Original text by Grzegorz Wypych (h0rac)
The article explains how security researchers can discover vulnerabilities that hide not in the main application binary but inside the shared libraries it depends on. The author presents the concept behind the ByteRay vulnerability hunting engine, which focuses on tracking how input data flows across program boundaries—from the main binary into external libraries where dangerous operations may occur. One of the key challenges in this type of analysis is identifying the relationship between sources (user-controlled input) and sinks (potentially unsafe operations) when they are located in different binaries. Traditional static analysis often fails to detect these issues because library code is analyzed separately or lacks proper context. ByteRay addresses this by performing cross-binary analysis and tracing the actual execution paths that propagate data into library functions. This approach allows researchers to uncover subtle vulnerabilities that remain hidden during normal audits. The article demonstrates how analyzing dependencies and following real data flows can reveal security flaws embedded deep inside commonly used libraries, emphasizing that vulnerabilities frequently reside in code that developers rarely inspect.
Today I would like to describe how ByteRay vulnerability hunting engine is able to detect bugs in shared libraries that main binary uses. One of the biggest problem of this kind of analysis is to find connection between sources and sinks in main library and shared library.
For demonstration how powerful is the engine I will provide example of two vulnerable libraries for stackoverflow vulnerability. Because it is example we should view it from source and compiled binary perspective.
Following code snippets include our vulnerable libraries and main code.
// main_static.c
#include <stdio.h>
#include <string.h>
#include "libsink.h"
#include "libmemcpy_overflow.h"
// Source = argv[1] albo stdin
int main(int argc, char **argv)
{
char input[256];
if (argc > 1) {
// Source: argv[1]
const char *user_data = argv[1];
int user_len = strlen(user_data);
// Old sink (strcpy overflow)
dangerous_sink(user_data);
// New sink (memcpy overflow)
memcpy_overflow_sink(user_data, user_len);
} else {
// Source: stdin
printf("Enter some text: ");
fflush(stdout);
if (fgets(input, sizeof(input), stdin) == NULL) {
return 1;
}
// remove newline
input[strcspn(input, "\n")] = '\0';
int user_len = strlen(input);
// Old sink (strcpy overflow)
dangerous_sink(input);
// New sink (memcpy overflow)
memcpy_overflow_sink(input, user_len);
}
return 0;
}/libmemecpy_overflow.c
#include <stdio.h>
#include <string.h>
// Stack overflow via tainted length in memcpy
void __attribute__((noinline))
memcpy_overflow_sink(const char *user_input, int user_size)
{
char local[16];
// BUG: user-controlled length
memcpy(local, user_input, user_size);
// Prevent optimization
printf("Copied: %s (len=%d)\n", local, user_size);// libsink.c
#include <string.h>
#include <stdio.h>
#include "libsink.h"
// Sink in libarry .so
void __attribute__((noinline)) dangerous_sink(const char *user_data)
{
char buf[16];
// Overflow
strcpy(buf, user_data);
// avoid compilation optimization
printf("Copied data: %s\n", buf);
}After compilation we will get 3 files and main binary will include both libraries + standard libc
readelf -d main_static2-aarch64-linux-gnu
Dynamic section at offset 0xfda8 contains 28 entries:
Tag Type Name/Value
0x0000000000000001 (NEEDED) Shared library: [./libsink-aarch64-linux-gnu.so]
0x0000000000000001 (NEEDED) Shared library: [./libmemcpy_overflow-aarch64-linux-gnu.so]
0x0000000000000001 (NEEDED) Shared library: [libc.so.6]Vulnerabilities are obvious if we will look on source code, but from binary disassembly it is more complicated. We can trigger both from argv or by fgets source.
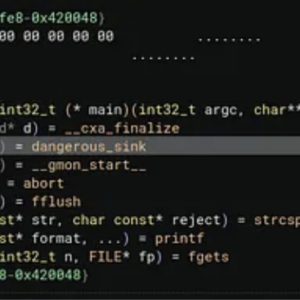
Now lets look how decompiled code look like when we represent it Binary Ninja
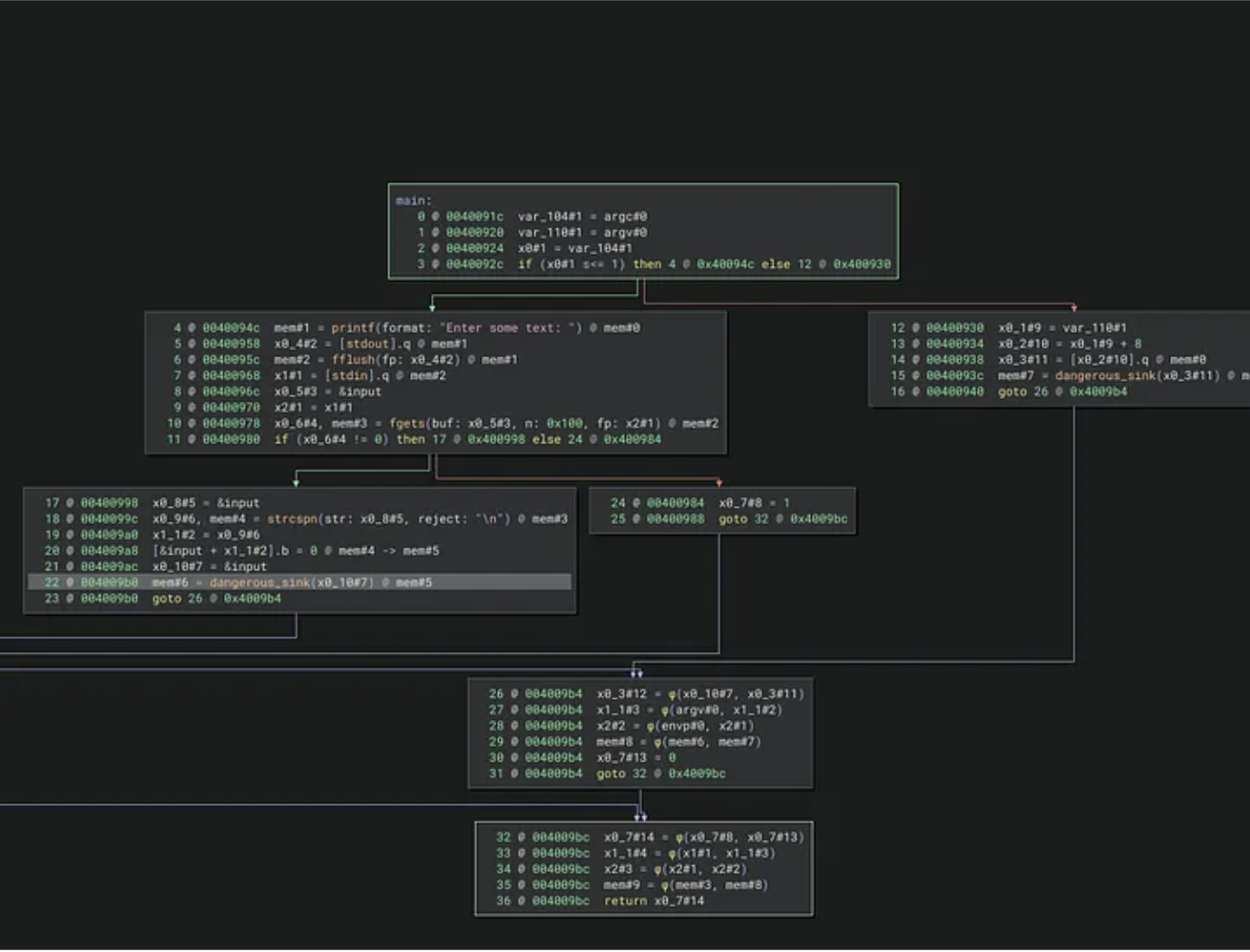
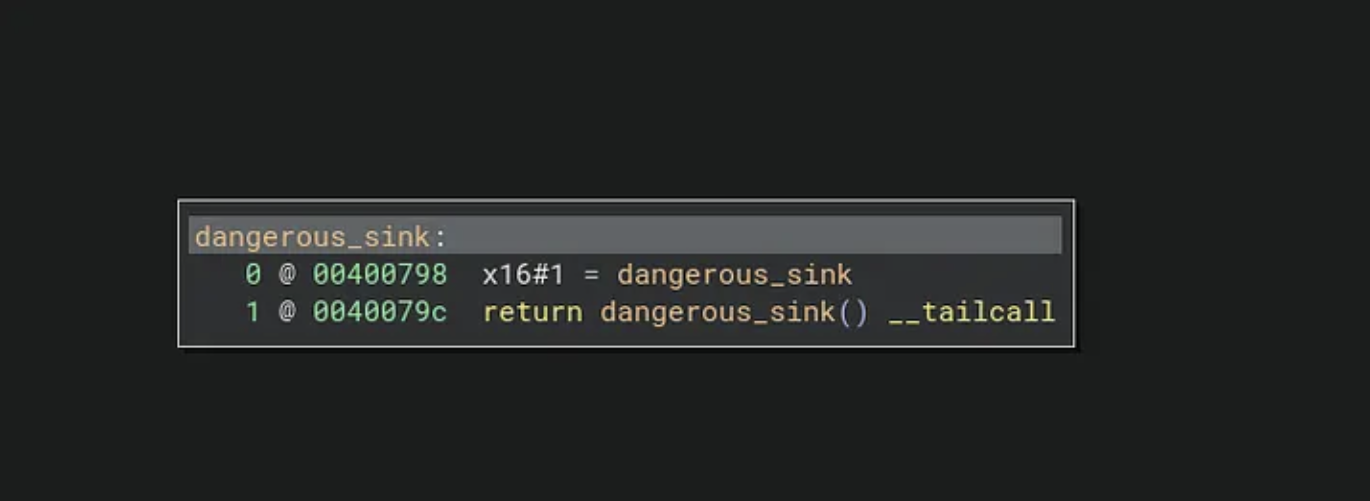
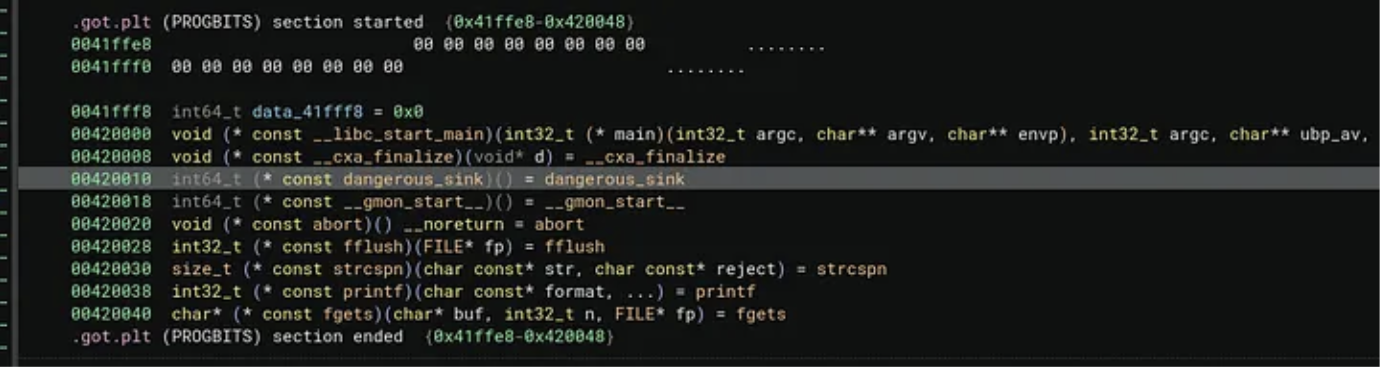
If we will visit our first vulnerable library call dangerous_sink we can observe that its basically returning a pointer i .got (GLOBAL OFFSET TABLE). If we will analyze main binary we will not have find any bug because we are not seeing vulnerable disassembled code.
