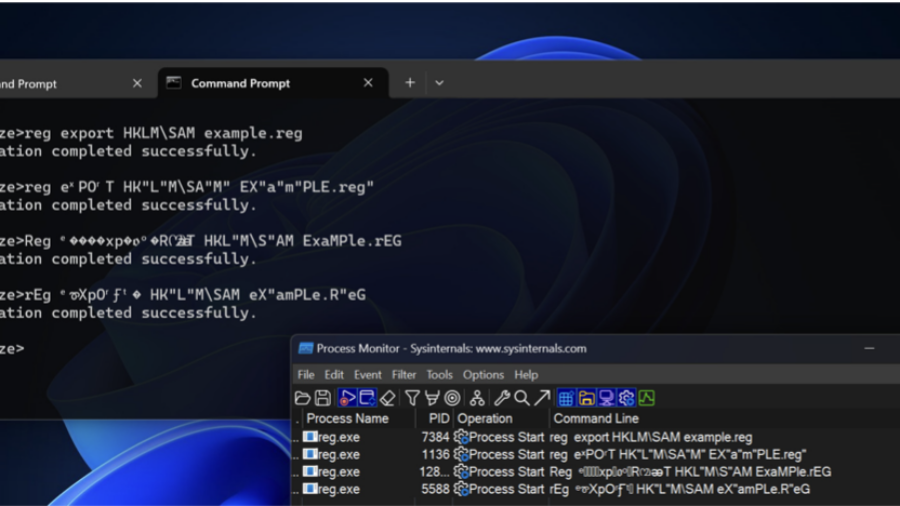
How attackers can bypass AV and EDR detections by obfuscating command-line arguments. By exploiting parsing quirks in executables, small changes to parameters can hide malicious intent while the command still executes normally.
Investigating Windows File System Artifacts Under C:\Windows
The article explores forensic artifacts stored under the C:\Windows directory in Windows 10 and 11. It explains how system files and OS-generated traces can reveal executed programs, user activity, and potential data exfiltration during forensic investigations.
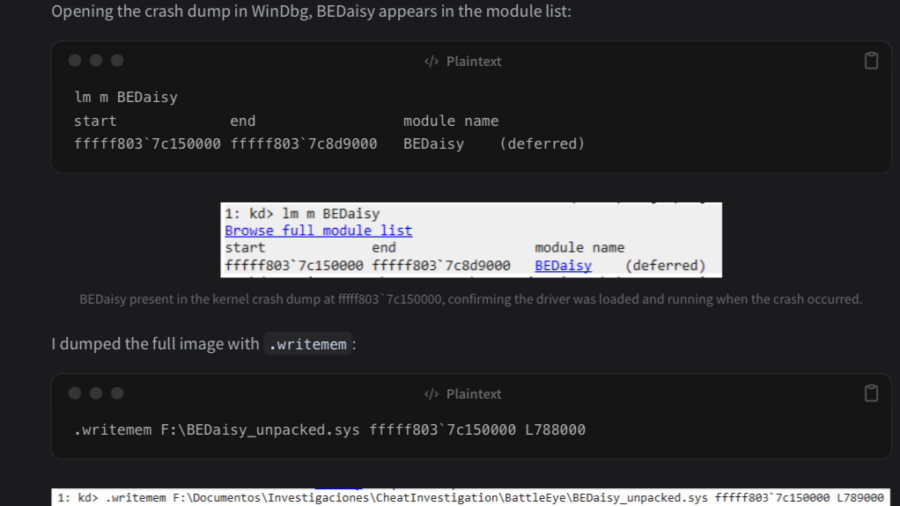
Reversing BEDaisy.sys: Static Analysis of BattlEye’s Kernel Anti-Cheat Driver
The article analyzes the Windows kernel driver BEDaisy.sys, used by BattlEye anti-cheat. Through static reverse engineering, it explores driver architecture, APC usage, hardware fingerprinting, import handling, and detection mechanisms used to monitor system activity.
