Original text by Xeno Kovah
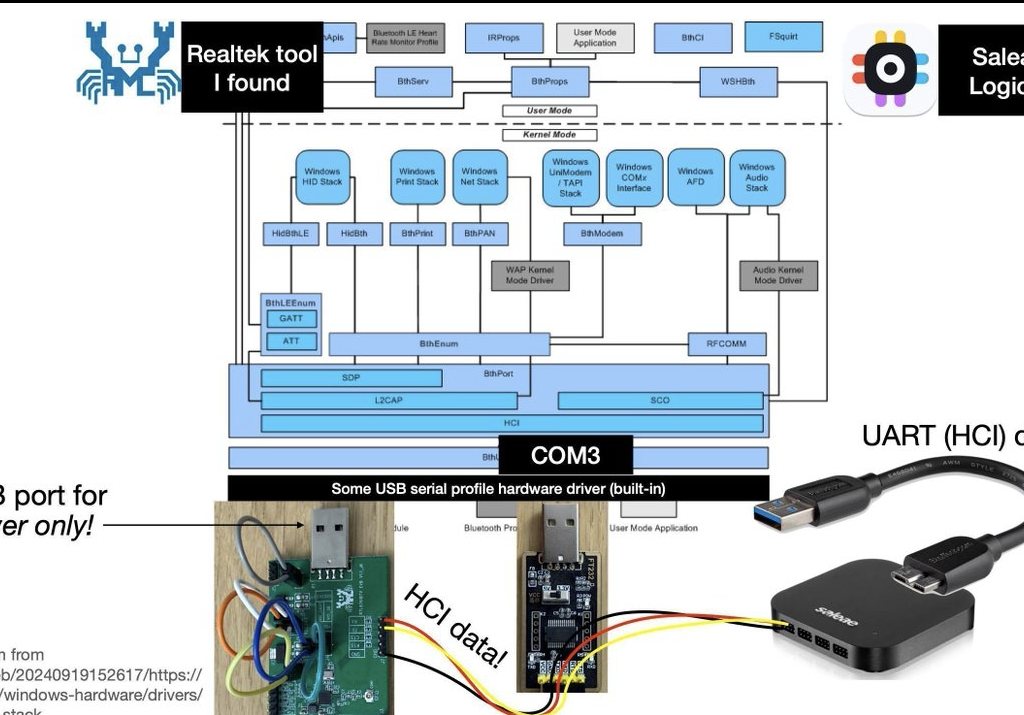
The article “Hardwear.io 2025 – Reverse Engineering Realtek Bluetooth Chips” from Dark Mentor describes research into undocumented Realtek Bluetooth chipsets commonly used in inexpensive USB adapters. The author investigated devices based on the RTL8761B chipset with the goal of enabling deeper Bluetooth security research without relying on expensive development boards. Because almost no public documentation exists for these chips, the work required reverse engineering their firmware, architecture, and update mechanisms. The research explains how the firmware operates on a mostly 16-bit MIPS-based system and how the vendor’s ROM-patching update process can be analyzed and modified. By studying this mechanism, the researcher demonstrated how firmware patches could be used to alter chip behavior, including spoofing Bluetooth device addresses and enabling the transmission of custom low-level Bluetooth protocol packets. These capabilities make inexpensive adapters useful tools for Bluetooth reconnaissance and vulnerability testing. The work highlights both the practical challenges of firmware reverse engineering and the broader security implications of poorly documented embedded hardware used in millions of devices.
https://darkmentor.com/2025-11-21_HardwearioNL2025_RTL8761B_RE_Slides_With_Builds.pdf
https://github.com/darkmentorllc/DarkFirmware_real_i
https://github.com/darkmentorllc/BT_Security_VSC_DB
Abstract
We hold this truth to be self-evident: SUFFERING BUILDS STRENGTH! In this talk I will walk you through the trials, tribulations, and triumph(!) of the worst debugging setup I’ve ever hacked together, which I used to reverse engineer the Realtek RTL8761B* family of Bluetooth chips.
This work was done because Bluetooth security tools are in an abominable state. We use “CSR4” (Cambridge Silicon Radio) dongles that don’t support packets newer than Bluetooth 4.0 (released in 2010!), just to be able to spoof the Bluetooth Device Address (BDADDR) for MitM attacks.
Veronica Kovah & I have been creating Bluetooth security classes for OpenSecurityTraining2. And we wanted to use better hardware; ideally something that supports BT 5.4 (released in 2023). So I bought a bunch of cheap dongles off Amazon, and found that most of them used the same RTL8761B chip. So the goal was clear: at a minimum, figure out a way to spoof the BDADDR on these dongles. But I also a set out a nice-to-have stretch goal – to figure out how to use these dongles to send custom LMP packets (which are architecturally not meant to be under full user control.) That way, could replace a bulky and expensive $55 dev board (that is only used for BT Classic), with a cheap and small $14 USB dongle (which has a better antenna to boot!) This would make Blue2thprinting (released at Hardwear.io 2023), and thus Bluetooth reconnaissance & vulnerability assessment, cheaper & better.
Bloodied (but not broken) by the ordeal, I achieved my goals and stretch goals. And given that there are no public descriptions of how Realtek Bluetooth chips work, I look forward to sharing hitherto-unknown information about how to navigate and understand these mostly-16-bit-MIPS-code systems. And I’ll discuss how their ROM-“patch”ing firmware update mechanism works, how you can patch it to change its code too, and the security implications thereof.
Purpose of this repository
This repository contains information about Bluetooth HCI Vendor-Specific Commands (VSCs) which are known to be security-relevant, as found across different vendors. The currently tracked VSC types of security interest are given below, along with a description of why they are security-relevant. It also documents the Vendor-Specific Events (VSEs) and their formats (when known), which are returned by a controller after a VSC is received.
- Read Controller Registers
- Write Controller Registers
- Read Controller RAM
- Write Controller RAM
- Read Controller ROM
- Write Controller ROM Patches
- Read Controller Non-volatile Memory (e.g. SPI NOR Flash)
- Write Controller Non-volatile Memory (e.g. SPI NOR Flash)
- Set Bluetooth Classic / BLE Public BD_ADDR
- Set TX power level
- Send arbitrary LMP packets
- Send arbitrary LLCP packets
These are not all possible security-relevant VSCs, but they are some of those most commonly found across chip-makers.
Known VSCs, organized by vendor
- Broadcom
- Cambridge Silicon Radio (CSR)
- Cypress (Purchased by Infineon)
- Espressif
- Realtek
- Silicon Labs
- Texas Instruments