The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
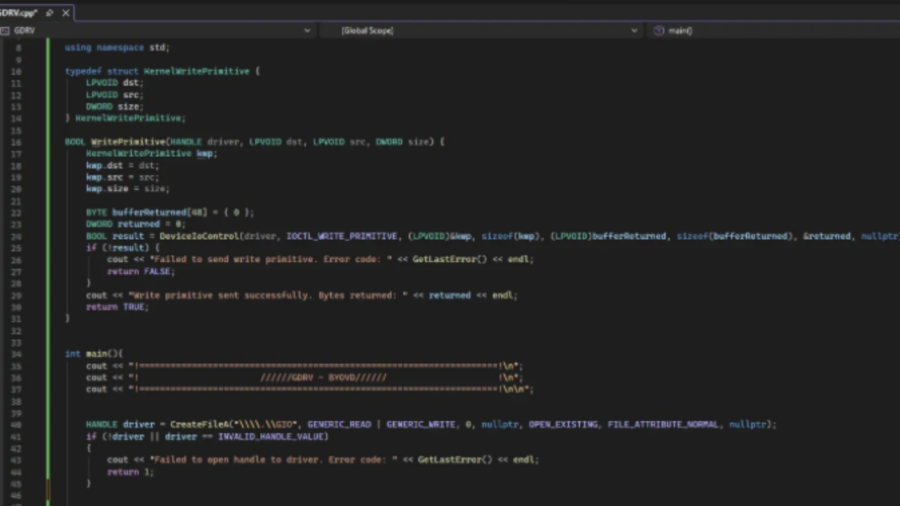
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
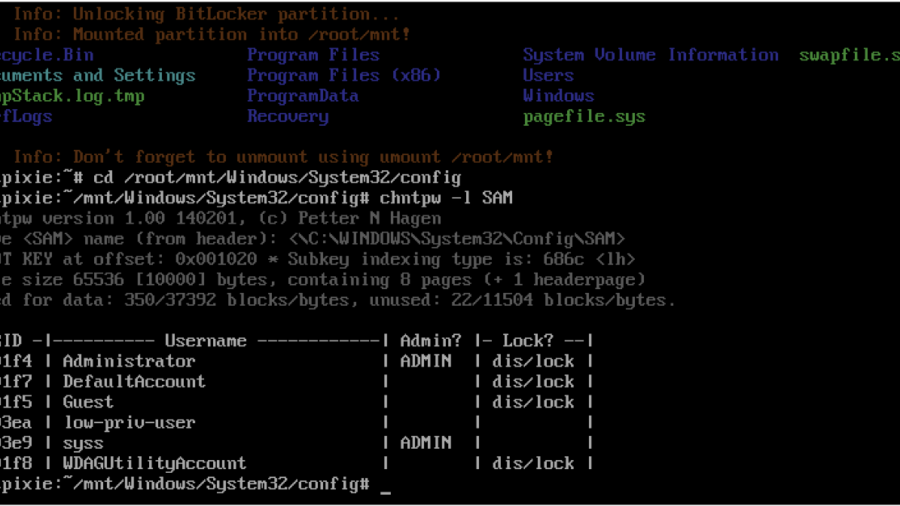
Windows Local Privilege Escalation through the bitpixie Vulnerability
The article explains the Bitpixie vulnerability in Windows Boot Manager that allows attackers to bypass BitLocker encryption. By abusing a PXE soft reboot flaw, the BitLocker key remains in memory, enabling extraction of the VMK and potential privilege escalation.
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