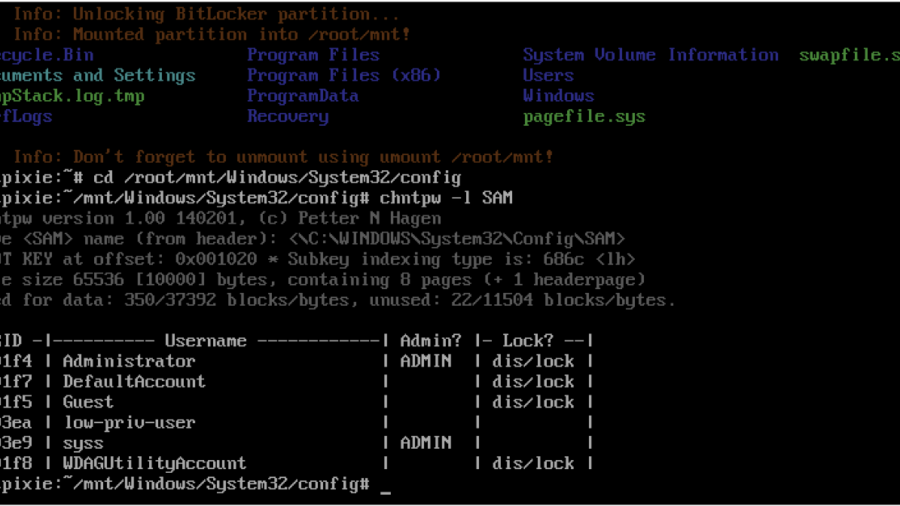
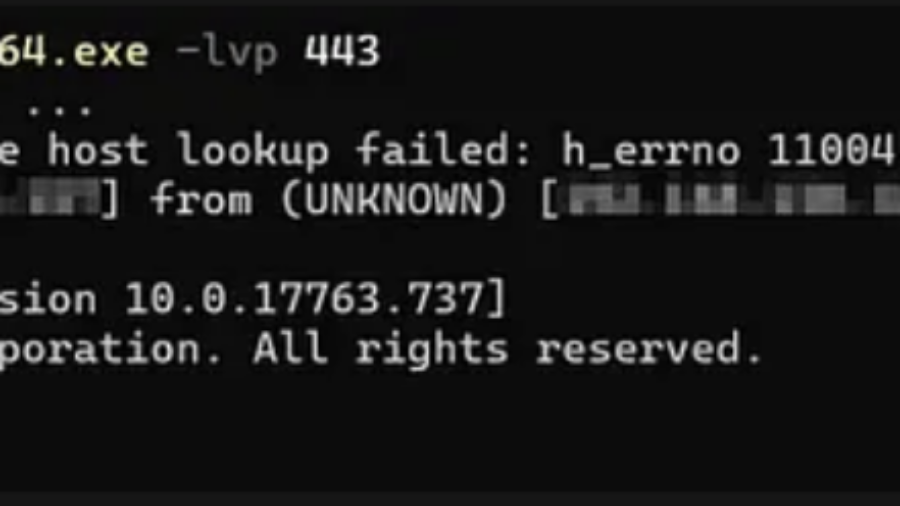
Windows Local Privilege Escalation through the bitpixie Vulnerability
The article explains the Bitpixie vulnerability in Windows Boot Manager that allows attackers to bypass BitLocker encryption. By abusing a PXE soft reboot flaw, the BitLocker key remains in memory, enabling extraction of the VMK and potential privilege escalation.
