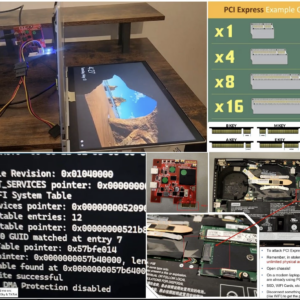
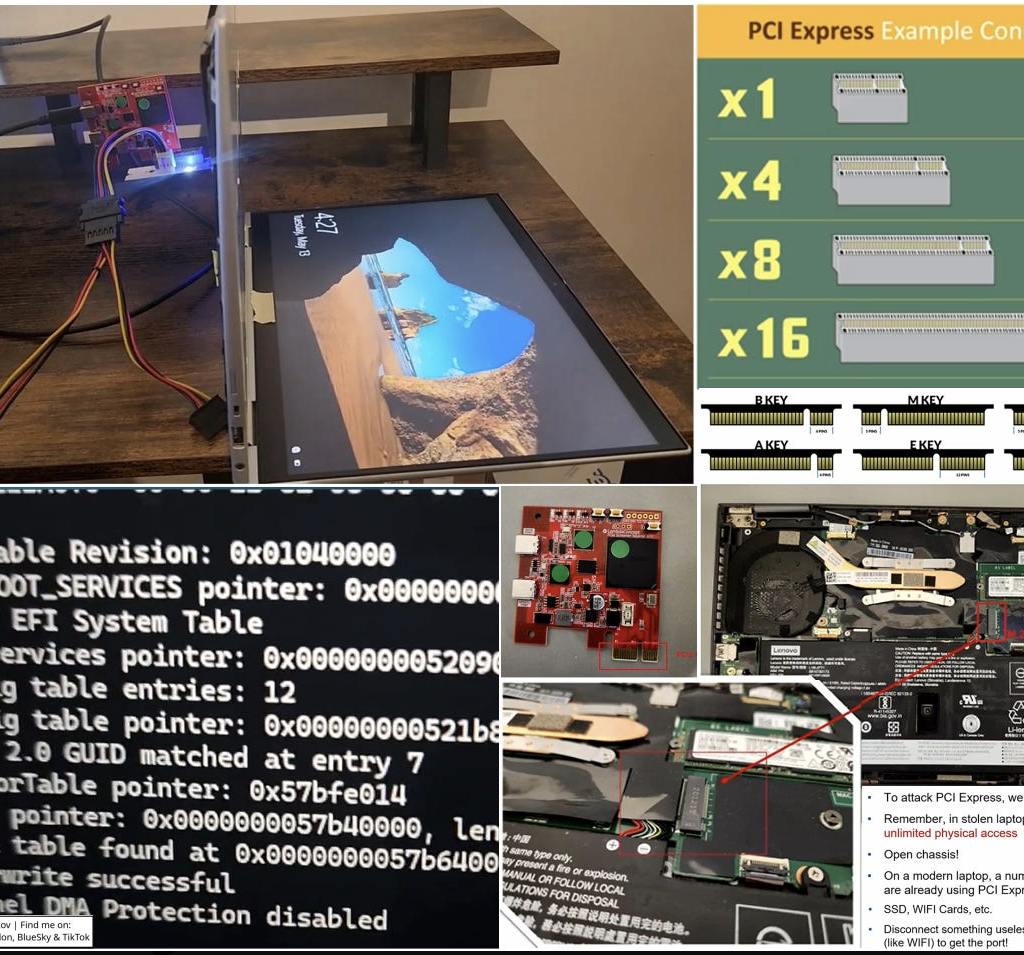
Security researcher Pierre-Nicolas Allard-Coutu presented in his talk ways to attack a stolen Windows laptop, even when modern security features like BitLocker, TPM, and Kernel DMA Protection are enabled.
Using a PCI Express connector, some tooling, and an understanding of the boot process, the author demonstrates how each feature can be disabled or bypassed to gain SYSTEM-level access to the operating system.
If you use TPM-only BitLocker (and in 99% of cases, you do), it’s literally not a problem for an attacker: BitLocker auto-decrypts with TPM-only setups, so the attacker just waits for Windows to boot – then injects code into memory before the OS fully loads. Smart, fast and elegant 🙂
Practical and very useful results of extensive security research, development, and creative thinking. Enjoy the video, and maybe enable a BitLocker PIN!
More details:
Stolen Laptops A brief overview of modern physical access attacks [Youtube]: https://lnkd.in/dtqQdQpq
DMAReaper [Github]: https://github.com/PN-Tester/DMAReaper
FirstStrike [Github]: https://github.com/PN-Tester/FirstStrike