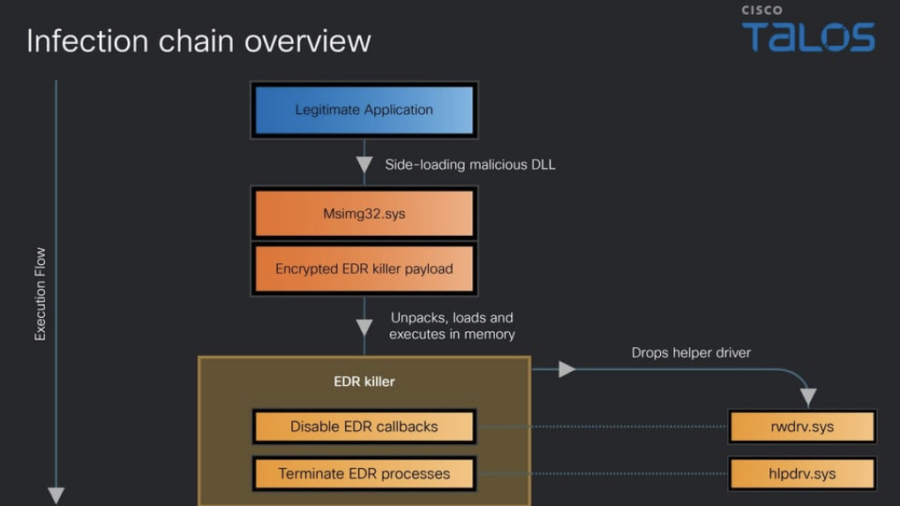
Cisco Talos analyzes a Qilin ransomware EDR-killer that disables over 300 security drivers. The multi-stage malware uses obfuscation and kernel-level techniques to bypass endpoint defenses and hide attacker activity.
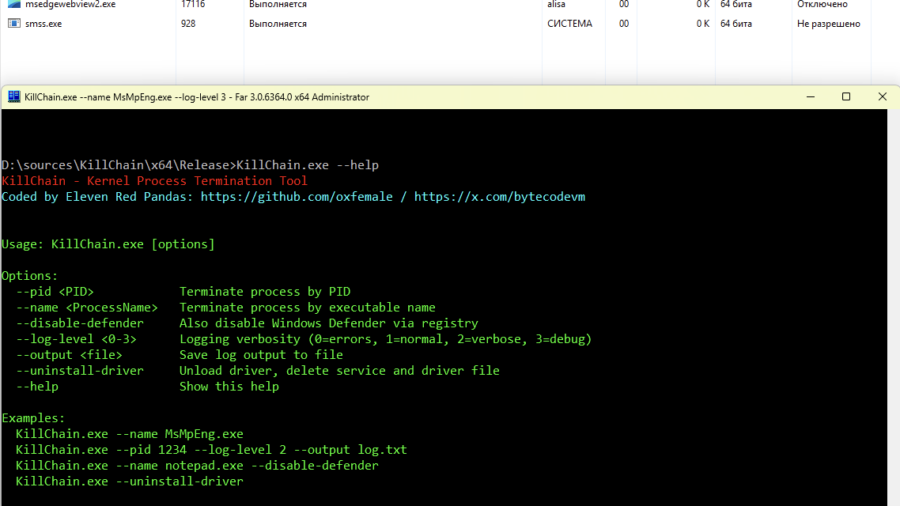
Breaking Process Protection: Exploiting CVE-2026-0828 in ProcessMonitorDriver.sys
The KillChain exploit leverages a vulnerability in ProcessMonitorDriver.sys (CVE-2026-0828) by abusing an exposed IOCTL that allows a user-mode application to terminate arbitrary processes — including protected system services — effectively bypassing standard Windows security checks.
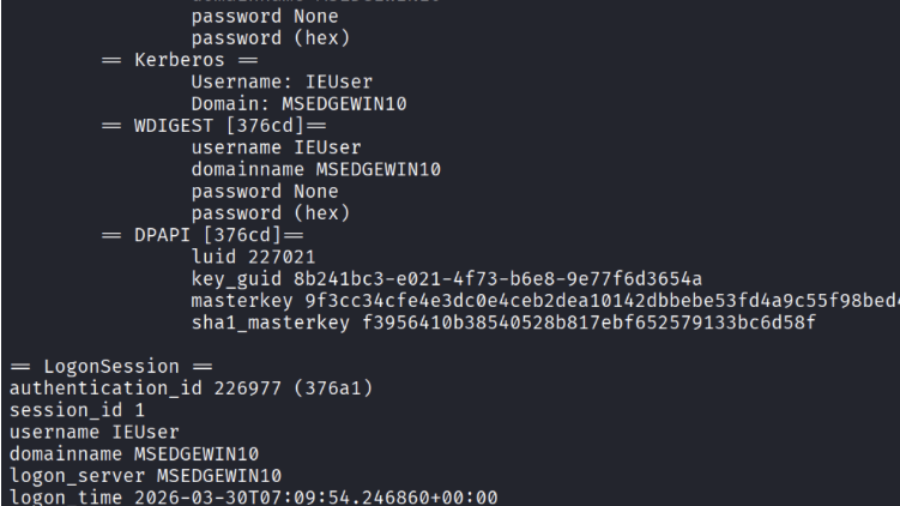
Credential Dumping from LSASS (Windows Authentication Secrets)
The article explains how attackers dump credentials from the Windows LSASS process using tools like Mimikatz and ProcDump, extracting password hashes and Kerberos tickets that enable privilege escalation and lateral movement.