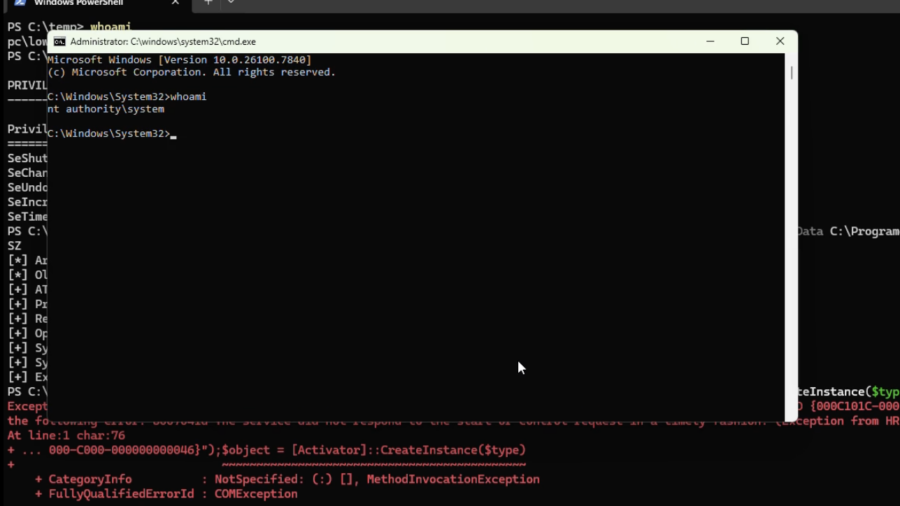
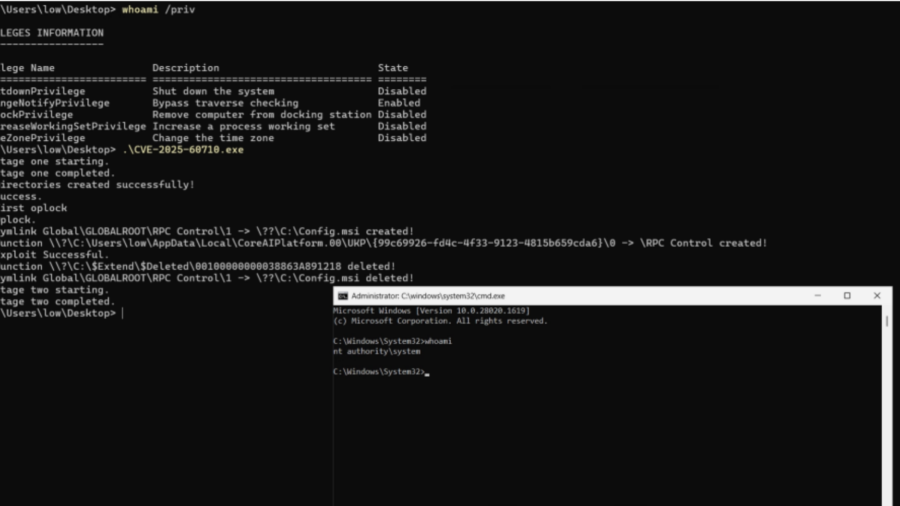
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.
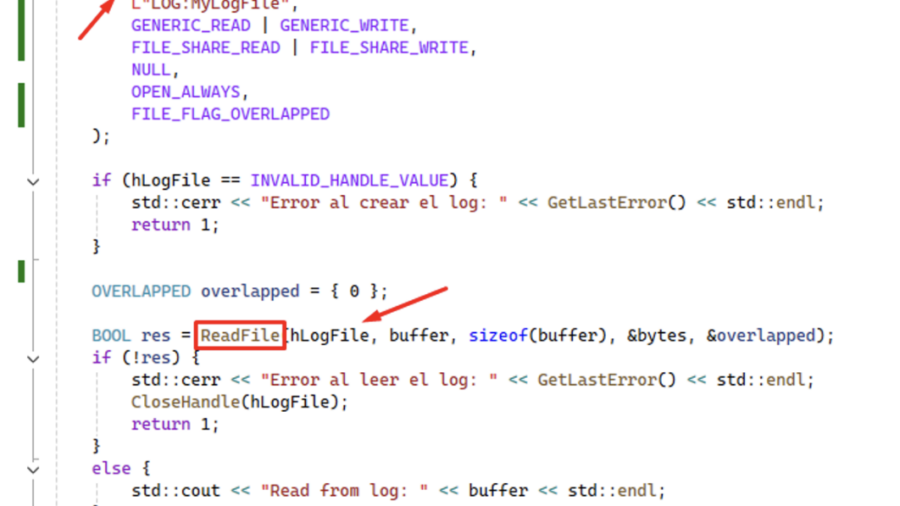
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
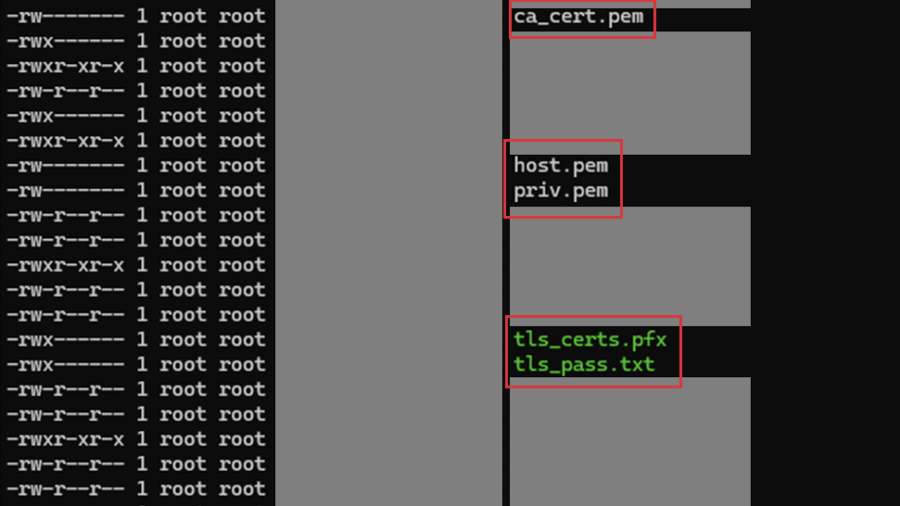
Multiple vulnerabilities in CPSD CryptoPro Secure Disk for BitLocker
SEC Consult found two high-impact vulnerabilities in CryptoPro Secure Disk for BitLocker (<7.6.6/7.7.1). An attacker with physical access can bypass integrity checks to gain root access (CVE-2025-10010) and read sensitive network data stored in cleartext. Patches are available.