Now lets look on both .so library files disassembly
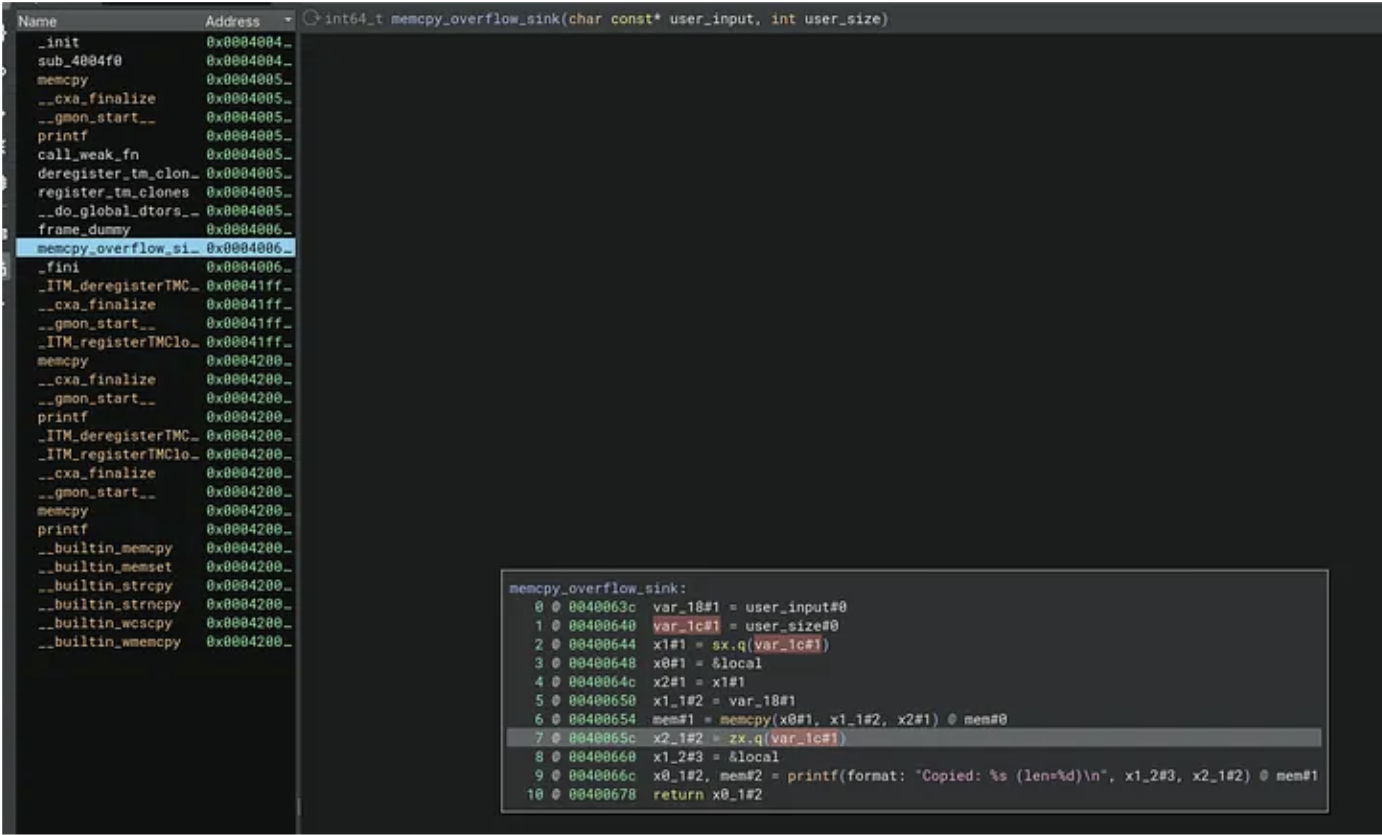
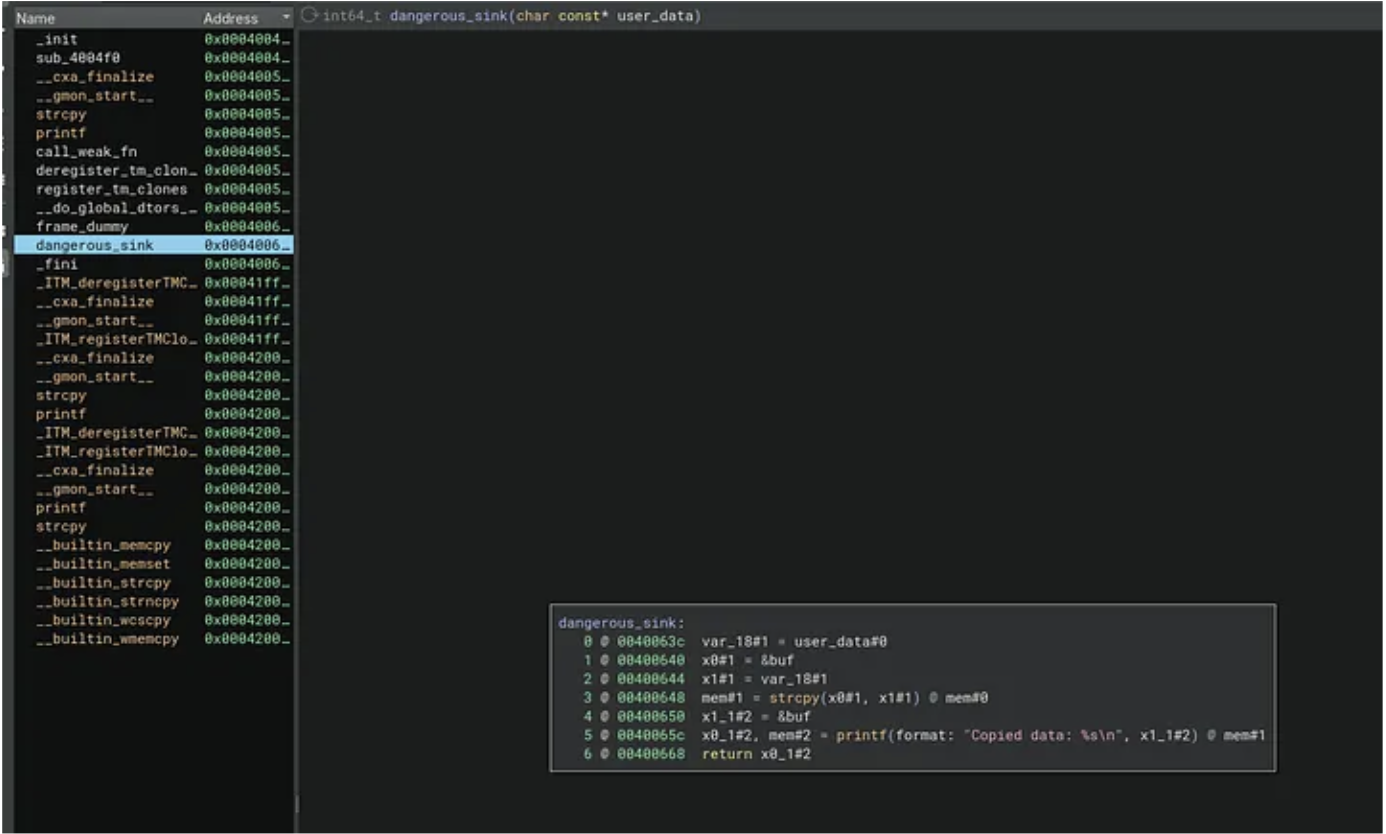
Now we see some memory copy operations in both libraries. Both are vulnerable but we know that looking on source, but from disassembly perspective which is usually a case for vulnerability hunting in closed source binaries we need to investigate.
