“Silent Harvest” explains how attackers can quietly extract sensitive Windows secrets such as credentials and security keys by abusing legitimate registry and system mechanisms, avoiding LSASS dumping and bypassing many common EDR detections.
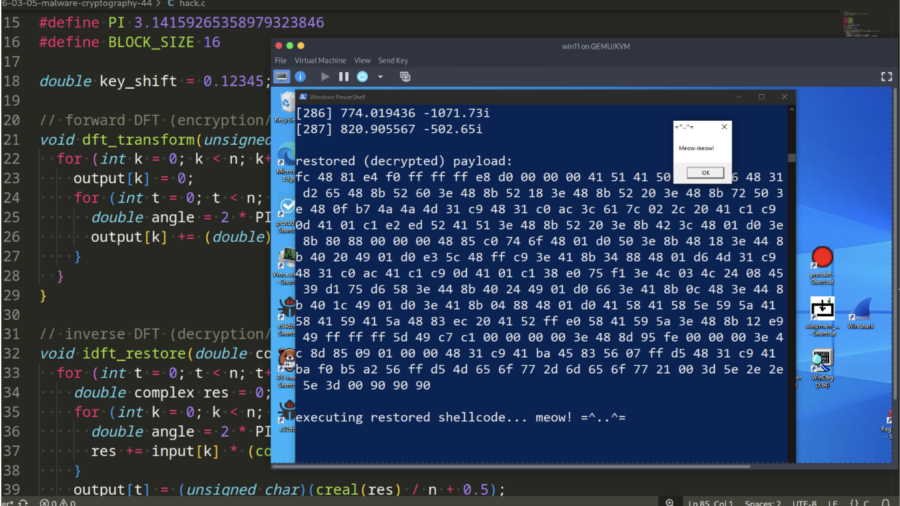
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.
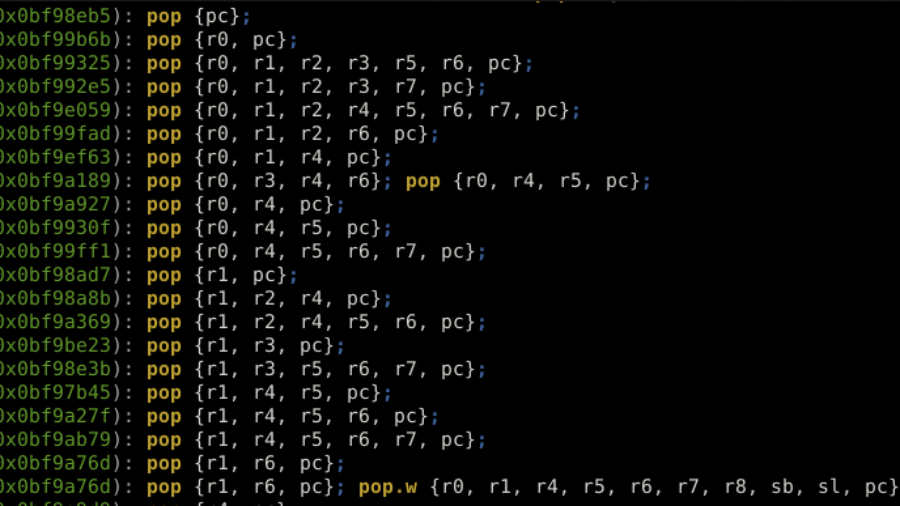
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.
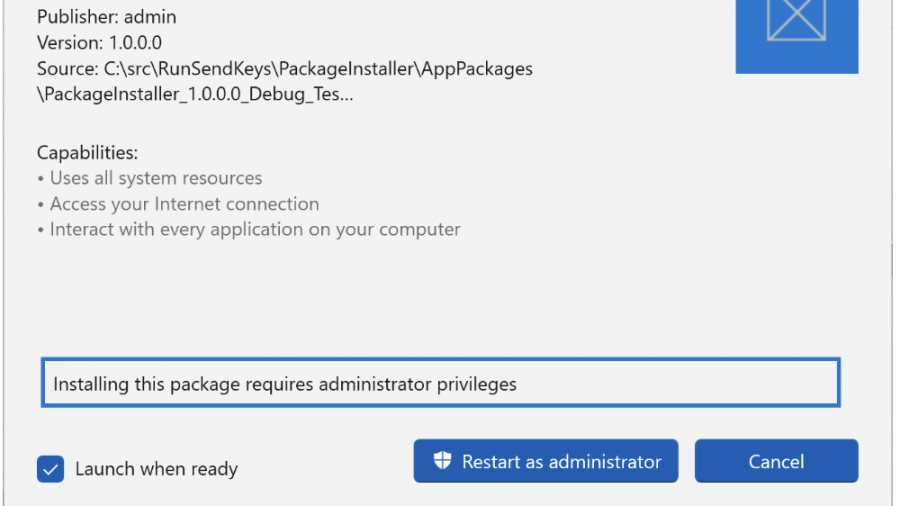
Bypassing Administrator Protection by Abusing UI Access
Windows “Administrator Protection” introduces a stronger admin model, but researchers found multiple privilege-escalation bypasses caused by legacy UAC behavior and UIAccess mechanisms. The issues allowed silent elevation in some cases and were later patched.