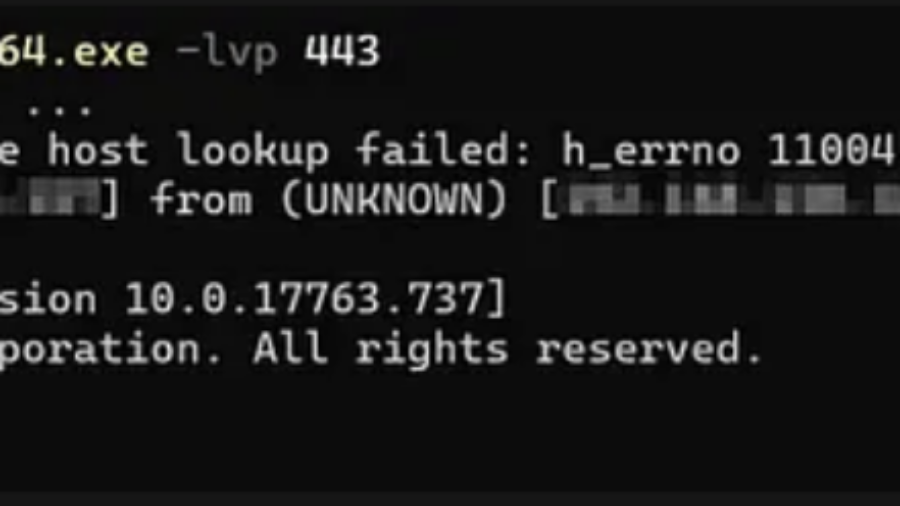
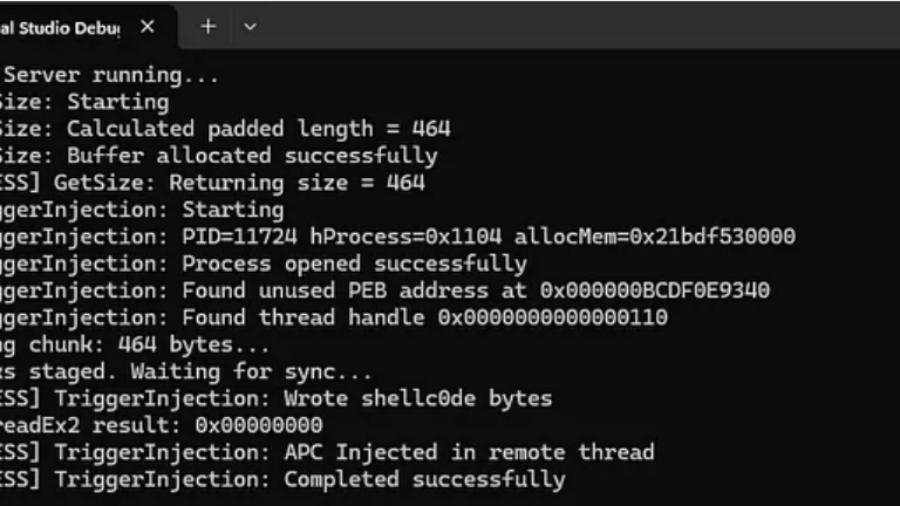
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
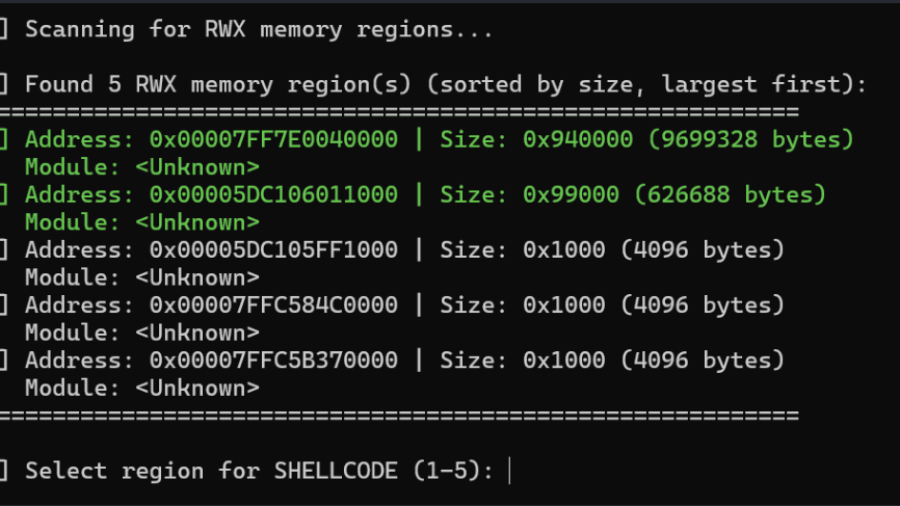
Living off the Process
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.