Let’s run now our engine with following parameters:
python3 -m vulnhunt tests/analysis/libload/main_static2-aarch64-linux-gnu --output-directory=libtest --library=trueor
python3 -m vulnhunt tests/analysis/libload/main_static-aarch64-linux-gnu --output-directory=libtest --lib_dirs=test_libload/lib --library=trueFirst usage assume libraries are in the same folder as main binary, in second use case we can define folder where libraries are located
Once we run the engine we will got following output:
unpwnable_things git:(prod) ✗ python3 -m vulnhunt tests/analysis/libload/main_static2-aarch64-linux-gnu --output-directory=libtest --library=true
____ _ ____
| __ ) _ _| |_ ___| _ \ __ _ _ _
| _ \| | | | __/ _ \ |_) / _` | | | |
| |_) | |_| | || __/ _ < (_| | |_| |
|____/ \__, |\__\___|_| \_\__,_|\__, |
|___/ |___/
2025-11-26T12:01:12.196412Z [debug ] [stackoverflow] analysis_progress=0 engine_version=0.0.17 file_name=__main__.py line=62
Opening main_static2-aarch64-linux-gnu.bndb: 100%|███████| 100/100 [00:00<00:00]
2025-11-26T12:01:12.757899Z [info ] Loaded database: tests/analysis/libload/main_static2-aarch64-linux-gnu.bndb [stackoverflow] line=132
Opening libsink-aarch64-linux-gnu.so.bndb: 100%|█████████| 100/100 [00:00<00:00]
2025-11-26T12:01:12.772404Z [info ] Loaded database: /home/h0rac/unpwnable_things/tests/analysis/libload/libsink-aarch64-linux-gnu.so.bndb [stackoverflow] line=132
2025-11-26T12:01:12.772614Z [info ] Loaded external library: ./libsink-aarch64-linux-gnu.so -> /home/h0rac/unpwnable_things/tests/analysis/libload/libsink-aarch64-linux-gnu.so [stackoverflow] line=334
Opening libmemcpy_overflow-aarch64-linux-gnu.so.bndb: 100%|█| 100/100 [00:00<00:
2025-11-26T12:01:12.788591Z [info ] Loaded database: /home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so.bndb [stackoverflow] line=132
2025-11-26T12:01:12.788922Z [info ] Loaded external library: ./libmemcpy_overflow-aarch64-linux-gnu.so -> /home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so [stackoverflow] line=334
2025-11-26T12:01:12.789175Z [debug ] Skipping system library libc.so.6 for /home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu [stackoverflow] line=272
2025-11-26T12:01:12.857159Z [debug ] [callconv] Skipping call convention fix (database view: /home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu.bndb) [stackoverflow] file_name=analyzer.py line=539
[*] '/home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu'
Arch: aarch64-64-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: PIE enabled
'/home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu'
Arch: aarch64-64-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: PIE enabled
2025-11-26T12:01:12.869545Z [info ] {'RELRO': 'Partial RELRO', 'Stack': 'No canary found', 'NX': 'NX enabled', 'PIE': 'PIE enabled'} [stackoverflow] analysis_progress=0 file_name=__main__.py line=119
2025-11-26T12:01:12.869764Z [info ] stackoverflow module enabled... [stackoverflow] analysis_progress=0 file_name=__main__.py line=159
2025-11-26T12:01:12.870030Z [info ] Path: ./libsink-aarch64-linux-gnu.so -> Library: /home/h0rac/unpwnable_things/tests/analysis/libload/libsink-aarch64-linux-gnu.so.bndb [stackoverflow] file_name=analyzer.py line=3697
2025-11-26T12:01:12.870309Z [debug ] Finding sources and sinks in function: _init - 0x4004d0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.874015Z [debug ] Finding sources and sinks in function: sub_4004f0 - 0x4004f0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.876446Z [debug ] Finding sources and sinks in function: __cxa_finalize - 0x400510 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.878149Z [debug ] Finding sources and sinks in function: __gmon_start__ - 0x400520 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.879486Z [debug ] Finding sources and sinks in function: call_weak_fn - 0x400550 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.881971Z [debug ] Finding sources and sinks in function: deregister_tm_clones - 0x400570 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.883817Z [debug ] Finding sources and sinks in function: register_tm_clones - 0x4005a0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.885724Z [debug ] Finding sources and sinks in function: __do_global_dtors_aux - 0x4005e0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.890333Z [debug ] Finding sources and sinks in function: frame_dummy - 0x400630 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.891847Z [debug ] Finding sources and sinks in function: dangerous_sink - 0x400634 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.893433Z [debug ] Finding sources and sinks in function: _fini - 0x40066c [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.893999Z [info ] Path: ./libmemcpy_overflow-aarch64-linux-gnu.so -> Library: /home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so.bndb [stackoverflow] file_name=analyzer.py line=3697
2025-11-26T12:01:12.894193Z [debug ] Finding sources and sinks in function: _init - 0x4004d8 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.895091Z [debug ] Finding sources and sinks in function: sub_4004f0 - 0x4004f0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.896526Z [debug ] Finding sources and sinks in function: __cxa_finalize - 0x400520 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.897818Z [debug ] Finding sources and sinks in function: __gmon_start__ - 0x400530 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.899420Z [debug ] Finding sources and sinks in function: call_weak_fn - 0x400550 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.902936Z [debug ] Finding sources and sinks in function: deregister_tm_clones - 0x400570 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.905929Z [debug ] Finding sources and sinks in function: register_tm_clones - 0x4005a0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.908758Z [debug ] Finding sources and sinks in function: __do_global_dtors_aux - 0x4005e0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.913089Z [debug ] Finding sources and sinks in function: frame_dummy - 0x400630 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.915013Z [debug ] Finding sources and sinks in function: memcpy_overflow_sink - 0x400634 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.918298Z [debug ] Finding sources and sinks in function: _fini - 0x40067c [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.919822Z [debug ] Finding sources and sinks in function: _init - 0x4007e0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.921725Z [debug ] Finding sources and sinks in function: sub_400800 - 0x400800 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.924230Z [debug ] Finding sources and sinks in function: __libc_start_main - 0x400830 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.925694Z [debug ] Finding sources and sinks in function: __cxa_finalize - 0x400840 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.926552Z [debug ] Finding sources and sinks in function: memcpy_overflow_sink - 0x400850 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.927501Z [debug ] Finding sources and sinks in function: dangerous_sink - 0x400860 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.928831Z [debug ] Finding sources and sinks in function: __gmon_start__ - 0x400870 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.929777Z [debug ] Finding sources and sinks in function: abort - 0x400880 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.931124Z [debug ] Finding sources and sinks in function: fflush - 0x400890 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.932505Z [debug ] Finding sources and sinks in function: strcspn - 0x4008a0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.934806Z [debug ] Finding sources and sinks in function: _start - 0x400900 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.937231Z [debug ] Finding sources and sinks in function: call_weak_fn - 0x400934 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.939402Z [debug ] Finding sources and sinks in function: deregister_tm_clones - 0x400950 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.941913Z [debug ] Finding sources and sinks in function: register_tm_clones - 0x400980 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.943536Z [debug ] Finding sources and sinks in function: __do_global_dtors_aux - 0x4009c0 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.947695Z [debug ] Finding sources and sinks in function: frame_dummy - 0x400a10 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.949628Z [debug ] Finding sources and sinks in function: main - 0x400a14 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.959172Z [debug ] Finding sources and sinks in function: _fini - 0x400af4 [stackoverflow] file_name=analyzer.py line=3897
2025-11-26T12:01:12.959899Z [debug ] func_name: main, func_addr: 0x400a14, func_sinks_number: 3, func_sinks: ['strlen', 'printf', 'strlen'], func_sources_number: 1 func_sources: ['fgets'] [stackoverflow] file_name=analyzer.py line=4018
2025-11-26T12:01:12.960007Z [debug ] func_name: dangerous_sink, func_addr: 0x400634, func_sinks_number: 2, func_sinks: ['strcpy', 'printf'], func_sources_number: 0 func_sources: [] [stackoverflow] file_name=analyzer.py line=4018
2025-11-26T12:01:12.960075Z [debug ] func_name: memcpy_overflow_sink, func_addr: 0x400634, func_sinks_number: 2, func_sinks: ['memcpy', 'printf'], func_sources_number: 0 func_sources: [] [stackoverflow] file_name=analyzer.py line=4018
2025-11-26T12:01:12.960929Z [info ] Start of analysis: main_static2-aarch64-linux-gnu
-------------------------------------------------------------------------------------
[stackoverflow] file_name=analyzer.py line=3801
2025-11-26T12:01:12.961132Z [info ] 0x400a1c: Tracing var_124#1 = argc#0, instructions to trace: 55 [stackoverflow] analysis_progress=0 file_name=analyzer.py line=3275
2025-11-26T12:01:12.961215Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=0 file_name=analyzer.py line=3289
2025-11-26T12:01:12.961340Z [info ] 0x400a1c: Tracing param: var_124#1 = argc#0 [stackoverflow] analysis_progress=0 file_name=analyzer.py line=1825
2025-11-26T12:01:12.961819Z [info ] 0x400a24: Tracing param: x0#1 = var_124#1 [stackoverflow] analysis_progress=0 file_name=analyzer.py line=1825
2025-11-26T12:01:12.962101Z [info ] 0x400a2c: Tracing param: if (x0#1 s<= 1) then 4 @ 0x400a68 else 12 @ 0x400a30 [stackoverflow] analysis_progress=0 file_name=analyzer.py line=1825
2025-11-26T12:01:12.962220Z [info ] Detected conditional if (x0#1 s<= 1) then 4 @ 0x400a68 else 12 @ 0x400a30 [stackoverflow] analysis_progress=0 file_name=analyzer.py line=1829
2025-11-26T12:01:12.962389Z [info ] 0x400a20: Tracing var_130#1 = argv#0, instructions to trace: 54 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3275
2025-11-26T12:01:12.962470Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3289
2025-11-26T12:01:12.962567Z [info ] 0x400a20: Tracing param: var_130#1 = argv#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.962754Z [info ] 0x400a30: Tracing param: x0_1#12 = var_130#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.963640Z [info ] 0x400a34: Tracing param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.964086Z [info ] 0x400a38: Tracing param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.964584Z [info ] 0x400a3c: Tracing param: x0_3#14 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.965123Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_4#15, mem#9 = 0x400820(x0_3#14) @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2160
2025-11-26T12:01:12.965573Z [info ] Resolved [strlen] by address: 0x400820 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2184
2025-11-26T12:01:12.965889Z [info ] Sink strlen detected [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2365
2025-11-26T12:01:12.966060Z [info ] Reverse recursive search for: x0_4#15, mem#9 = 0x400820(x0_3#14) @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1301
2025-11-26T12:01:12.966213Z [info ] Reverse recursive source param definition search for param: x0_3#14 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1348
/home/h0rac/unpwnable_things/src/vulnhunt/analyzer.py:1135: DeprecatedWarning: visit_all is deprecated as of 4.0.4907. Use :py:func:`MediumLevelILInstruction.traverse` instead.
