The article explains how to set up Windows kernel debugging over a network using WinDBG and a host/target configuration. It covers enabling debug mode, connecting WinDBG to a remote VM, and using kernel debug infrastructure for low-level inspection and manipulation.
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
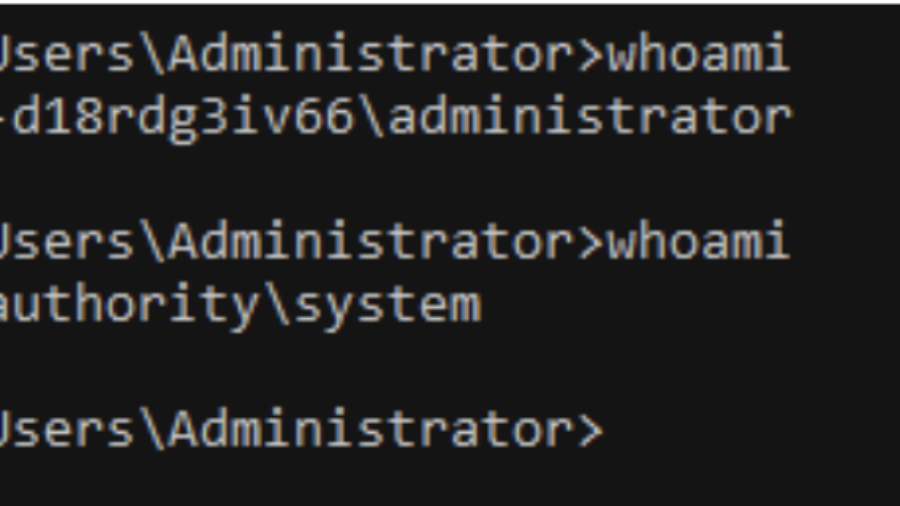
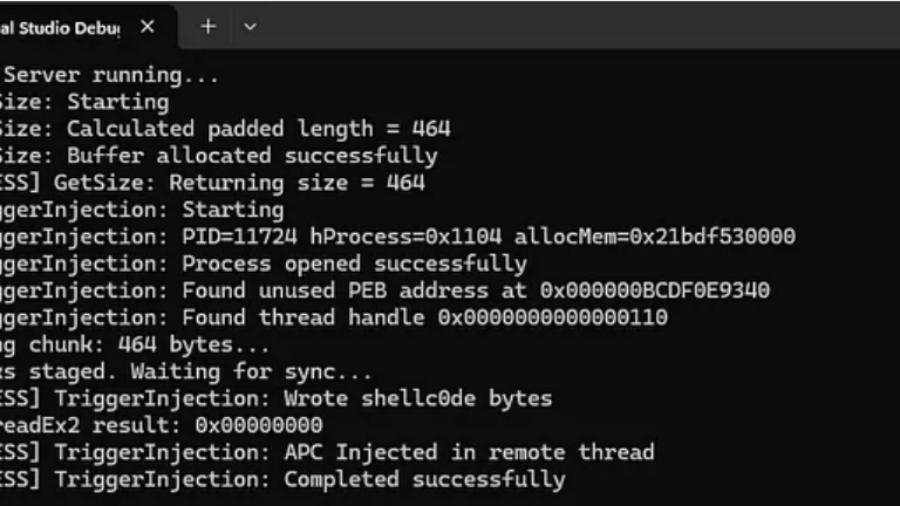
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
Living off the Process
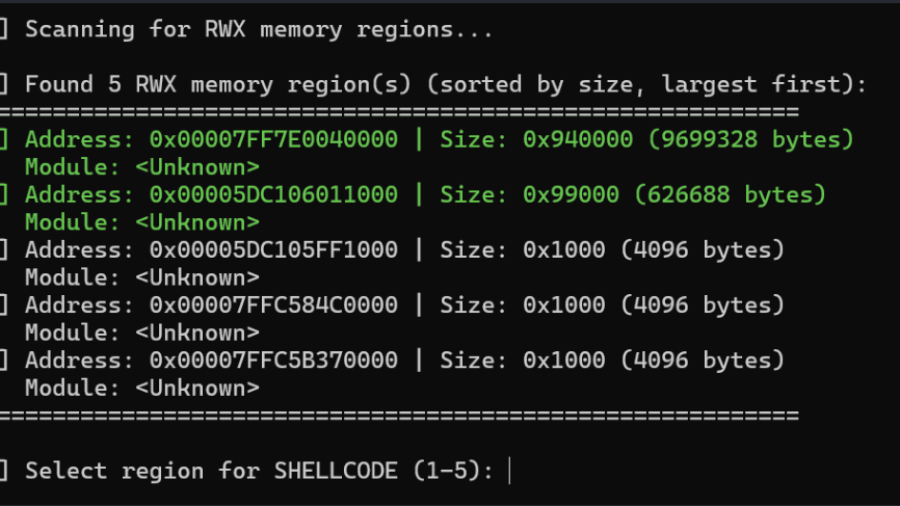
