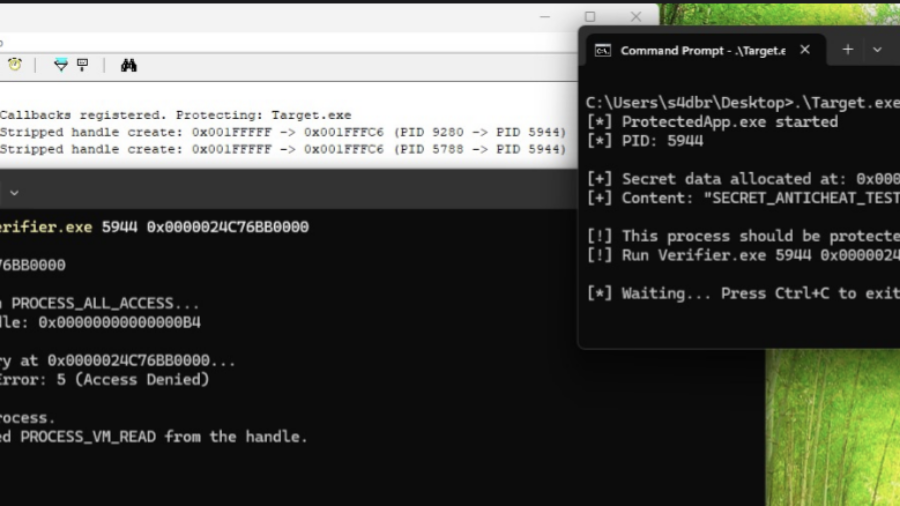
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
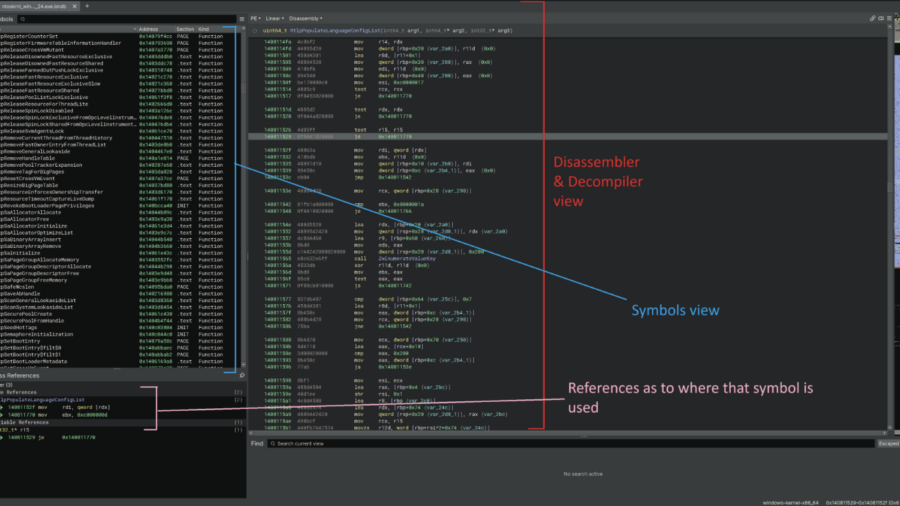
Reverse engineering undocumented Windows Kernel features to work with the EDR
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
Hacking a Bluetooth Printer Server: GATT to UART Adapter?
Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.
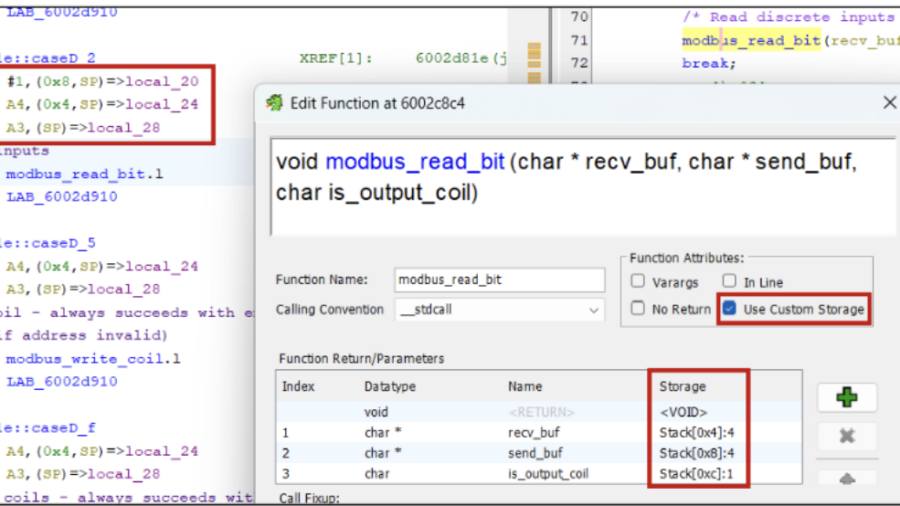
Taming the dragon: reverse engineering firmware with Ghidra
The article explains how to reverse engineer embedded firmware using Ghidra, covering techniques for loading firmware, identifying CPU architectures, analyzing functions, and using scripts/plugins to understand device logic and discover vulnerabilities.
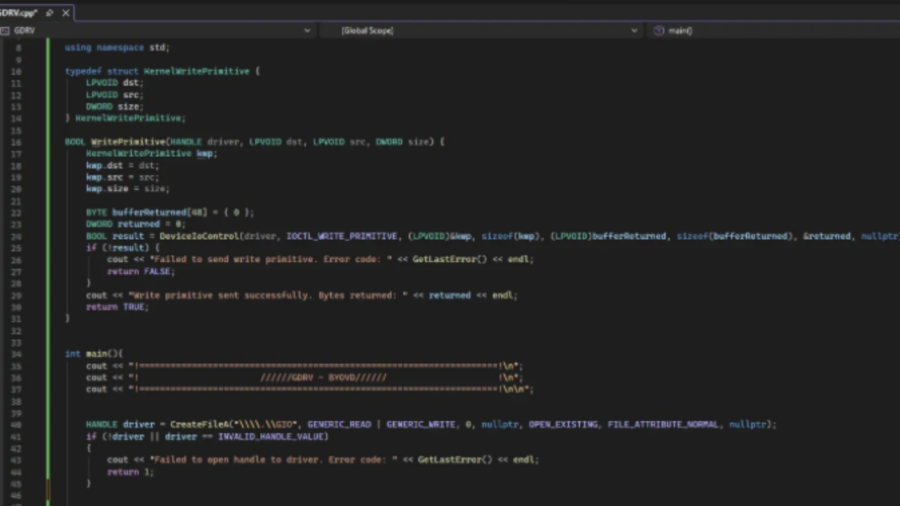
Exploiting a Kernel Read/Write Primitive using BYOVD
The article explains how attackers exploit a vulnerable signed driver (BYOVD) to obtain a kernel read/write primitive. It shows how unsafe IOCTL handlers allow manipulating kernel memory and abusing driver functionality for offensive operations.
Rooting the TP-Link Tapo C200 Rev.5
A analyze the TP-Link Tapo C200 camera firmware by dumping flash via UART and U-Boot, reversing AES-encrypted rootfs headers, and modifying the firmware to gain remote root access for deeper dynamic security analysis of the device.