if not var.visit_all(callback):
2025-11-26T12:01:12.967017Z [info ] Found param: x0_3#14 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.967404Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.968366Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.968835Z [info ] End of reverse search, src param: [x0_1#12 + 8].q @ mem#0, forward taint search required [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1364
2025-11-26T12:01:12.971851Z [info ] 0x400a40: x0_3#14 passed to: strlen [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1651
2025-11-26T12:01:12.972110Z [info ] 0x400a48: Tracing param: x0_5#16 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.972683Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#10 = 0x400860(x0_5#16) @ mem#9 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2160
2025-11-26T12:01:12.973187Z [info ] Resolved [dangerous_sink] by address: 0x400860 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2184
2025-11-26T12:01:12.973847Z [info ] Found param: x0_5#16 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.974258Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.974826Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.975089Z [info ] Visit [dangerous_sink] function [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3121
2025-11-26T12:01:12.975262Z [info ] 0x400860: First instruction at [dangerous_sink]: x16#1 = 0x420020 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3145
2025-11-26T12:01:12.975448Z [info ] 0x400a54: Tracing param: x0_6#17 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.975764Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#11 = 0x400850(x0_6#17, x1#4) @ mem#10 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2160
2025-11-26T12:01:12.975961Z [info ] Resolved [memcpy_overflow_sink] by address: 0x400850 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2184
2025-11-26T12:01:12.976224Z [info ] Found param: x0_6#17 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.976468Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.976710Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.976962Z [info ] Found param usage in sign extension operation: x1#4 = zx.q(user_len#1) [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1027
2025-11-26T12:01:12.977093Z [info ] Found param usage: user_len#1 = x0_4#15 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1068
2025-11-26T12:01:12.977264Z [info ] Found param usage in call function: x0_4#15, mem#9 = 0x400820(x0_3#14) @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1055
2025-11-26T12:01:12.977438Z [info ] End of reverse search, definition: user_len#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1193
2025-11-26T12:01:12.977572Z [info ] Visit [memcpy_overflow_sink] function [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3121
2025-11-26T12:01:12.977705Z [info ] 0x400850: First instruction at [memcpy_overflow_sink]: x16#1 = 0x420018 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=3145
2025-11-26T12:01:12.977877Z [info ] 0x400ae8: Tracing param: x0_6#18 = ϕ(x0_16#10, x0_6#17) [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2974
2025-11-26T12:01:12.978109Z [info ] Found param: x0_16#10 = &input [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.978375Z [info ] Found param: x0_6#17 = user_data#1 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.978619Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.978855Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.979097Z [info ] 0x400ae8: Tracing param: user_data#2 = ϕ(user_data#0, user_data#1) [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=2974
2025-11-26T12:01:12.979238Z [info ] End of reverse search, definition: user_data#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1118
2025-11-26T12:01:12.979427Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.979662Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=1.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.979903Z [info ] 0x400a68: Tracing mem#1 = 0x4008b0("Enter some text: ") @ mem#0, instructions to trace: 51 [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=3275
2025-11-26T12:01:12.979989Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=3289
2025-11-26T12:01:12.980108Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#1 = 0x4008b0("Enter some text: ") @ mem#0 [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=2160
2025-11-26T12:01:12.980288Z [info ] Resolved [printf] by address: 0x4008b0 [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=2184
2025-11-26T12:01:12.980542Z [warning ] Sink printf skipped for return value tracking [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=2361
2025-11-26T12:01:12.980653Z [info ] Sink printf detected [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=2365
2025-11-26T12:01:12.980812Z [info ] Reverse recursive search for: mem#1 = 0x4008b0("Enter some text: ") @ mem#0 [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=1301
2025-11-26T12:01:12.981311Z [info ] printf with static param: "Enter some text: " [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=1334
2025-11-26T12:01:12.984610Z [info ] 0x400a68: "Enter some text: " passed to: printf [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=1651
2025-11-26T12:01:12.985005Z [info ] stackoverflow module check passed [stackoverflow] analysis_progress=2.7 file_name=analyzer.py line=2601
2025-11-26T12:01:12.985149Z [info ] printf [stackoverflow] file_name=argstream.py line=24
2025-11-26T12:01:12.985375Z [info ] 0x400a74: Tracing x0_7#2 = [stdout].q @ mem#1, instructions to trace: 50 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=3275
2025-11-26T12:01:12.985458Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=3289
2025-11-26T12:01:12.985648Z [info ] 0x400a74: Tracing param: x0_7#2 = [stdout].q @ mem#1 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=1825
2025-11-26T12:01:12.986058Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#2 = 0x400890(x0_7#2) @ mem#1 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=2160
2025-11-26T12:01:12.986290Z [info ] Resolved [fflush] by address: 0x400890 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=2184
2025-11-26T12:01:12.986576Z [info ] Found param: x0_7#2 = [stdout].q @ mem#1 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=1088
2025-11-26T12:01:12.986794Z [info ] Visit [fflush] function [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=3121
2025-11-26T12:01:12.986963Z [info ] 0x400890: First instruction at [fflush]: x16#1 = 0x420038 [stackoverflow] analysis_progress=4.1 file_name=analyzer.py line=3145
2025-11-26T12:01:12.987180Z [info ] 0x400a84: Tracing x1_1#1 = [stdin].q @ mem#2, instructions to trace: 48 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=3275
2025-11-26T12:01:12.987265Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=3289
2025-11-26T12:01:12.987421Z [info ] 0x400a84: Tracing param: x1_1#1 = [stdin].q @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.987655Z [info ] 0x400a8c: Tracing param: x2#1 = x1_1#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1825
2025-11-26T12:01:12.987918Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_9#4, mem#3 = 0x4008c0(x0_8#3, 0x100, x2#1) @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2160
2025-11-26T12:01:12.988136Z [info ] Resolved [fgets] by address: 0x4008c0 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2184
2025-11-26T12:01:12.988365Z [info ] Source fgets detected [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2269
2025-11-26T12:01:12.988581Z [info ] Reverse recursive search for: x0_9#4, mem#3 = 0x4008c0(x0_8#3, 0x100, x2#1) @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1301
2025-11-26T12:01:12.988748Z [info ] Reverse recursive source param definition search for param: x0_8#3 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1348
2025-11-26T12:01:12.988929Z [info ] Found param: x0_8#3 = &input [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.989115Z [info ] End of reverse search, src param: &input, forward taint search required [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1364
2025-11-26T12:01:12.989511Z [info ] fgets with static param: 0x100 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1338
2025-11-26T12:01:12.989713Z [info ] Reverse recursive source param definition search for param: x2#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1348
2025-11-26T12:01:12.990166Z [info ] Found param: x2#1 = x1_1#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.990884Z [info ] Found param: x1_1#1 = [stdin].q @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.991167Z [info ] End of reverse search, src param: [stdin].q @ mem#2, forward taint search required [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1364
2025-11-26T12:01:12.997531Z [info ] 0x400ae8: Tracing param: x2#2 = ϕ(envp#0, x2#1) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2974
2025-11-26T12:01:12.998204Z [info ] End of reverse search, definition: envp#0 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1118
2025-11-26T12:01:12.998651Z [info ] Found param: x2#1 = x1_1#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.999133Z [info ] Found param: x1_1#1 = [stdin].q @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:12.999554Z [info ] 0x400af0: Tracing param: x2#3 = ϕ(x2#1, x2#2) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2974
2025-11-26T12:01:12.999841Z [info ] Found param: x2#1 = x1_1#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.000147Z [info ] Found param: x1_1#1 = [stdin].q @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.000587Z [info ] Found param: x2#2 = ϕ(envp#0, x2#1) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.001103Z [info ] End of reverse search, definition: envp#0 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1118
2025-11-26T12:01:13.001512Z [info ] 0x400af0: Tracing param: x1#6 = ϕ(x1_1#1, x1#5) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=2974
2025-11-26T12:01:13.001991Z [info ] Found param: x1_1#1 = [stdin].q @ mem#2 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.002370Z [info ] Found param: x1#5 = ϕ(x1_3#3, x1#4) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.002740Z [info ] Found param usage in sign extension operation: x1_3#3 = zx.q(user_len#1) [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1027
2025-11-26T12:01:13.002895Z [info ] Found param usage: user_len#1 = x0_14#8 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1068
2025-11-26T12:01:13.003103Z [info ] Found param usage in call function: x0_14#8, mem#6 = 0x400820(x0_13#7) @ mem#5 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1055
2025-11-26T12:01:13.003290Z [info ] End of reverse search, definition: user_len#1 [stackoverflow] analysis_progress=5.4 file_name=analyzer.py line=1193
2025-11-26T12:01:13.003477Z [info ] 0x400a88: Tracing x0_8#3 = &input, instructions to trace: 47 [stackoverflow] analysis_progress=6.8 file_name=analyzer.py line=3275
2025-11-26T12:01:13.003545Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=6.8 file_name=analyzer.py line=3289
2025-11-26T12:01:13.003678Z [info ] 0x400a88: Tracing param: x0_8#3 = &input [stackoverflow] analysis_progress=6.8 file_name=analyzer.py line=1825
2025-11-26T12:01:13.004036Z [info ] 0x400a9c: Tracing if (x0_9#4 != 0) then 24 @ 0x400ab4 else 37 @ 0x400aa0, instructions to trace: 44 [stackoverflow] analysis_progress=8.1 file_name=analyzer.py line=3275
2025-11-26T12:01:13.004159Z [info ] 0x400a44: Tracing user_len#1 = x0_4#15, instructions to trace: 38 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=3275
