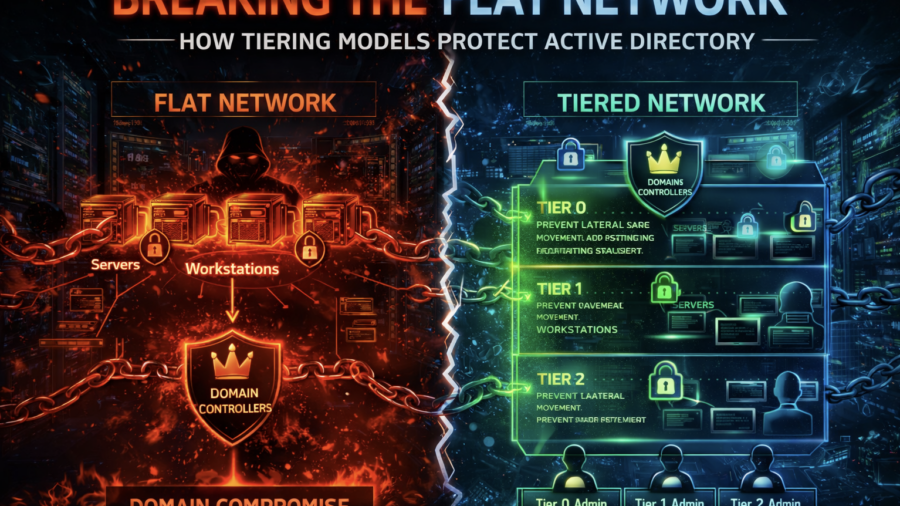
The article explains how flat enterprise networks enable easy lateral movement and domain compromise. It shows how Active Directory tiering models segment privileges and systems to prevent attackers from escalating access.
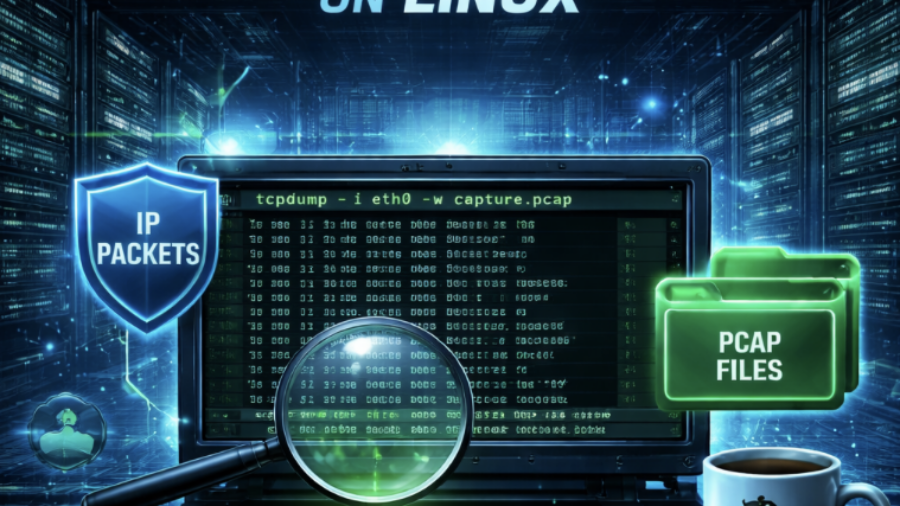
From PCAP to Passwords: Automating Kerberos Roast Extraction
Krb5RoastParser is a Python tool that extracts Kerberos authentication hashes from PCAP traffic and converts them into Hashcat-compatible formats, simplifying Kerberoasting and Kerberos password-cracking workflows.