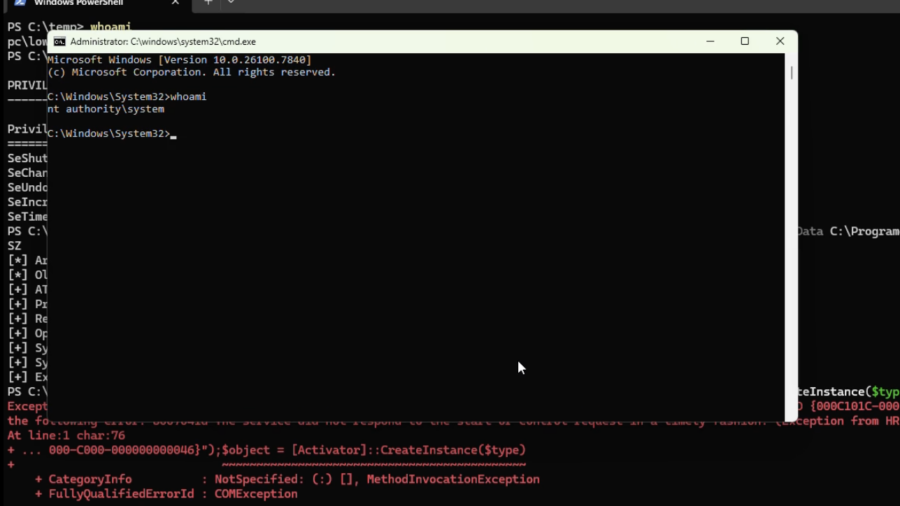
The article explores a red-team research project called “RegPwn,” showing how weaknesses in Windows registry handling can be abused to achieve privilege escalation or persistence, and discusses why the technique has now been mitigated or rendered ineffective.