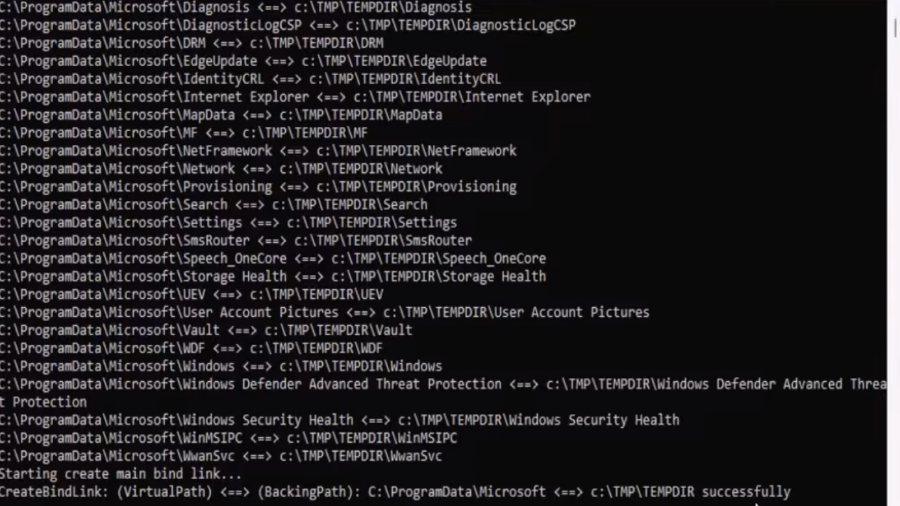
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
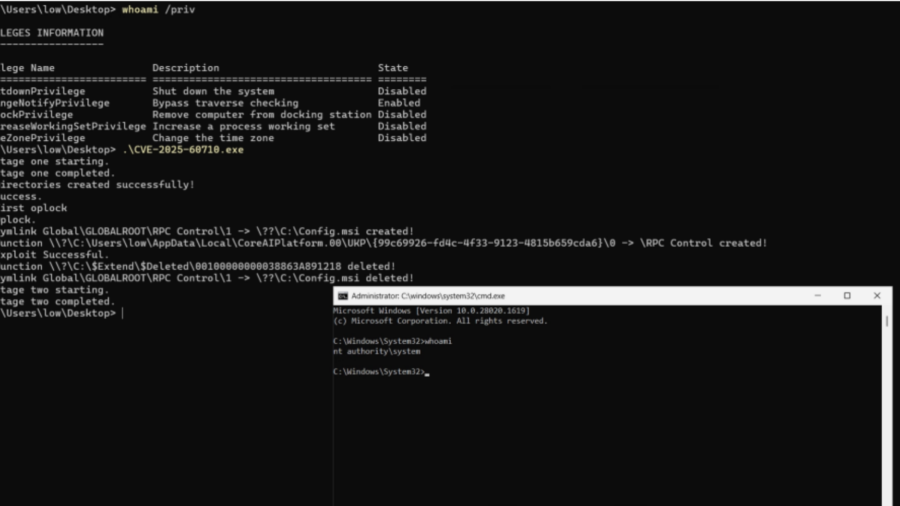
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.
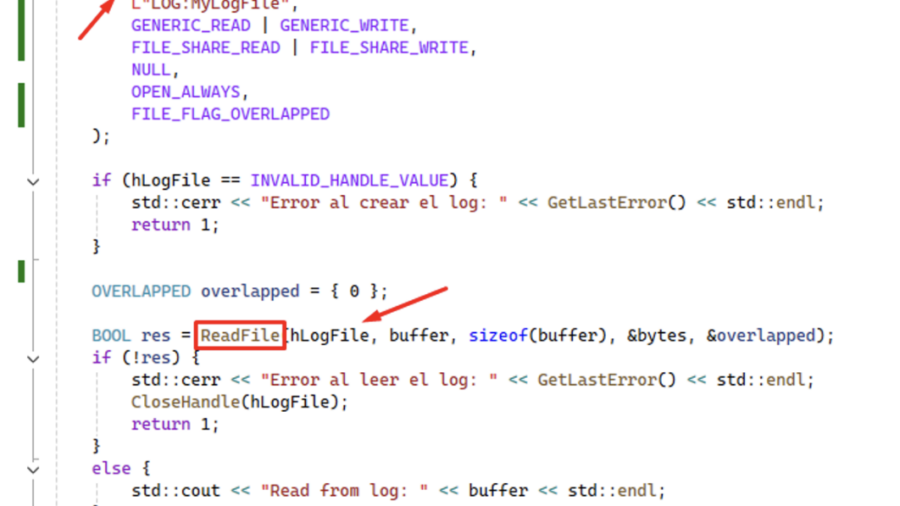
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
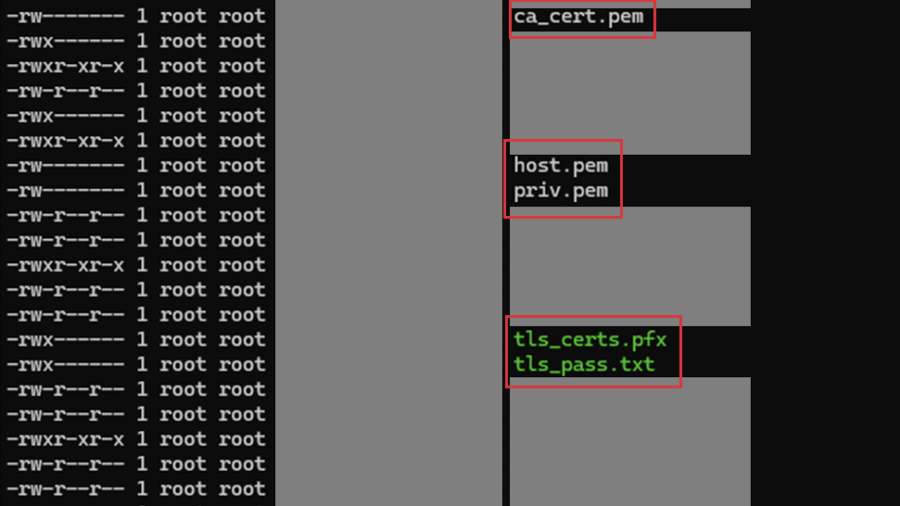
Multiple vulnerabilities in CPSD CryptoPro Secure Disk for BitLocker
SEC Consult found two high-impact vulnerabilities in CryptoPro Secure Disk for BitLocker (<7.6.6/7.7.1). An attacker with physical