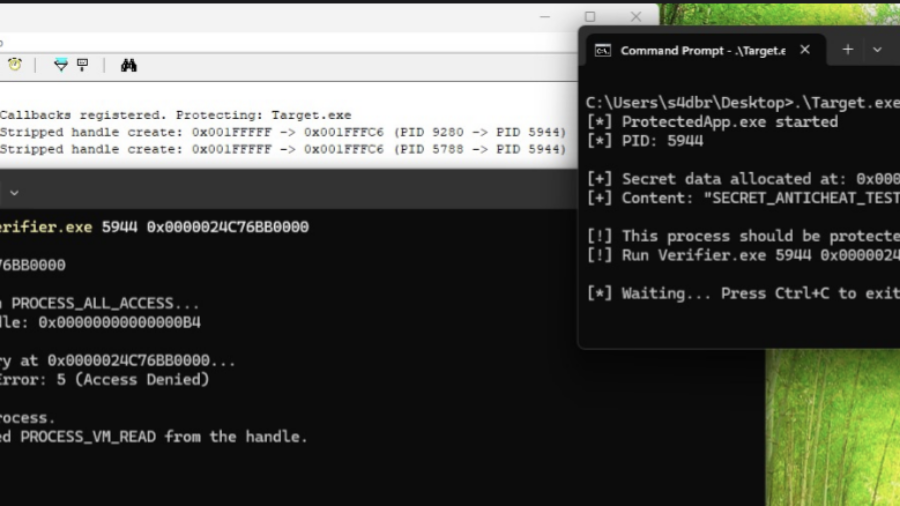
The article explains how modern kernel-level anti-cheat systems work, describing their driver architecture, callbacks, memory monitoring, and detection methods used to identify cheats that operate at the same privilege level as the operating system kernel.
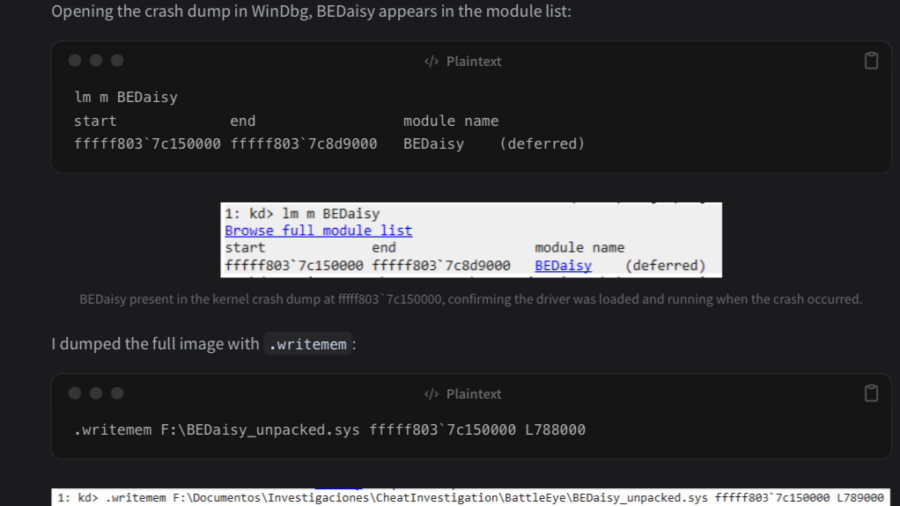
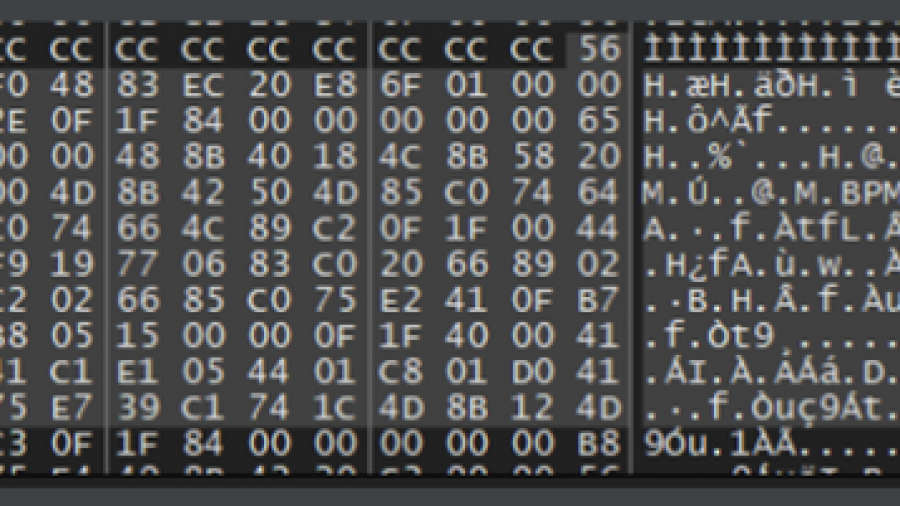
Reversing BEDaisy.sys: Static Analysis of BattlEye’s Kernel Anti-Cheat Driver
The article analyzes the Windows kernel driver BEDaisy.sys, used by BattlEye anti-cheat. Through static reverse engineering, it explores driver architecture, APC usage, hardware fingerprinting, import handling, and detection mechanisms used to monitor system activity.
