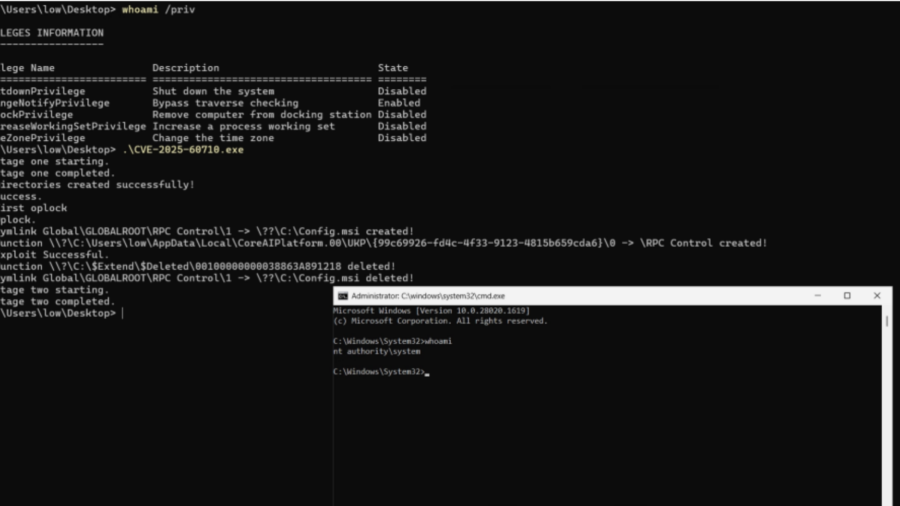
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.
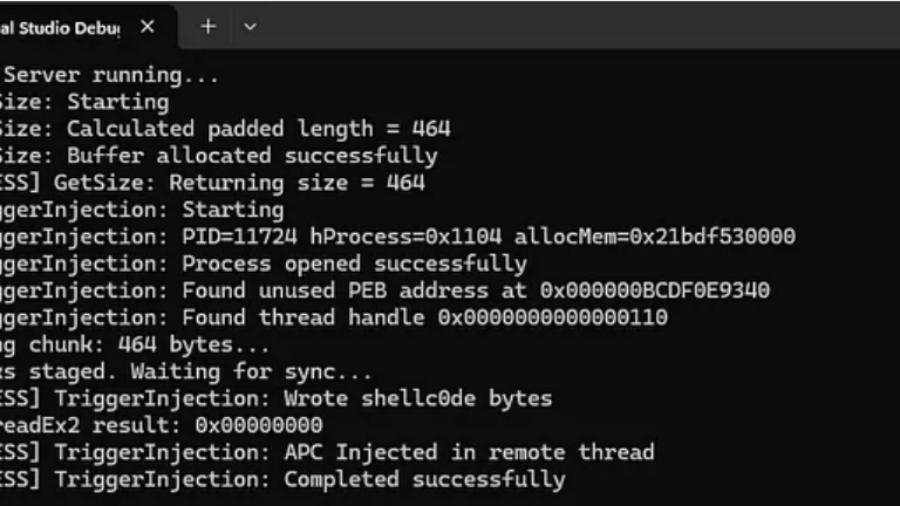
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
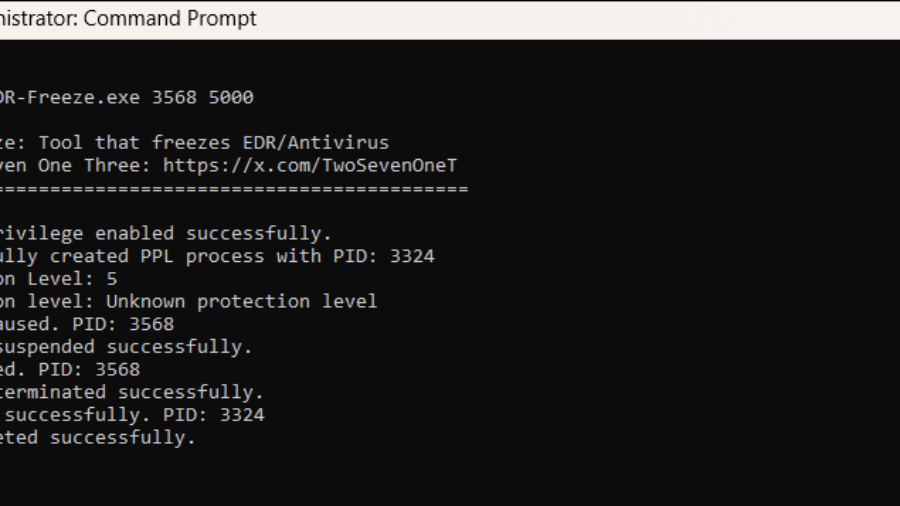
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.