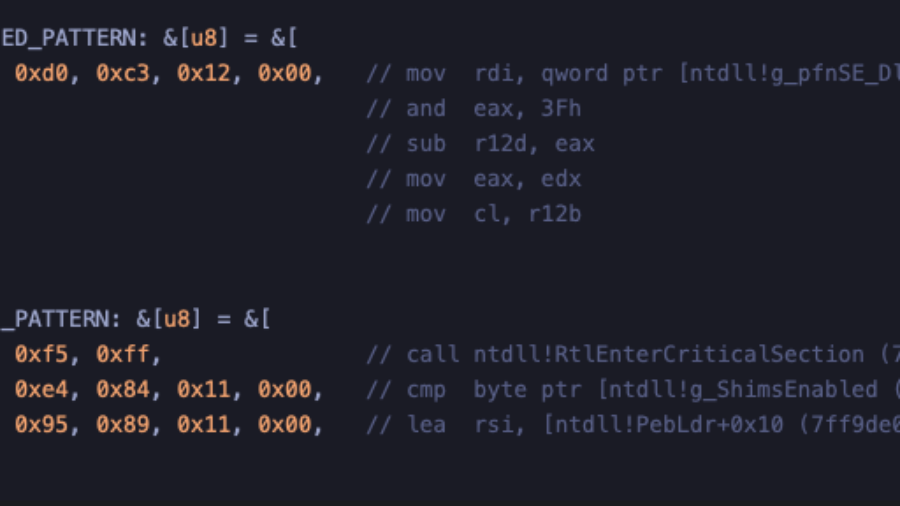
Crimes against NTDLL – Implementing Early Cascade Injection
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
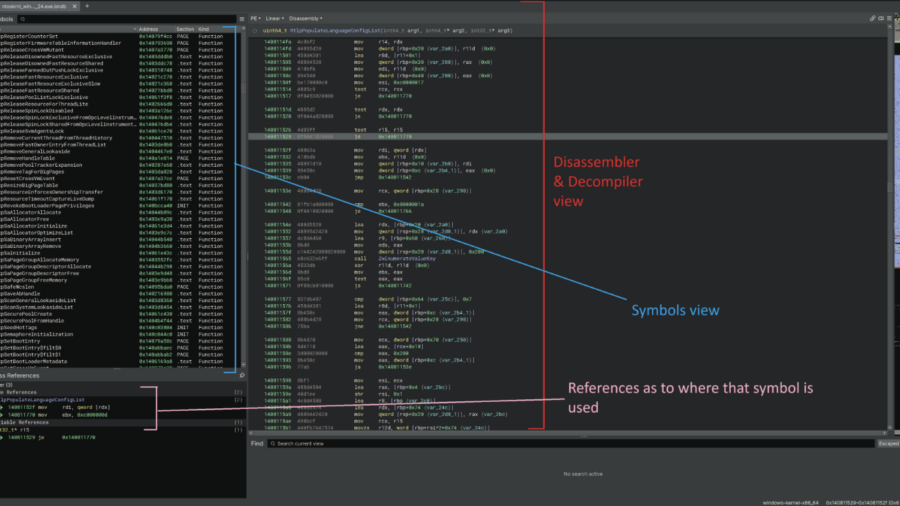
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.