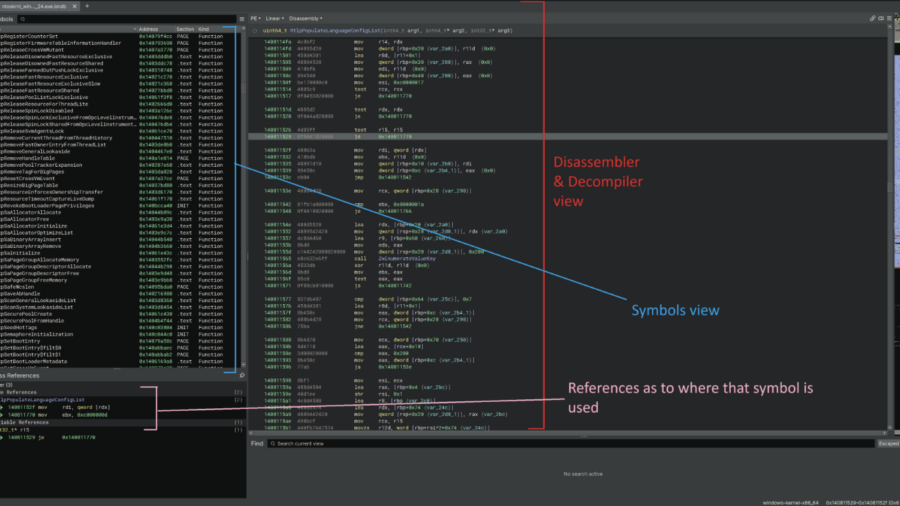
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
Windows Defender ACL Blocking: A Silent Technique With Serious Impact
The article analyzes a technique that disables Microsoft Defender by modifying file ACLs to block security services from accessing critical system DLLs. This silent method prevents Defender from starting without triggering obvious alerts.
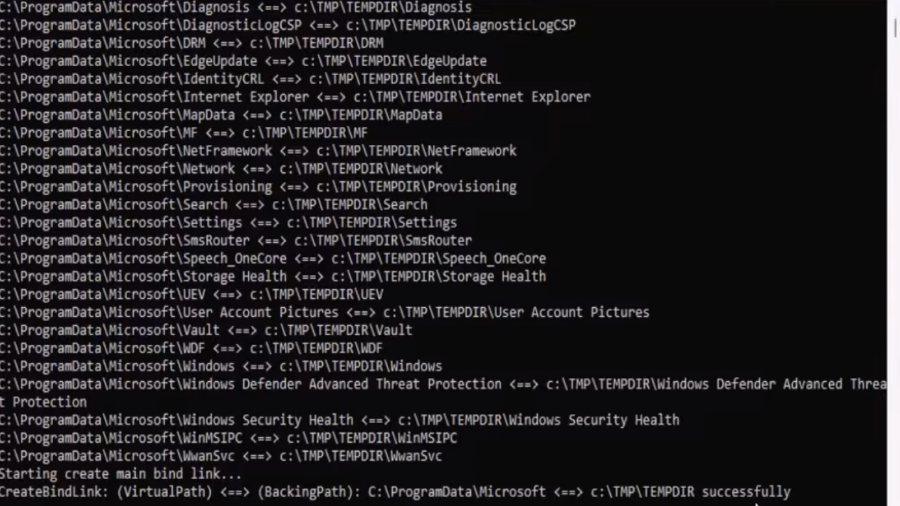
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.