access can bypass integrity checks to gain root access (CVE-2025-10010) and read sensitive network data stored in cleartext. Patches are available.
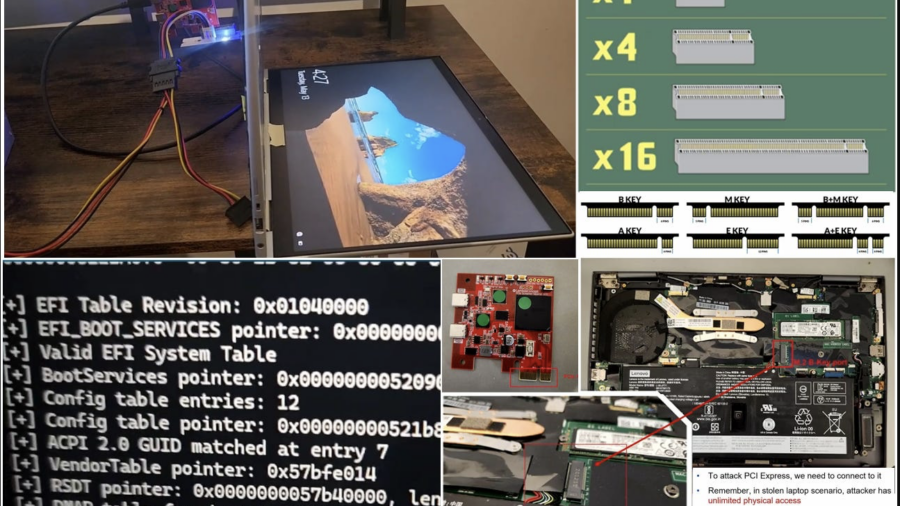
Hacking a stolen laptop: bypassing Windows security (BitLocker etc.) using PCI connector.
The article outlines security researcher Pierre-Nicolas Allard-Coutu’s demonstration of attacking a stolen Windows laptop using a PCIe connector to bypass protections like BitLocker, TPM, and Kernel DMA Protection, showing how to gain SYSTEM access.