2025-11-26T12:01:13.004221Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=3289
2025-11-26T12:01:13.004357Z [info ] 0x400a44: Tracing param: user_len#1 = x0_4#15 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1825
2025-11-26T12:01:13.004702Z [info ] 0x400a50: Tracing param: x1#4 = zx.q(user_len#1) [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1825
2025-11-26T12:01:13.005026Z [info ] 0x400ae8: Tracing param: x1#5 = ϕ(x1_3#3, x1#4) [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=2974
2025-11-26T12:01:13.005274Z [info ] Found param usage in sign extension operation: x1_3#3 = zx.q(user_len#1) [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1027
2025-11-26T12:01:13.005401Z [info ] Found param usage: user_len#1 = x0_14#8 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1068
2025-11-26T12:01:13.005569Z [info ] Found param usage in call function: x0_14#8, mem#6 = 0x400820(x0_13#7) @ mem#5 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1055
2025-11-26T12:01:13.005753Z [info ] End of reverse search, definition: user_len#1 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1193
2025-11-26T12:01:13.005979Z [info ] Found param usage in sign extension operation: x1#4 = zx.q(user_len#1) [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1027
2025-11-26T12:01:13.006116Z [info ] Found param usage: user_len#1 = x0_4#15 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1068
2025-11-26T12:01:13.006332Z [info ] Found param usage in call function: x0_4#15, mem#9 = 0x400820(x0_3#14) @ mem#0 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1055
2025-11-26T12:01:13.006658Z [info ] End of reverse search, definition: user_len#1 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1193
2025-11-26T12:01:13.007137Z [info ] 0x400ae8: Tracing param: user_len#2 = ϕ(user_len#0, user_len#1) [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=2974
2025-11-26T12:01:13.007611Z [info ] End of reverse search, definition: user_len#0 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1118
2025-11-26T12:01:13.007983Z [info ] Found param: user_len#1 = x0_4#15 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.008270Z [info ] Found param: x0_3#14 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.008449Z [info ] Found param: x0_3#14 = user_data#1 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.008689Z [info ] Found param: user_data#1 = x0_2#13 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.008938Z [info ] Found param: x0_2#13 = [x0_1#12 + 8].q @ mem#0 [stackoverflow] analysis_progress=9.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.009248Z [info ] 0x400a5c: Tracing goto 39 @ 0x400ae8, instructions to trace: 32 [stackoverflow] analysis_progress=10.8 file_name=analyzer.py line=3275
2025-11-26T12:01:13.009375Z [info ] 0x400ab4: Tracing x0_11#5 = &input, instructions to trace: 31 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=3275
2025-11-26T12:01:13.009459Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=3289
2025-11-26T12:01:13.009599Z [info ] 0x400ab4: Tracing param: x0_11#5 = &input [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.009918Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_12#6, mem#4 = 0x4008a0(x0_11#5, "\n") @ mem#3 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=2160
2025-11-26T12:01:13.010137Z [info ] Resolved [strcspn] by address: 0x4008a0 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=2184
2025-11-26T12:01:13.010430Z [info ] Visit [strcspn] function [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=3121
2025-11-26T12:01:13.010589Z [info ] 0x4008a0: First instruction at [strcspn]: x16#1 = 0x420040 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=3145
2025-11-26T12:01:13.010817Z [info ] 0x400abc: Tracing param: x1_2#2 = x0_12#6 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.011132Z [info ] 0x400ac4: Tracing param: [&input + x1_2#2].b = 0 @ mem#4 -> mem#5 [stackoverflow] analysis_progress=12.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.011453Z [info ] 0x400ac8: Tracing x0_13#7 = &input, instructions to trace: 27 [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=3275
2025-11-26T12:01:13.011522Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=3289
2025-11-26T12:01:13.011660Z [info ] 0x400ac8: Tracing param: x0_13#7 = &input [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1825
2025-11-26T12:01:13.011930Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_14#8, mem#6 = 0x400820(x0_13#7) @ mem#5 [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=2160
2025-11-26T12:01:13.012129Z [info ] Resolved [strlen] by address: 0x400820 [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=2184
2025-11-26T12:01:13.012337Z [info ] Sink strlen detected [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=2365
2025-11-26T12:01:13.012464Z [info ] Reverse recursive search for: x0_14#8, mem#6 = 0x400820(x0_13#7) @ mem#5 [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1301
2025-11-26T12:01:13.012616Z [info ] Reverse recursive source param definition search for param: x0_13#7 [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1348
2025-11-26T12:01:13.012787Z [info ] Found param: x0_13#7 = &input [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1088
2025-11-26T12:01:13.012941Z [info ] End of reverse search, src param: &input, forward taint search required [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1364
2025-11-26T12:01:13.017978Z [info ] 0x400acc: x0_13#7 passed to: strlen [stackoverflow] analysis_progress=13.5 file_name=analyzer.py line=1651
2025-11-26T12:01:13.018788Z [info ] 0x400ad0: Tracing user_len#1 = x0_14#8, instructions to trace: 25 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=3275
2025-11-26T12:01:13.018935Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=3289
2025-11-26T12:01:13.019234Z [info ] 0x400ad0: Tracing param: user_len#1 = x0_14#8 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1825
2025-11-26T12:01:13.019905Z [info ] 0x400ae0: Tracing param: x1_3#3 = zx.q(user_len#1) [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1825
2025-11-26T12:01:13.020308Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#8 = 0x400850(x0_16#10, x1_3#3) @ mem#7 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=2160
2025-11-26T12:01:13.020530Z [info ] Resolved [memcpy_overflow_sink] by address: 0x400850 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=2184
2025-11-26T12:01:13.020826Z [info ] Found param: x0_16#10 = &input [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1088
2025-11-26T12:01:13.021483Z [info ] Found param usage in sign extension operation: x1_3#3 = zx.q(user_len#1) [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1027
2025-11-26T12:01:13.021627Z [info ] Found param usage: user_len#1 = x0_14#8 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1068
2025-11-26T12:01:13.021792Z [info ] Found param usage in call function: x0_14#8, mem#6 = 0x400820(x0_13#7) @ mem#5 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1055
2025-11-26T12:01:13.021982Z [info ] End of reverse search, definition: user_len#1 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1193
2025-11-26T12:01:13.022143Z [info ] Visit [memcpy_overflow_sink] function [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=3121
2025-11-26T12:01:13.022295Z [info ] 0x400850: First instruction at [memcpy_overflow_sink]: x16#1 = 0x420018 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=3145
2025-11-26T12:01:13.022546Z [info ] 0x400ae8: Tracing param: user_len#2 = ϕ(user_len#0, user_len#1) [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=2974
2025-11-26T12:01:13.022709Z [info ] End of reverse search, definition: user_len#0 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1118
2025-11-26T12:01:13.022906Z [info ] Found param: user_len#1 = x0_14#8 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1088
2025-11-26T12:01:13.023153Z [info ] Found param: x0_13#7 [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1088
2025-11-26T12:01:13.023368Z [info ] Found param: x0_13#7 = &input [stackoverflow] analysis_progress=14.9 file_name=analyzer.py line=1088
2025-11-26T12:01:13.023786Z [info ] 0x400ad4: Tracing x0_15#9 = &input, instructions to trace: 24 [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=3275
2025-11-26T12:01:13.023977Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=3289
2025-11-26T12:01:13.024312Z [info ] 0x400ad4: Tracing param: x0_15#9 = &input [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.025068Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#7 = 0x400860(x0_15#9) @ mem#6 [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=2160
2025-11-26T12:01:13.025330Z [info ] Resolved [dangerous_sink] by address: 0x400860 [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=2184
2025-11-26T12:01:13.025621Z [info ] Found param: x0_15#9 = &input [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=1088
2025-11-26T12:01:13.025847Z [info ] Visit [dangerous_sink] function [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=3121
2025-11-26T12:01:13.026023Z [info ] 0x400860: First instruction at [dangerous_sink]: x16#1 = 0x420020 [stackoverflow] analysis_progress=16.2 file_name=analyzer.py line=3145
2025-11-26T12:01:13.026309Z [info ] 0x400adc: Tracing x0_16#10 = &input, instructions to trace: 22 [stackoverflow] analysis_progress=17.6 file_name=analyzer.py line=3275
2025-11-26T12:01:13.026379Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=17.6 file_name=analyzer.py line=3289
2025-11-26T12:01:13.026532Z [info ] 0x400adc: Tracing param: x0_16#10 = &input [stackoverflow] analysis_progress=17.6 file_name=analyzer.py line=1825
2025-11-26T12:01:13.026901Z [info ] 0x400ae4: Tracing goto 39 @ 0x400ae8, instructions to trace: 19 [stackoverflow] analysis_progress=18.9 file_name=analyzer.py line=3275
2025-11-26T12:01:13.027030Z [info ] 0x400aa0: Tracing x0_10#11 = 1, instructions to trace: 18 [stackoverflow] analysis_progress=20.3 file_name=analyzer.py line=3275
2025-11-26T12:01:13.027093Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=20.3 file_name=analyzer.py line=3289
2025-11-26T12:01:13.027236Z [info ] 0x400aa0: Tracing param: x0_10#11 = 1 [stackoverflow] analysis_progress=20.3 file_name=analyzer.py line=1825
2025-11-26T12:01:13.027484Z [info ] 0x400af0: Tracing param: x0_10#20 = ϕ(x0_10#11, x0_10#19) [stackoverflow] analysis_progress=20.3 file_name=analyzer.py line=1825
2025-11-26T12:01:13.027739Z [info ] 0x400af0: Tracing param: return x0_10#20 [stackoverflow] analysis_progress=20.3 file_name=analyzer.py line=1825
2025-11-26T12:01:13.027913Z [info ] 0x400aa4: Tracing goto 48 @ 0x400af0, instructions to trace: 17 [stackoverflow] analysis_progress=21.6 file_name=analyzer.py line=3275
2025-11-26T12:01:13.028143Z [info ] 0x400ae8: Tracing mem#12 = ϕ(mem#8, mem#11), instructions to trace: 10 [stackoverflow] analysis_progress=23.0 file_name=analyzer.py line=3275
2025-11-26T12:01:13.028265Z [info ] 0x400ae8: Tracing x0_10#19 = 0, instructions to trace: 9 [stackoverflow] analysis_progress=24.3 file_name=analyzer.py line=3275
2025-11-26T12:01:13.028323Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=24.3 file_name=analyzer.py line=3289
2025-11-26T12:01:13.028469Z [info ] 0x400ae8: Tracing param: x0_10#19 = 0 [stackoverflow] analysis_progress=24.3 file_name=analyzer.py line=1825
2025-11-26T12:01:13.028757Z [info ] 0x400ae8: Tracing goto 48 @ 0x400af0, instructions to trace: 8 [stackoverflow] analysis_progress=25.7 file_name=analyzer.py line=3275
