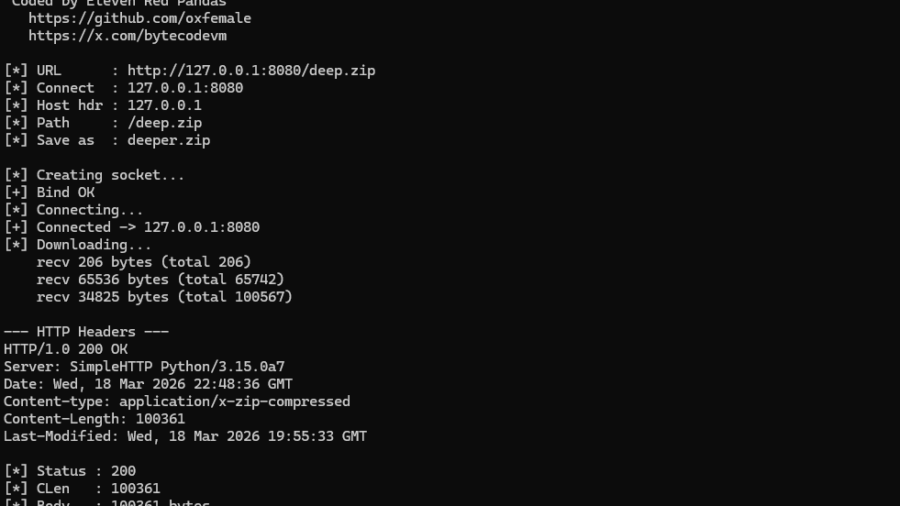
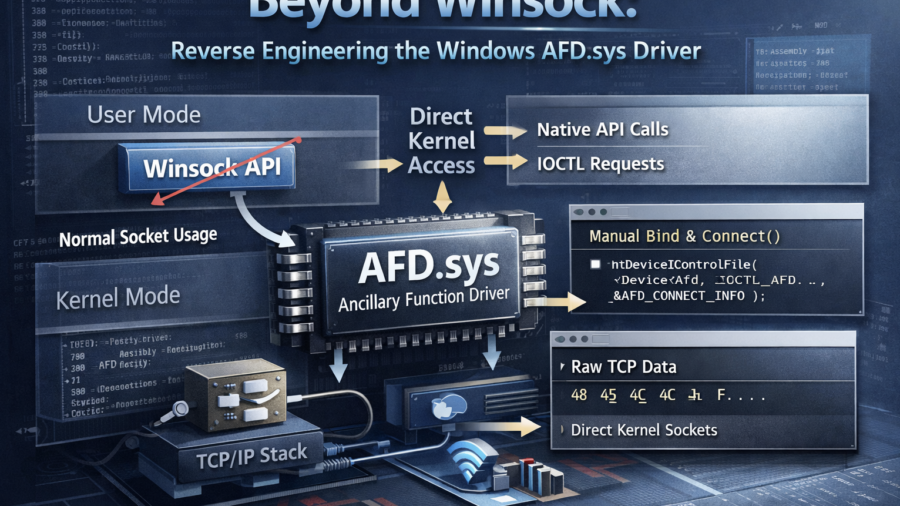
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.
Peeling Back the Socket Layer: Reverse Engineering Windows AFD.sys
The research reverse-engineers Windows AFD.sys, showing how TCP sockets can be created, connected, and used by sending handcrafted IOCTL requests directly to the kernel driver—completely bypassing the Winsock networking API.