Reverse engineering a Bluetooth printer server reveals multiple security flaws, including exposed debug interfaces and insecure GATT services, enabling unauthenticated remote code execution with root privileges via Bluetooth or network access.
Blinkenlights 2.0: Reverse Engineering a Smartwatch via Screen Signals
Reverse engineering a cheap smartwatch and reviving the classic “blinkenlights” attack to extract firmware through screen update patterns, revealing weaknesses in OTA update mechanisms, BLE communication, and embedded device security design.
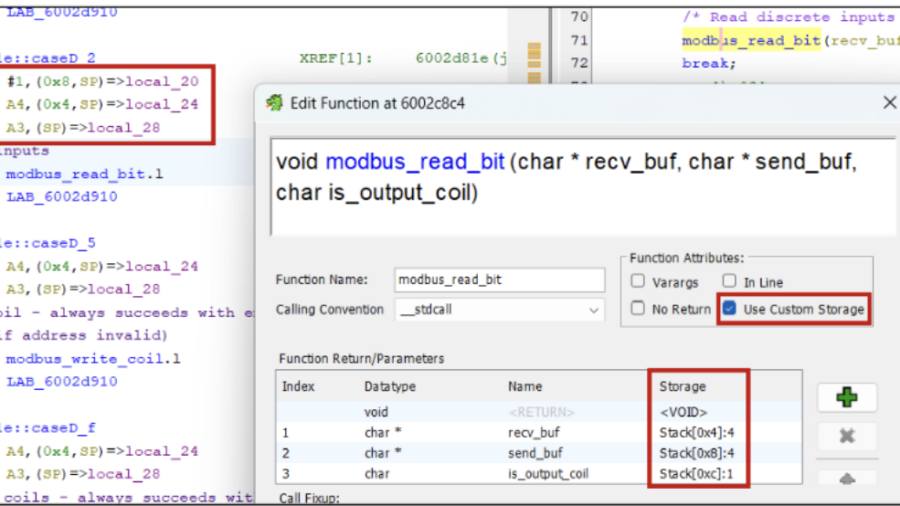
Taming the dragon: reverse engineering firmware with Ghidra
The article explains how to reverse engineer embedded firmware using Ghidra, covering techniques for loading firmware, identifying CPU architectures, analyzing functions, and using scripts/plugins to understand device logic and discover vulnerabilities.
Physical Network Sniffing: Capturing Ethernet Traffic with Simple Alligator Clips
The article demonstrates how Ethernet traffic can be passively intercepted at the physical layer using simple tools like alligator clips attached to network cables. It highlights risks of exposed wiring and shows how attackers can capture unencrypted traffic.
Understanding CPU Cache Hierarchy: Why Modern Processors Use Multiple Cache Levels
The article explains why modern CPUs use multiple cache levels (L1, L2, L3) instead of a single large cache. It discusses the trade-off between cache size and latency and shows how a cache hierarchy balances speed, capacity, and efficiency.
Rooting the TP-Link Tapo C200 Rev.5
A analyze the TP-Link Tapo C200 camera firmware by dumping flash via UART and U-Boot, reversing AES-encrypted rootfs headers, and modifying the firmware to gain remote root access for deeper dynamic security analysis of the device.
Breaking Flash Encryption on Espressif ESP32: Side-Channel Attacks Against Embedded Security
Researchers demonstrated that flash encryption on Espressif ESP32 chips can be broken using side-channel power analysis. By measuring power traces during AES operations, attackers can recover encryption keys and potentially decrypt firmware stored in flash memory.
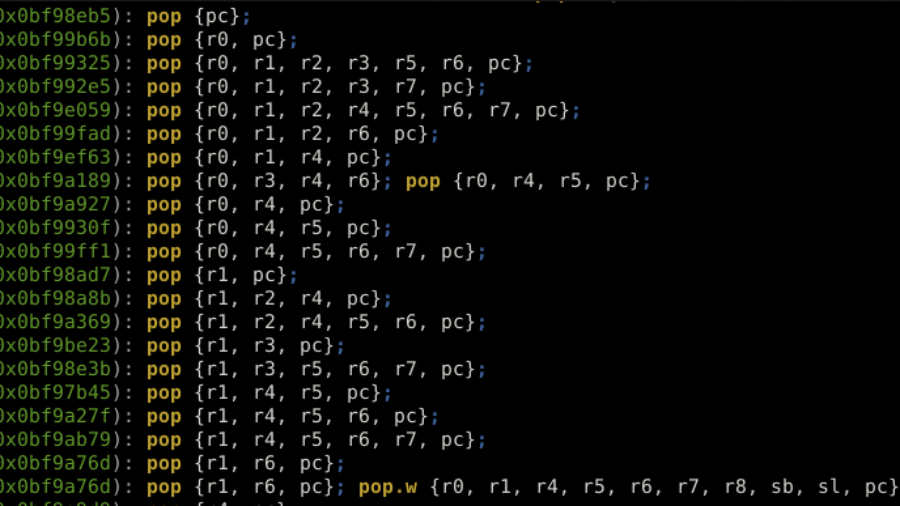
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.