2025-11-26T12:01:13.028882Z [info ] 0x400af0: Tracing user_len#3 = ϕ(user_len#0, user_len#2), instructions to trace: 7 [stackoverflow] analysis_progress=27.0 file_name=analyzer.py line=3275
2025-11-26T12:01:13.029011Z [info ] 0x400af0: Tracing user_data#3 = ϕ(user_data#0, user_data#2), instructions to trace: 6 [stackoverflow] analysis_progress=28.4 file_name=analyzer.py line=3275
2025-11-26T12:01:13.029135Z [info ] 0x400af0: Tracing user_len#3 = ϕ(user_len#0, user_len#2), instructions to trace: 5 [stackoverflow] analysis_progress=29.7 file_name=analyzer.py line=3275
2025-11-26T12:01:13.029316Z [info ] 0x400af0: Tracing mem#13 = ϕ(mem#3, mem#12), instructions to trace: 1 [stackoverflow] analysis_progress=31.1 file_name=analyzer.py line=3275
2025-11-26T12:01:13.029418Z [info ] End of analysis: main_static2-aarch64-linux-gnu
-------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=3809
2025-11-26T12:01:13.029587Z [info ] Start of analysis: libsink-aarch64-linux-gnu.so
-------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=3801
2025-11-26T12:01:13.029719Z [info ] 0x40063c: Tracing var_18#1 = user_data#0, instructions to trace: 6 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=3275
2025-11-26T12:01:13.029783Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=3289
2025-11-26T12:01:13.029947Z [info ] 0x40063c: Tracing param: var_18#1 = user_data#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1825
2025-11-26T12:01:13.030444Z [info ] 0x400644: Tracing param: x1#1 = var_18#1 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1825
2025-11-26T12:01:13.030915Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2160
2025-11-26T12:01:13.031221Z [info ] Resolved [strcpy] by address: 0x400530 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2184
2025-11-26T12:01:13.031495Z [warning ] Sink strcpy skipped for return value tracking [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2361
2025-11-26T12:01:13.031651Z [info ] Sink strcpy detected [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2365
2025-11-26T12:01:13.031832Z [info ] Reverse recursive search for: mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1301
2025-11-26T12:01:13.032084Z [info ] Reverse recursive source param definition search for param: x0#1 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1348
2025-11-26T12:01:13.032403Z [info ] Found param: x0#1 = &buf [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.032617Z [info ] End of reverse search, src param: &buf, forward taint search required [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1364
2025-11-26T12:01:13.032807Z [info ] Reverse recursive source param definition search for param: x1#1 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1348
2025-11-26T12:01:13.032999Z [info ] Found param: x1#1 = var_18#1 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.033264Z [info ] Found param: var_18#1 = user_data#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1088
2025-11-26T12:01:13.033460Z [info ] End of reverse search, definition: user_data#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1118
2025-11-26T12:01:13.037295Z [info ] 0x400648: x0#1 passed to: strcpy [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1651
2025-11-26T12:01:13.037528Z [info ] 0x400648: x1#1 passed to: strcpy as SRC param [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=1632
2025-11-26T12:01:13.037611Z [info ] Checking if vulnerable to stack overflow bug class ... [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2679
2025-11-26T12:01:13.037744Z [info ] Current instruction : mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2682
2025-11-26T12:01:13.038413Z [debug ] Chain for x1#1: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.038502Z [debug ] ['x1#1 = var_18#1', 'var_18#1 = user_data#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.038591Z [debug ] Found common parameter: {'user_data#0', 'var_18#1'} [stackoverflow] file_name=stack_taint_overflow.py line=1265
2025-11-26T12:01:13.038718Z [error ] Possible type stack overflow detected at 0x400648 | mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] file_name=stack_taint_overflow.py line=1869
2025-11-26T12:01:13.038814Z [error ] Variable x1#1 was computed from a source operation without bounds checking [stackoverflow] file_name=stack_taint_overflow.py line=1872
2025-11-26T12:01:13.038896Z [error ] Dest variable &buf was computed with buffer size 16 [stackoverflow] file_name=stack_taint_overflow.py line=1875
2025-11-26T12:01:13.040709Z [info ] Saved result to libtest/stackoverflow/libsink-aarch64-linux-gnu.so_00001.json [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=4632
2025-11-26T12:01:13.041054Z [info ] Saved result DFG to libtest/stackoverflow/libsink-aarch64-linux-gnu.so_00001_dfg.json [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=4638
2025-11-26T12:01:13.041150Z [info ]
-----------------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=4639
2025-11-26T12:01:13.041484Z [info ] 0x400640: Tracing x0#1 = &buf, instructions to trace: 5 [stackoverflow] analysis_progress=33.8 file_name=analyzer.py line=3275
2025-11-26T12:01:13.041650Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=33.8 file_name=analyzer.py line=3289
2025-11-26T12:01:13.042063Z [info ] 0x400640: Tracing param: x0#1 = &buf [stackoverflow] analysis_progress=33.8 file_name=analyzer.py line=1825
2025-11-26T12:01:13.042934Z [info ] 0x400650: Tracing x1_1#2 = &buf, instructions to trace: 2 [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=3275
2025-11-26T12:01:13.043083Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=3289
2025-11-26T12:01:13.043280Z [info ] 0x400650: Tracing param: x1_1#2 = &buf [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1825
2025-11-26T12:01:13.043650Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_1#2, mem#2 = 0x400540("Copied data: %s\n", x1_1#2) @ mem#1 [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=2160
2025-11-26T12:01:13.043882Z [info ] Resolved [printf] by address: 0x400540 [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=2184
2025-11-26T12:01:13.044175Z [warning ] Sink printf skipped for return value tracking [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=2361
2025-11-26T12:01:13.044266Z [info ] Sink printf detected [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=2365
2025-11-26T12:01:13.044413Z [info ] Reverse recursive search for: x0_1#2, mem#2 = 0x400540("Copied data: %s\n", x1_1#2) @ mem#1 [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1301
2025-11-26T12:01:13.044734Z [info ] printf with static param: "Copied data: %s\n" [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1334
2025-11-26T12:01:13.044873Z [info ] Reverse recursive source param definition search for param: x1_1#2 [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1348
2025-11-26T12:01:13.045499Z [info ] Found param: x1_1#2 = &buf [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1088
2025-11-26T12:01:13.045699Z [info ] End of reverse search, src param: &buf, forward taint search required [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1364
2025-11-26T12:01:13.048212Z [info ] 0x40065c: "Copied data: %s\n" passed to: printf [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1651
2025-11-26T12:01:13.048509Z [info ] 0x40065c: x1_1#2 passed to: printf as SRC param [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=1632
2025-11-26T12:01:13.048601Z [info ] stackoverflow module check passed [stackoverflow] analysis_progress=35.1 file_name=analyzer.py line=2601
2025-11-26T12:01:13.048718Z [info ] printf [stackoverflow] file_name=argstream.py line=24
2025-11-26T12:01:13.048988Z [info ] 0x400668: Tracing return x0_1#2, instructions to trace: 0 [stackoverflow] analysis_progress=36.5 file_name=analyzer.py line=3275
2025-11-26T12:01:13.049088Z [info ] End of analysis: libsink-aarch64-linux-gnu.so
-------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=3809
2025-11-26T12:01:13.049296Z [info ] Start of analysis: libmemcpy_overflow-aarch64-linux-gnu.so
-------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=3801
2025-11-26T12:01:13.049439Z [info ] 0x40063c: Tracing var_18#1 = user_input#0, instructions to trace: 10 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=3275
2025-11-26T12:01:13.049504Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=3289
2025-11-26T12:01:13.049676Z [info ] 0x40063c: Tracing param: var_18#1 = user_input#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1825
2025-11-26T12:01:13.050338Z [info ] 0x400650: Tracing param: x1_1#2 = var_18#1 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1825
2025-11-26T12:01:13.051129Z [info ] Detected operation MLIL_CALL_SSA for instruction mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2160
2025-11-26T12:01:13.051546Z [info ] Resolved [memcpy] by address: 0x400510 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2184
2025-11-26T12:01:13.051846Z [warning ] Sink memcpy skipped for return value tracking [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2361
2025-11-26T12:01:13.051945Z [info ] Sink memcpy detected [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2365
2025-11-26T12:01:13.052125Z [info ] Reverse recursive search for: mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1301
2025-11-26T12:01:13.052331Z [info ] Reverse recursive source param definition search for param: x0#1 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1348
2025-11-26T12:01:13.052600Z [info ] Found param: x0#1 = &local [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1088
2025-11-26T12:01:13.052831Z [info ] End of reverse search, src param: &local, forward taint search required [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1364
2025-11-26T12:01:13.053049Z [info ] Reverse recursive source param definition search for param: x1_1#2 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1348
2025-11-26T12:01:13.053240Z [info ] Found param: x1_1#2 = var_18#1 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1088
2025-11-26T12:01:13.053514Z [info ] Found param: var_18#1 = user_input#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1088
2025-11-26T12:01:13.053725Z [info ] End of reverse search, definition: user_input#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1118
2025-11-26T12:01:13.053919Z [info ] Reverse recursive source param definition search for param: x2#1 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1348
2025-11-26T12:01:13.054107Z [info ] Found param: x2#1 = x1#1 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1088
2025-11-26T12:01:13.054393Z [info ] Found param usage in sign extension operation: x1#1 = sx.q(var_1c#1) [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1027
2025-11-26T12:01:13.054526Z [info ] Found param usage: var_1c#1 = user_size#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1068
2025-11-26T12:01:13.054925Z [info ] Found param: var_1c#1 = user_size#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1088
2025-11-26T12:01:13.055166Z [info ] End of reverse search, definition: user_size#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1118
2025-11-26T12:01:13.059472Z [info ] 0x400654: x0#1 passed to: memcpy [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1651
2025-11-26T12:01:13.059692Z [info ] 0x400654: x1_1#2 passed to: memcpy as SRC param [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1632
2025-11-26T12:01:13.059793Z [info ] 0x400654: x2#1 passed to: memcpy as SIZE param [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=1637