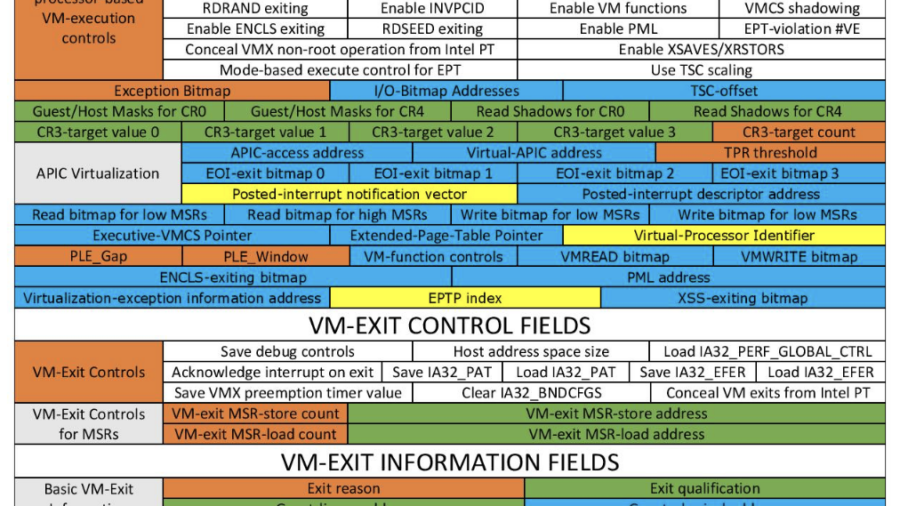
Hypervisor-Based Defense (Windows Kernel Protection)
The article explains how a defensive hypervisor can protect Windows systems from kernel attacks such as BYOVD by monitoring memory and enforcing protections below the OS using Intel VT-x and EPT virtualization features.
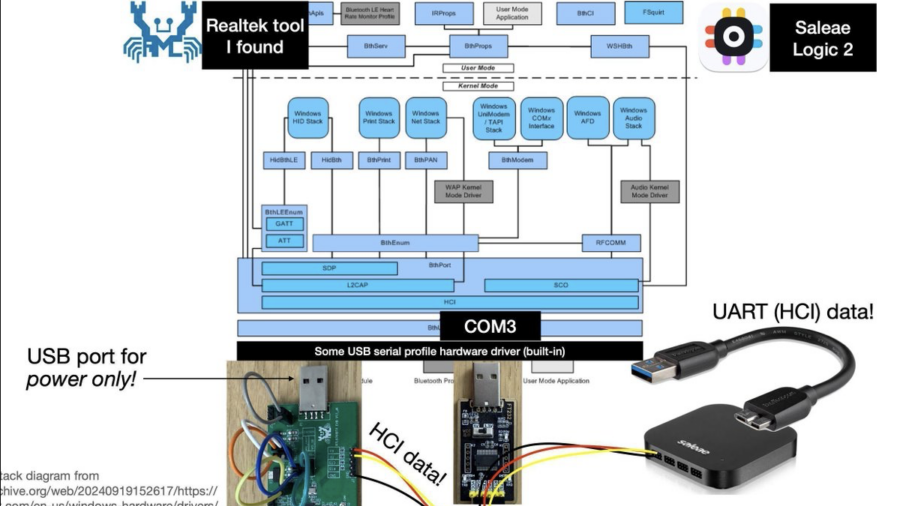
Reverse engineering Realtek RTL8761B* Bluetooth chips, to make better Bluetooth security tools & classes
Bloodied (but not broken) by the ordeal, I achieved my goals and stretch goals. And given that there are no public descriptions of how Realtek Bluetooth chips work, I look forward to sharing hitherto-unknown information about how to navigate and understand these mostly-16-bit-MIPS-code systems. And I’ll discuss how their ROM-“patch”ing firmware update mechanism works, how you can patch it to change its code too, and the security implications thereof.
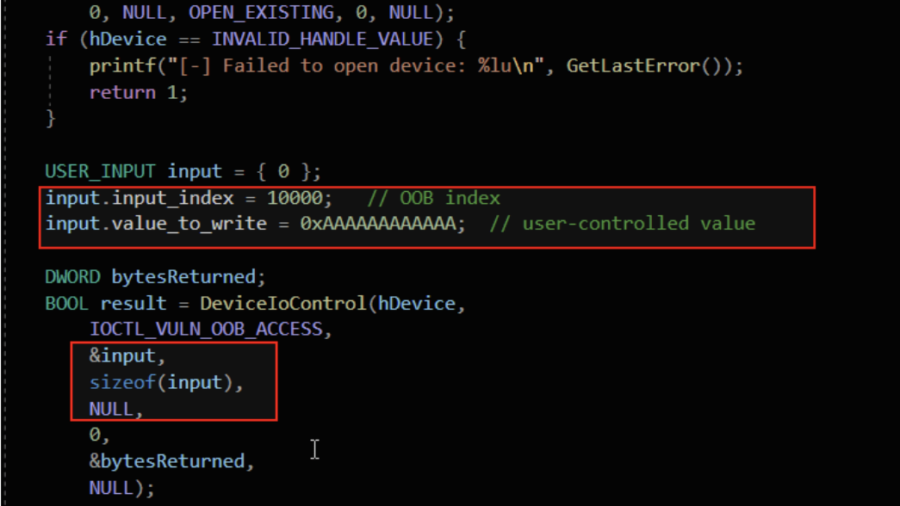
Understanding Out-Of-Bounds in Windows Kernel Driver
The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
MAD Bugs: Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
Researchers showed that the Claude AI model could generate a working exploit for a FreeBSD kernel vulnerability (CVE-2026-4747), producing a remote root shell by building a stack overflow and ROP chain with minimal human guidance.