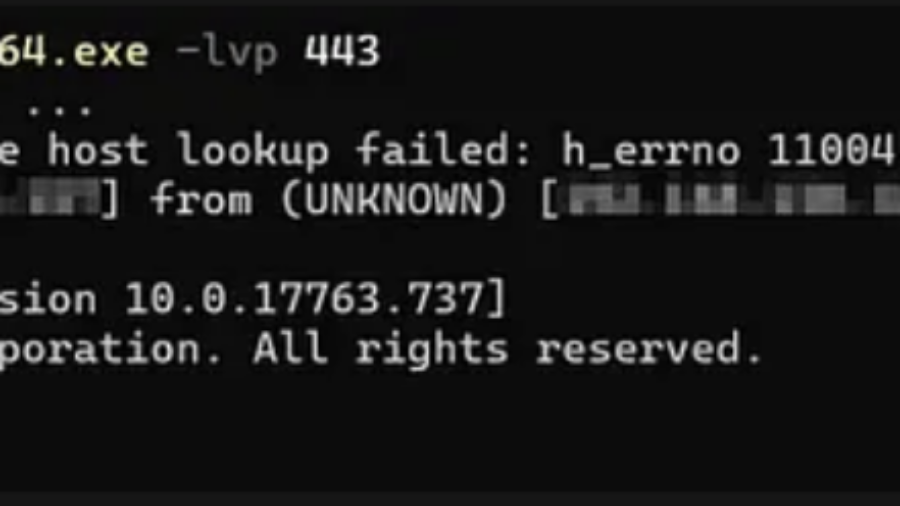
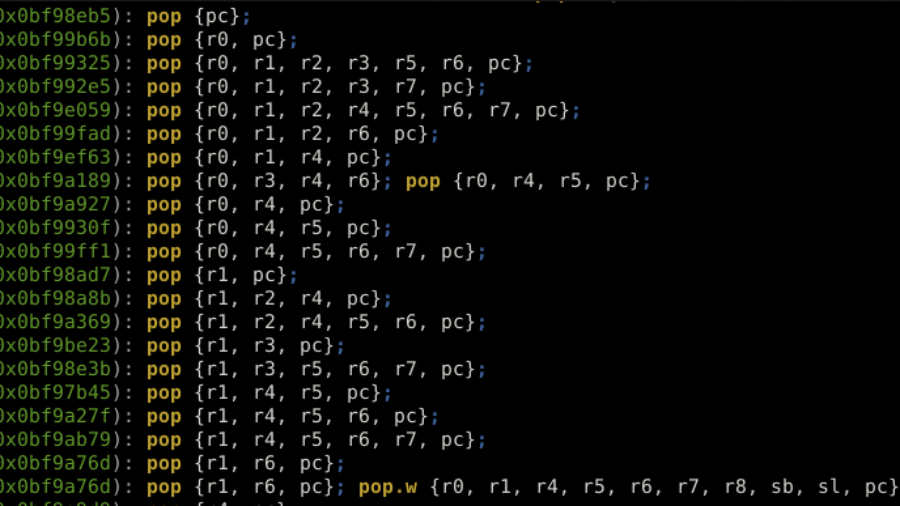
Uses manual Return-Oriented Programming (ROP) to chain existing code fragments and call VirtualAlloc, changing memory permissions to bypass Windows DEP and then execute shellcode in exploited process memory.
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.