2025-11-26T12:01:13.059870Z [info ] Checking if vulnerable to stack overflow bug class ... [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2679
2025-11-26T12:01:13.060011Z [info ] Current instruction : mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2682
2025-11-26T12:01:13.060410Z [info ] Size x2#1 is of type MLIL_VAR_SSA [stackoverflow] file_name=stack_taint_overflow.py line=289
2025-11-26T12:01:13.060871Z [debug ] Chain for x1_1#2: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.060963Z [debug ] ['x1_1#2 = var_18#1', 'var_18#1 = user_input#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.061033Z [debug ] Chain for x2#1: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.061088Z [debug ] ['x2#1 = x1#1', 'x1#1 = sx.q(var_1c#1)', 'var_1c#1 = user_size#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.061143Z [debug ] No common calculations found. [stackoverflow] file_name=stack_taint_overflow.py line=1270
2025-11-26T12:01:13.061213Z [info ] Found independent tainted parameters: {'user_size#0', 'user_input#0'} [stackoverflow] file_name=stack_taint_overflow.py line=1274
2025-11-26T12:01:13.061334Z [error ] Possible type stack overflow detected at 0x400654 | mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] file_name=stack_taint_overflow.py line=307
2025-11-26T12:01:13.061410Z [error ] Size x2#1 was computed from a source operation without bounds checking [stackoverflow] file_name=stack_taint_overflow.py line=310
2025-11-26T12:01:13.061485Z [error ] Dest variable &local was computed with buffer size 16 [stackoverflow] file_name=stack_taint_overflow.py line=313
2025-11-26T12:01:13.063258Z [info ] Saved result to libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001.json [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=4632
2025-11-26T12:01:13.063552Z [info ] Saved result DFG to libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001_dfg.json [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=4638
2025-11-26T12:01:13.063662Z [info ]
-----------------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=4639
2025-11-26T12:01:13.064042Z [info ] 0x400640: Tracing var_1c#1 = user_size#0, instructions to trace: 9 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=3275
2025-11-26T12:01:13.064149Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=3289
2025-11-26T12:01:13.064439Z [info ] 0x400640: Tracing param: var_1c#1 = user_size#0 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.065253Z [info ] 0x400644: Tracing param: x1#1 = sx.q(var_1c#1) [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.065744Z [info ] 0x40064c: Tracing param: x2#1 = x1#1 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.066304Z [info ] 0x40065c: Tracing param: x2_1#2 = zx.q(var_1c#1) [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1825
2025-11-26T12:01:13.066722Z [info ] Detected operation MLIL_CALL_SSA for instruction x0_1#2, mem#2 = 0x400540("Copied: %s (len=%d)\n", x1_2#3, x2_1#2) @ mem#1 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=2160
2025-11-26T12:01:13.066985Z [info ] Resolved [printf] by address: 0x400540 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=2184
2025-11-26T12:01:13.067471Z [warning ] Sink printf skipped for return value tracking [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=2361
2025-11-26T12:01:13.067681Z [info ] Sink printf detected [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=2365
2025-11-26T12:01:13.068068Z [info ] Reverse recursive search for: x0_1#2, mem#2 = 0x400540("Copied: %s (len=%d)\n", x1_2#3, x2_1#2) @ mem#1 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1301
2025-11-26T12:01:13.068797Z [info ] printf with static param: "Copied: %s (len=%d)\n" [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1334
2025-11-26T12:01:13.069070Z [info ] Reverse recursive source param definition search for param: x1_2#3 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1348
2025-11-26T12:01:13.069467Z [info ] Found param: x1_2#3 = &local [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1088
2025-11-26T12:01:13.069706Z [info ] End of reverse search, src param: &local, forward taint search required [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1364
2025-11-26T12:01:13.069941Z [info ] Reverse recursive source param definition search for param: x2_1#2 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1348
2025-11-26T12:01:13.070176Z [info ] Found param usage in sign extension operation: x2_1#2 = zx.q(var_1c#1) [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1027
2025-11-26T12:01:13.070313Z [info ] Found param usage: var_1c#1 = user_size#0 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1068
2025-11-26T12:01:13.070527Z [info ] End of reverse search, definition: var_1c#1 [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1193
2025-11-26T12:01:13.074662Z [info ] 0x40066c: "Copied: %s (len=%d)\n" passed to: printf [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1651
2025-11-26T12:01:13.075342Z [info ] 0x40066c: x1_2#3 passed to: printf as SRC param [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1632
2025-11-26T12:01:13.075449Z [info ] 0x40066c: x2_1#2 passed to: printf as VAR_ARGS param [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=1641
2025-11-26T12:01:13.075522Z [info ] stackoverflow module check passed [stackoverflow] analysis_progress=39.2 file_name=analyzer.py line=2601
2025-11-26T12:01:13.075619Z [info ] printf [stackoverflow] file_name=argstream.py line=24
2025-11-26T12:01:13.075888Z [info ] 0x400648: Tracing x0#1 = &local, instructions to trace: 7 [stackoverflow] analysis_progress=40.5 file_name=analyzer.py line=3275
2025-11-26T12:01:13.075979Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=40.5 file_name=analyzer.py line=3289
2025-11-26T12:01:13.076201Z [info ] 0x400648: Tracing param: x0#1 = &local [stackoverflow] analysis_progress=40.5 file_name=analyzer.py line=1825
2025-11-26T12:01:13.076796Z [info ] 0x400660: Tracing x1_2#3 = &local, instructions to trace: 2 [stackoverflow] analysis_progress=41.9 file_name=analyzer.py line=3275
2025-11-26T12:01:13.076876Z [info ] Forward recursive param use search... [stackoverflow] analysis_progress=41.9 file_name=analyzer.py line=3289
2025-11-26T12:01:13.077098Z [info ] 0x400660: Tracing param: x1_2#3 = &local [stackoverflow] analysis_progress=41.9 file_name=analyzer.py line=1825
2025-11-26T12:01:13.077527Z [info ] 0x400678: Tracing return x0_1#2, instructions to trace: 0 [stackoverflow] analysis_progress=43.2 file_name=analyzer.py line=3275
2025-11-26T12:01:13.077611Z [info ] End of analysis: libmemcpy_overflow-aarch64-linux-gnu.so
-------------------------------------------------------------------------------------
[stackoverflow] analysis_progress=44.6 file_name=analyzer.py line=3809
2025-11-26T12:01:13.077680Z [info ] [stackoverflow] analysis_progress=100 file_name=analyzer.py line=3814Now let’s focus on most important parts of the log. I will refer them in parts
to be easier to follow
2025-11-26T12:01:12.196412Z [debug ] [stackoverflow] analysis_progress=0 engine_version=0.0.17 file_name=__main__.py line=62
Opening main_static2-aarch64-linux-gnu.bndb: 100%|███████| 100/100 [00:00<00:00]
2025-11-26T12:01:12.757899Z [info ] Loaded database: tests/analysis/libload/main_static2-aarch64-linux-gnu.bndb [stackoverflow] line=132
Opening libsink-aarch64-linux-gnu.so.bndb: 100%|█████████| 100/100 [00:00<00:00]
2025-11-26T12:01:12.772404Z [info ] Loaded database: /home/h0rac/unpwnable_things/tests/analysis/libload/libsink-aarch64-linux-gnu.so.bndb [stackoverflow] line=132
2025-11-26T12:01:12.772614Z [info ] Loaded external library: ./libsink-aarch64-linux-gnu.so -> /home/h0rac/unpwnable_things/tests/analysis/libload/libsink-aarch64-linux-gnu.so [stackoverflow] line=334
Opening libmemcpy_overflow-aarch64-linux-gnu.so.bndb: 100%|█| 100/100 [00:00<00:
2025-11-26T12:01:12.788591Z [info ] Loaded database: /home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so.bndb [stackoverflow] line=132
2025-11-26T12:01:12.788922Z [info ] Loaded external library: ./libmemcpy_overflow-aarch64-linux-gnu.so -> /home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so [stackoverflow] line=334
2025-11-26T12:01:12.789175Z [debug ] Skipping system library libc.so.6 for /home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu [stackoverflow] line=272
2025-11-26T12:01:12.857159Z [debug ] [callconv] Skipping call convention fix (database view: /home/h0rac/unpwnable_things/tests/analysis/libload/main_static2-aarch64-linux-gnu.bndb) [stackoverflow] file_name=analyzer.py line=539First we load the libraries and because I already had CFG build for it load database files to speed up analysis for main binary and libraries. We also skip libc.so.6 from analysis because it is not custom library. Call convention is also skipped because aarch64 does it well.
Each analysed file is marked with information which file is currently under analysis.
Next we detect possible sources and sinks in all files
2025-11-26T12:01:12.959899Z [debug ] func_name: main, func_addr: 0x400a14, func_sinks_number: 3, func_sinks: ['strlen', 'printf', 'strlen'], func_sources_number: 1 func_sources: ['fgets'] [stackoverflow] file_name=analyzer.py line=4018
2025-11-26T12:01:12.960007Z [debug ] func_name: dangerous_sink, func_addr: 0x400634, func_sinks_number: 2, func_sinks: ['strcpy', 'printf'], func_sources_number: 0 func_sources: [] [stackoverflow] file_name=analyzer.py line=4018
2025-11-26T12:01:12.960075Z [debug ] func_name: memcpy_overflow_sink, func_addr: 0x400634, func_sinks_number: 2, func_sinks: ['memcpy', 'printf'], func_sources_number: 0 func_sources: [] [stackoverflow] file_name=analyzer.py line=4018One we detect sources/sinks we start analysis of the files
025-11-26T12:01:13.037611Z [info ] Checking if vulnerable to stack overflow bug class ... [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2679
2025-11-26T12:01:13.037744Z [info ] Current instruction : mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=2682
2025-11-26T12:01:13.038413Z [debug ] Chain for x1#1: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.038502Z [debug ] ['x1#1 = var_18#1', 'var_18#1 = user_data#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.038591Z [debug ] Found common parameter: {'user_data#0', 'var_18#1'} [stackoverflow] file_name=stack_taint_overflow.py line=1265
2025-11-26T12:01:13.038718Z [error ] Possible type stack overflow detected at 0x400648 | mem#1 = 0x400530(x0#1, x1#1) @ mem#0 [stackoverflow] file_name=stack_taint_overflow.py line=1869
2025-11-26T12:01:13.038814Z [error ] Variable x1#1 was computed from a source operation without bounds checking [stackoverflow] file_name=stack_taint_overflow.py line=1872
2025-11-26T12:01:13.038896Z [error ] Dest variable &buf was computed with buffer size 16 [stackoverflow] file_name=stack_taint_overflow.py line=1875
2025-11-26T12:01:13.040709Z [info ] Saved result to libtest/stackoverflow/libsink-aarch64-linux-gnu.so_00001.json [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=4632
2025-11-26T12:01:13.041054Z [info ] Saved result DFG to libtest/stackoverflow/libsink-aarch64-linux-gnu.so_00001_dfg.json [stackoverflow] analysis_progress=32.4 file_name=analyzer.py line=4638Here we have information that stackoverflow was detected in libsink library and DFG (Data Flow Graph) was saved in working directory
After that engine is finding new vulnerability in libmemcpy_overflow library and also saves the DFG as file.