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
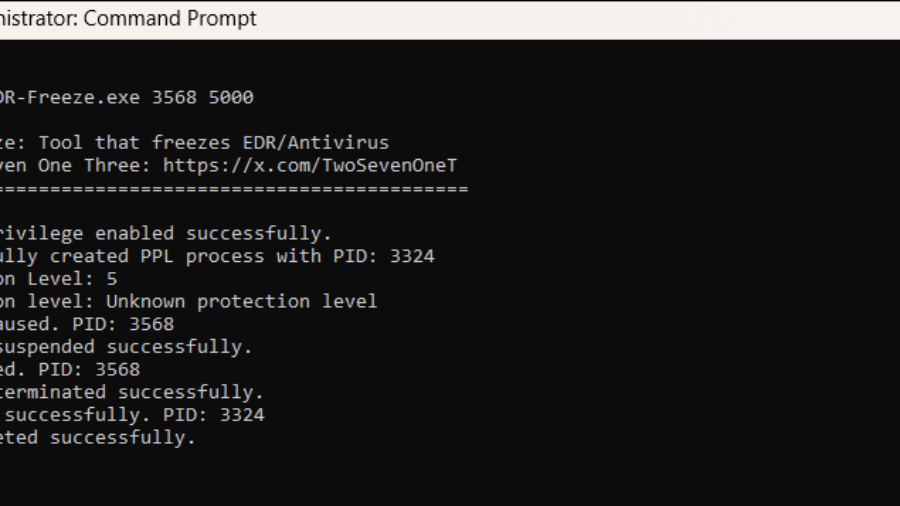
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.
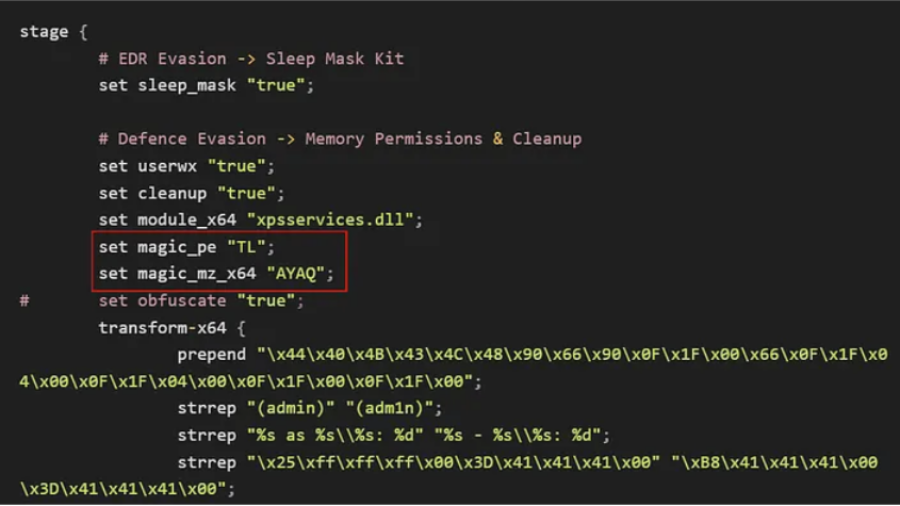
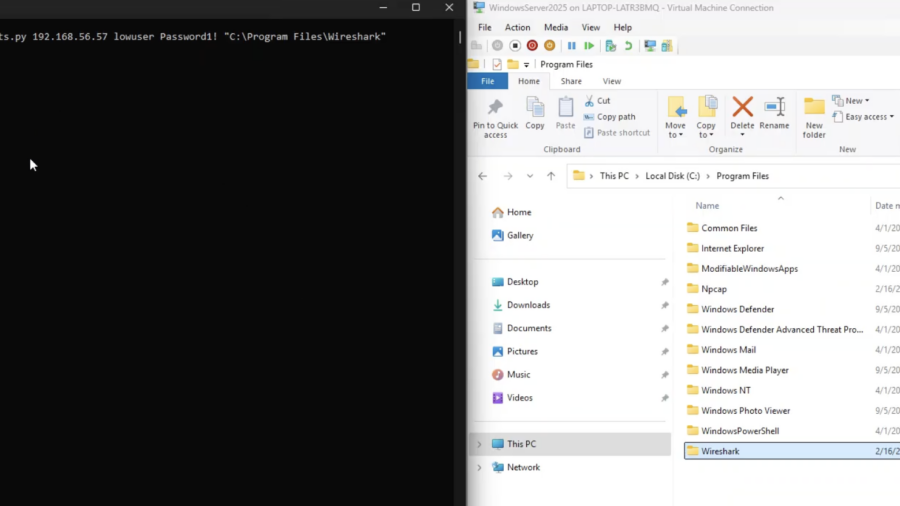
Bypassing Elastic EDR to Perform Lateral Movement
Article demonstrates how lateral movement can still be achieved in a lab with Elastic EDR and Microsoft ASR enabled by modifying payload delivery and execution techniques, bypassing common detection patterns and highlighting gaps in behavior-based defenses.
