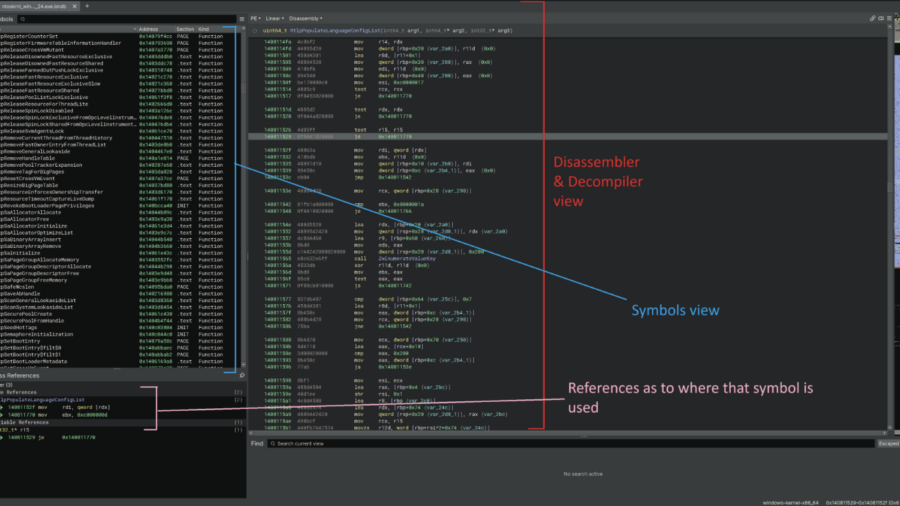
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
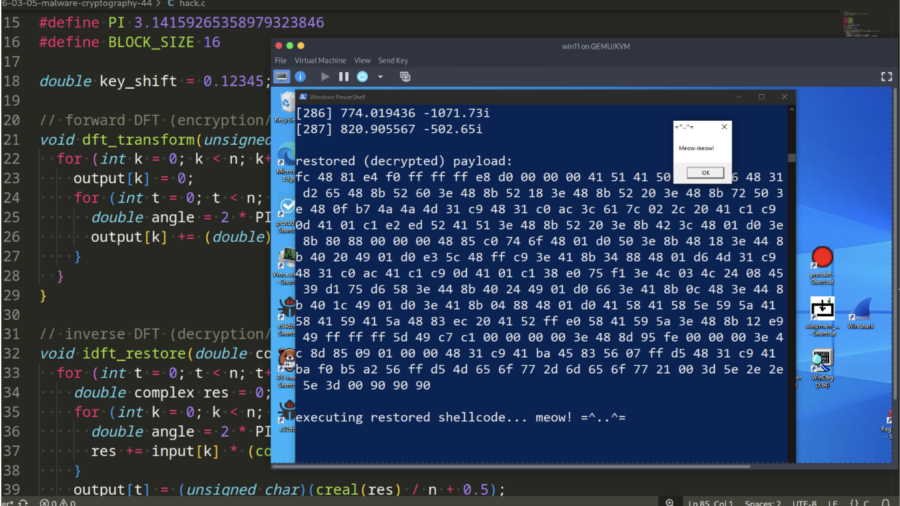
Malware and cryptography 44 – encrypt/decrypt payload via Discrete Fourier Transform. Simple C example.
Demonstration how malware can encrypt and decrypt payloads using the Discrete Fourier Transform (DFT). It provides a simple C example showing how mathematical transforms can hide shellcode and help evade static signature-based detection.