025-11-26T12:01:13.059870Z [info ] Checking if vulnerable to stack overflow bug class ... [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2679
2025-11-26T12:01:13.060011Z [info ] Current instruction : mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=2682
2025-11-26T12:01:13.060410Z [info ] Size x2#1 is of type MLIL_VAR_SSA [stackoverflow] file_name=stack_taint_overflow.py line=289
2025-11-26T12:01:13.060871Z [debug ] Chain for x1_1#2: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.060963Z [debug ] ['x1_1#2 = var_18#1', 'var_18#1 = user_input#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.061033Z [debug ] Chain for x2#1: [stackoverflow] file_name=stack_taint_overflow.py line=1261
2025-11-26T12:01:13.061088Z [debug ] ['x2#1 = x1#1', 'x1#1 = sx.q(var_1c#1)', 'var_1c#1 = user_size#0'] [stackoverflow] file_name=stack_taint_overflow.py line=1262
2025-11-26T12:01:13.061143Z [debug ] No common calculations found. [stackoverflow] file_name=stack_taint_overflow.py line=1270
2025-11-26T12:01:13.061213Z [info ] Found independent tainted parameters: {'user_size#0', 'user_input#0'} [stackoverflow] file_name=stack_taint_overflow.py line=1274
2025-11-26T12:01:13.061334Z [error ] Possible type stack overflow detected at 0x400654 | mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0 [stackoverflow] file_name=stack_taint_overflow.py line=307
2025-11-26T12:01:13.061410Z [error ] Size x2#1 was computed from a source operation without bounds checking [stackoverflow] file_name=stack_taint_overflow.py line=310
2025-11-26T12:01:13.061485Z [error ] Dest variable &local was computed with buffer size 16 [stackoverflow] file_name=stack_taint_overflow.py line=313
2025-11-26T12:01:13.063258Z [info ] Saved result to libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001.json [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=4632
2025-11-26T12:01:13.063552Z [info ] Saved result DFG to libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001_dfg.json [stackoverflow] analysis_progress=37.8 file_name=analyzer.py line=4638
Now lets look on the saved files structure:
➜ unpwnable_things git:(prod) ✗ tree libtest
libtest
├── main_static2-aarch64-linux-gnu_00001.log
└── stackoverflow
├── libmemcpy_overflow-aarch64-linux-gnu.so_00001_dfg.json
├── libmemcpy_overflow-aarch64-linux-gnu.so_00001.json
├── libsink-aarch64-linux-gnu.so_00001_dfg.json
└── libsink-aarch64-linux-gnu.so_00001.jsoncat libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001_dfg.json
[
{
"taint_dfg": [
[
"0x400a94",
"fgets-x0_9#4",
[
"x0_8#3",
"0x100",
"x2#1"
],
"main"
],
[
"0x400a88",
"main",
"x0_8#3 = &input",
"main"
],
[
"0x400a8c",
"main",
"x2#1 = x1_1#1",
"main"
],
[
"0x400a84",
"main",
"x1_1#1 = [stdin].q @ mem#2",
"main"
],
[
"0x400ae8",
"main",
"x2#2 = \u03d5(envp#0, x2#1)",
"main"
],
[
"0x400af0",
"main",
"x2#3 = \u03d5(x2#1, x2#2)",
"main"
],
[
"0x400af0",
"main",
"x1#6 = \u03d5(x1_1#1, x1#5)",
"main"
],
[
"0x400ae0",
"main",
"x1_3#3 = zx.q(user_len#1)",
"main"
],
[
"0x400a44",
"main",
"user_len#1 = x0_4#15",
"main"
],
[
"0x400a50",
"main",
"x1#4 = zx.q(user_len#1)",
"main"
],
[
"0x400ae8",
"main",
"x1#5 = \u03d5(x1_3#3, x1#4)",
"main"
],
[
"0x400ae8",
"main",
"user_len#2 = \u03d5(user_len#0, user_len#1)",
"main"
],
[
"0x400a3c",
"main",
"x0_3#14 = user_data#1",
"main"
],
[
"0x400a38",
"main",
"user_data#1 = x0_2#13",
"main"
],
[
"0x400a34",
"main",
"x0_2#13 = [x0_1#12 + 8].q @ mem#0",
"main"
],
[
"0x400ab4",
"main",
"x0_11#5 = &input",
"main"
],
[
"0x400ab8",
"x0_12#6 = strcspn",
[
"x0_11#5",
"0x400b28"
],
"main"
],
[
"0x400abc",
"main",
"x1_2#2 = x0_12#6",
"main"
],
[
"0x400ac4",
"main",
"[&input + x1_2#2].b = 0 @ mem#4 -> mem#5",
"main"
],
[
"0x400ac8",
"main",
"x0_13#7 = &input",
"main"
],
[
"0x400acc",
"strlen-x0_14#8",
[
"x0_13#7"
],
"main"
],
[
"0x400ad0",
"main",
"user_len#1 = x0_14#8",
"main"
],
[
"0x400ae4",
"memcpy_overflow_sink",
[
"x0_16#10",
"x1_3#3"
],
"main"
],
[
"0x400ad4",
"main",
"x0_15#9 = &input",
"main"
],
[
"0x400ad8",
"dangerous_sink",
[
"x0_15#9"
],
"main"
],
[
"0x400adc",
"main",
"x0_16#10 = &input",
"main"
],
[
"0x400aa0",
"main",
"x0_10#11 = 1",
"main"
],
[
"0x400af0",
"main",
"x0_10#20 = \u03d5(x0_10#11, x0_10#19)",
"main"
],
[
"0x400af0",
"main",
"return x0_10#20",
"main"
],
[
"0x400ae8",
"main",
"x0_10#19 = 0",
"main"
],
[
"0x40063c",
"dangerous_sink",
"var_18#1 = user_data#0",
"dangerous_sink"
],
[
"0x400644",
"dangerous_sink",
"x1#1 = var_18#1",
"dangerous_sink"
],
[
"0x400648",
"strcpy",
[
"x0#1",
"x1#1"
],
"dangerous_sink"
],
[
"0x400640",
"dangerous_sink",
"x0#1 = &buf",
"dangerous_sink"
],
[
"0x400650",
"dangerous_sink",
"x1_1#2 = &buf",
"dangerous_sink"
],
[
"0x40065c",
"printf-x0_1#2",
[
"\"Copied data: %s\\n\"",
"x1_1#2"
],
"dangerous_sink"
],
[
"0x40063c",
"memcpy_overflow_sink",
"var_18#1 = user_input#0",
"memcpy_overflow_sink"
],
[
"0x400650",
"memcpy_overflow_sink",
"x1_1#2 = var_18#1",
"memcpy_overflow_sink"
],
[
"0x400654",
"memcpy",
[
"x0#1",
"x1_1#2",
"x2#1"
],
"memcpy_overflow_sink"
],
[
"0x400648",
"memcpy_overflow_sink",
"x0#1 = &local",
"memcpy_overflow_sink"
],
[
"0x40064c",
"memcpy_overflow_sink",
"x2#1 = x1#1",
"memcpy_overflow_sink"
],
[
"0x400644",
"memcpy_overflow_sink",
"x1#1 = sx.q(var_1c#1)",
"memcpy_overflow_sink"
],
[
"0x400640",
"memcpy_overflow_sink",
"var_1c#1 = user_size#0",
"memcpy_overflow_sink"
]
],
"severity": "HIGH",
"instruction": "mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0",
"instruction_address": "0x400654",
"dest": "&local",
"dest_addr": "0x400648",
"source": "x2#1",
"source_addr": "0x400654",
"vuln_description": "Size [x2#1] was computed from a source operation without bounds checking. Dest variable [&local] was computed with buffer size 16",
"module": "stackoverflow",
"library": "/home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so.bndb"
}
]% We have information that fgets is our source of data and our DFG graphs for library and main binary as single flow in the table. We also have detailed description of the detected bug.
Now lets on the second found bug:
cat libtest/stackoverflow/libmemcpy_overflow-aarch64-linux-gnu.so_00001_dfg.json
[
{
"taint_dfg": [
[
"0x400a94",
"fgets-x0_9#4",
[
"x0_8#3",
"0x100",
"x2#1"
],
"main"
],
[
"0x400a88",
"main",
"x0_8#3 = &input",
"main"
],
[
"0x400a8c",
"main",
"x2#1 = x1_1#1",
"main"
],
[
"0x400a84",
"main",
"x1_1#1 = [stdin].q @ mem#2",
"main"
],
[
"0x400ae8",
"main",
"x2#2 = \u03d5(envp#0, x2#1)",
"main"
],
[
"0x400af0",
"main",
"x2#3 = \u03d5(x2#1, x2#2)",
"main"
],
[
"0x400af0",
"main",
"x1#6 = \u03d5(x1_1#1, x1#5)",
"main"
],
[
"0x400ae0",
"main",
"x1_3#3 = zx.q(user_len#1)",
"main"
],
[
"0x400a44",
"main",
"user_len#1 = x0_4#15",
"main"
],
[
"0x400a50",
"main",
"x1#4 = zx.q(user_len#1)",
"main"
],
[
"0x400ae8",
"main",
"x1#5 = \u03d5(x1_3#3, x1#4)",
"main"
],
[
"0x400ae8",
"main",
"user_len#2 = \u03d5(user_len#0, user_len#1)",
"main"
],
[
"0x400a3c",
"main",
"x0_3#14 = user_data#1",
"main"
],
[
"0x400a38",
"main",
"user_data#1 = x0_2#13",
"main"
],
[
"0x400a34",
"main",
"x0_2#13 = [x0_1#12 + 8].q @ mem#0",
"main"
],
[
"0x400ab4",
"main",
"x0_11#5 = &input",
"main"
],
[
"0x400ab8",
"x0_12#6 = strcspn",
[
"x0_11#5",
"0x400b28"
],
"main"
],
[
"0x400abc",
"main",
"x1_2#2 = x0_12#6",
"main"
],
[
"0x400ac4",
"main",
"[&input + x1_2#2].b = 0 @ mem#4 -> mem#5",
"main"
],
[
"0x400ac8",
"main",
"x0_13#7 = &input",
"main"
],
[
"0x400acc",
"strlen-x0_14#8",
[
"x0_13#7"
],
"main"
],
[
"0x400ad0",
"main",
"user_len#1 = x0_14#8",
"main"
],
[
"0x400ae4",
"memcpy_overflow_sink",
[
"x0_16#10",
"x1_3#3"
],
"main"
],
[
"0x400ad4",
"main",
"x0_15#9 = &input",
"main"
],
[
"0x400ad8",
"dangerous_sink",
[
"x0_15#9"
],
"main"
],
[
"0x400adc",
"main",
"x0_16#10 = &input",
"main"
],
[
"0x400aa0",
"main",
"x0_10#11 = 1",
"main"
],
[
"0x400af0",
"main",
"x0_10#20 = \u03d5(x0_10#11, x0_10#19)",
"main"
],
[
"0x400af0",
"main",
"return x0_10#20",
"main"
],
[
"0x400ae8",
"main",
"x0_10#19 = 0",
"main"
],
[
"0x40063c",
"dangerous_sink",
"var_18#1 = user_data#0",
"dangerous_sink"
],
[
"0x400644",
"dangerous_sink",
"x1#1 = var_18#1",
"dangerous_sink"
],
[
"0x400648",
"strcpy",
[
"x0#1",
"x1#1"
],
"dangerous_sink"
],
[
"0x400640",
"dangerous_sink",
"x0#1 = &buf",
"dangerous_sink"
],
[
"0x400650",
"dangerous_sink",
"x1_1#2 = &buf",
"dangerous_sink"
],
[
"0x40065c",
"printf-x0_1#2",
[
"\"Copied data: %s\\n\"",
"x1_1#2"
],
"dangerous_sink"
],
[
"0x40063c",
"memcpy_overflow_sink",
"var_18#1 = user_input#0",
"memcpy_overflow_sink"
],
[
"0x400650",
"memcpy_overflow_sink",
"x1_1#2 = var_18#1",
"memcpy_overflow_sink"
],
[
"0x400654",
"memcpy",
[
"x0#1",
"x1_1#2",
"x2#1"
],
"memcpy_overflow_sink"
],
[
"0x400648",
"memcpy_overflow_sink",
"x0#1 = &local",
"memcpy_overflow_sink"
],
[
"0x40064c",
"memcpy_overflow_sink",
"x2#1 = x1#1",
"memcpy_overflow_sink"
],
[
"0x400644",
"memcpy_overflow_sink",
"x1#1 = sx.q(var_1c#1)",
"memcpy_overflow_sink"
],
[
"0x400640",
"memcpy_overflow_sink",
"var_1c#1 = user_size#0",
"memcpy_overflow_sink"
]
],
"severity": "HIGH",
"instruction": "mem#1 = 0x400510(x0#1, x1_1#2, x2#1) @ mem#0",
"instruction_address": "0x400654",
"dest": "&local",
"dest_addr": "0x400648",
"source": "x2#1",
"source_addr": "0x400654",
"vuln_description": "Size [x2#1] was computed from a source operation without bounds checking. Dest variable [&local] was computed with buffer size 16",
"module": "stackoverflow",
"library": "/home/h0rac/unpwnable_things/tests/analysis/libload/libmemcpy_overflow-aarch64-linux-gnu.so.bndb"
}
]% Perfect we have similar flow from source of fgets to the vulnerable memcpy when user is able to control size parameter.
Hope this example shows you that we seriously finding bugs via ByteRay engine and services. In case of any technical questions please contact me via grzegorz@byteray.co.uk email address