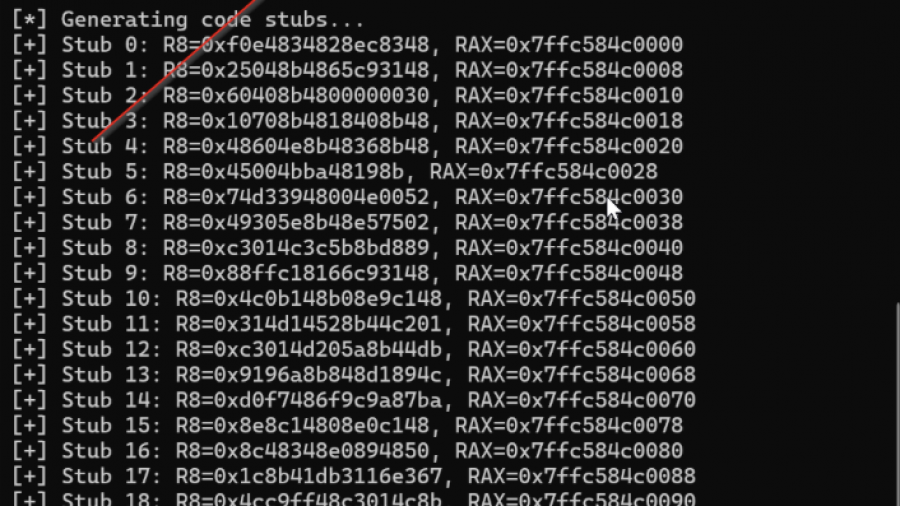
Defeating Windows DEP Using ROP Chains Leveraging VirtualAlloc
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
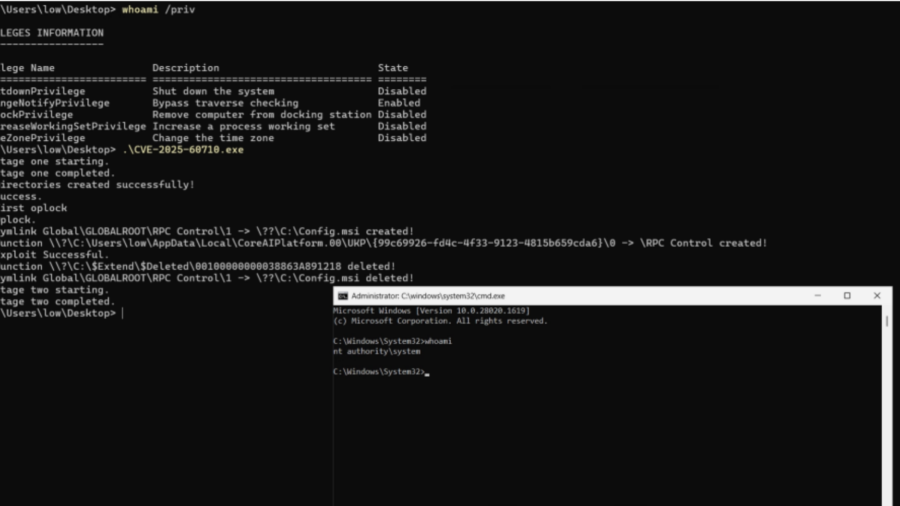
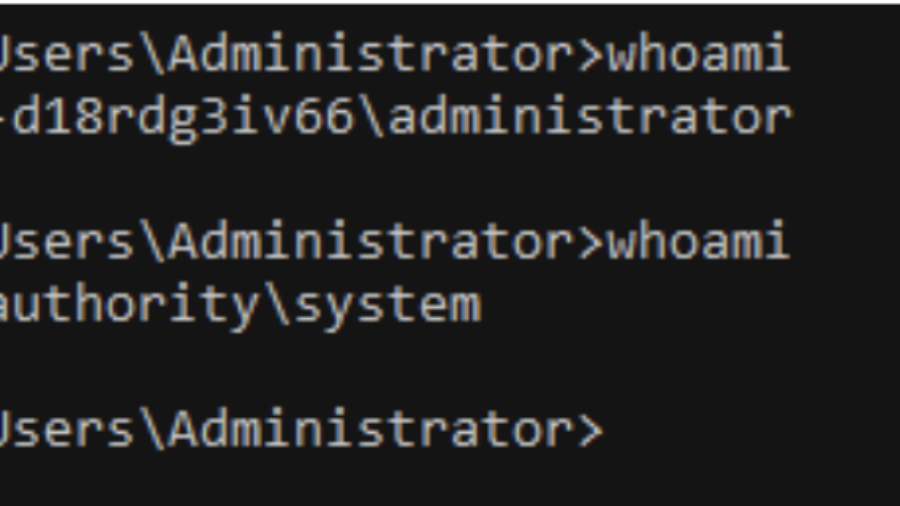
Total Recall – Retracing Your Steps Back to NT AUTHORITY\SYSTEM
A Windows elevation-of-privilege flaw in the Recall scheduled task let low-privileged users trigger it via WNF and abuse unsafe directory cleanup to execute arbitrary actions as NT AUTHORITY\SYSTEM.
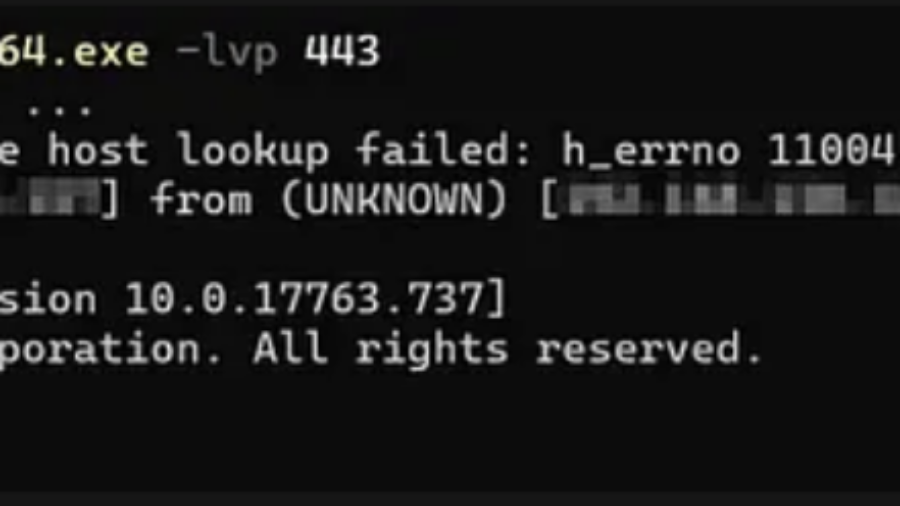
Windows Kernel Debugging
The article explains how to set up Windows kernel debugging over a network using WinDBG and a host/target configuration. It covers enabling debug mode, connecting WinDBG to a remote VM, and using kernel debug infrastructure for low-level inspection and manipulation.
Mastering Living off the Process in Offensive Security
No need for overusing WriteProcessMemory, VirtualAlloc, injecting a DLL, etc. This way, everything you need to manipulate the remote process is self-contained and already available to the process.