EventLog-in: Propagating With Weak Credentials Using the Eventlog Service in Microsoft Windows (CVE-2025-29969)
SafeBreach Labs disclosed a critical RCE in the MS-EVEN RPC service (CVE-2025-29969) that lets low-privilege users write arbitrary files remotely on Windows 11/Server 2025, bypassing share limits. Patched May 2025.
Website Update: Enhancing Security and Performance
server global update
ALPC Uncovered: The Hidden Backbone of Local RPC in Windows 11 and Server 2025
This article explores ALPC in Windows 11 and Windows Server 2025, covering hardened server design, message attributes, section-based transfer, and its role in Local RPC. It also analyzes ALPC as a security boundary and attack surface.
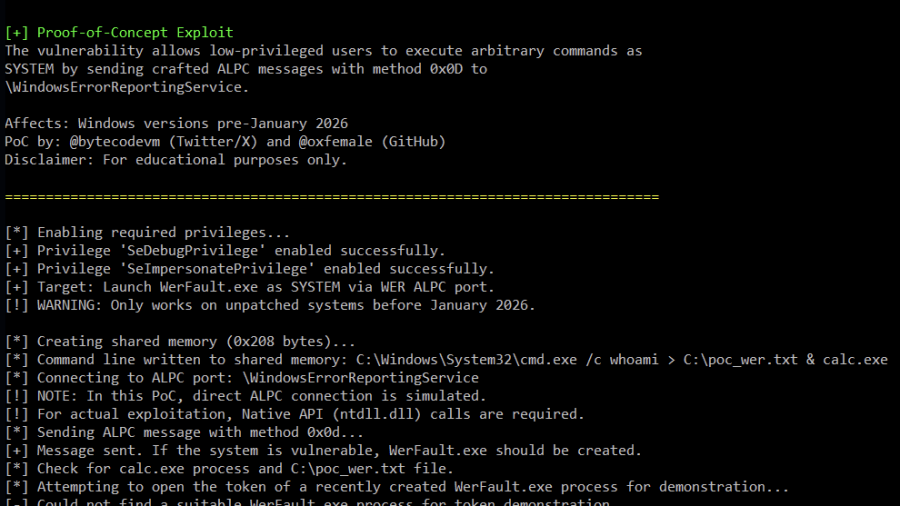
Analysis of Improper Authorization in Windows Error Reporting CVE-2026-20817 (PoC)
Proof-of-Concept (PoC) for CVE-2026-20817, a local privilege escalation vulnerability in the Windows Error Reporting (WER) service. The vulnerability allows an authenticated low-privileged user to execute arbitrary code with SYSTEM privileges by sending specially crafted ALPC messages to the WER service.
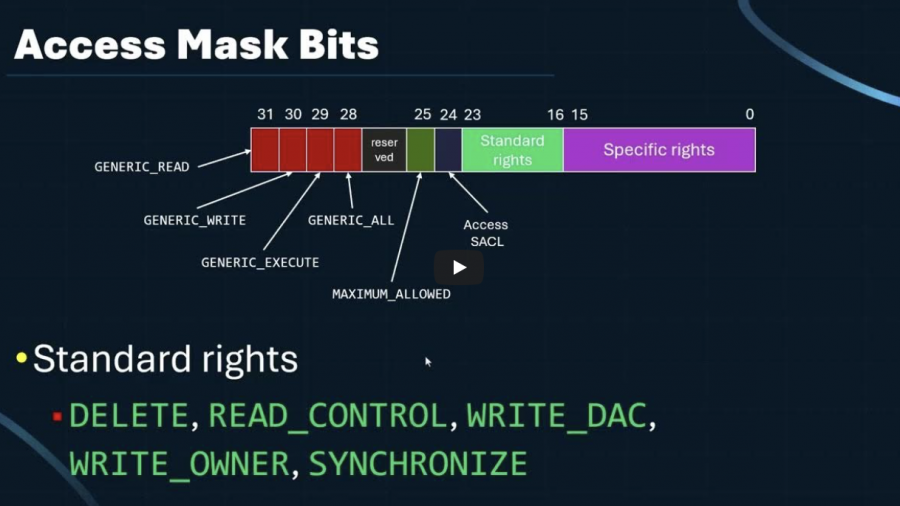
Looking into Windows Access Masks
Access masks are 32-bit permission values defining what operations a handle or security descriptor allows. The article breaks down standard, specific, and generic rights, explains ACE usage, and shows how Windows enforces access checks internally.