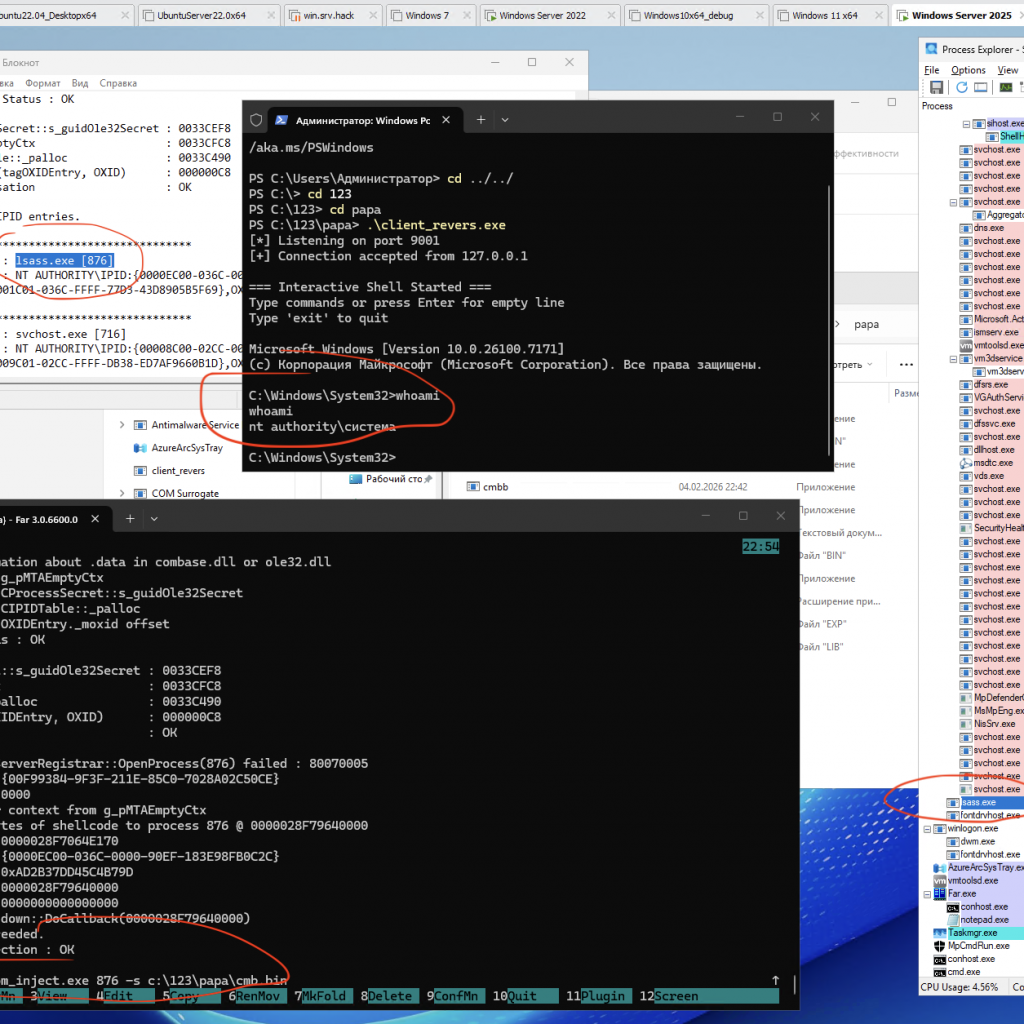
A PoC/demo demonstrating code injection via COM (using the IRundown::DoCallback() mechanism) to execute a payload in the context of a selected process, including lsass.exe (or any other PID).
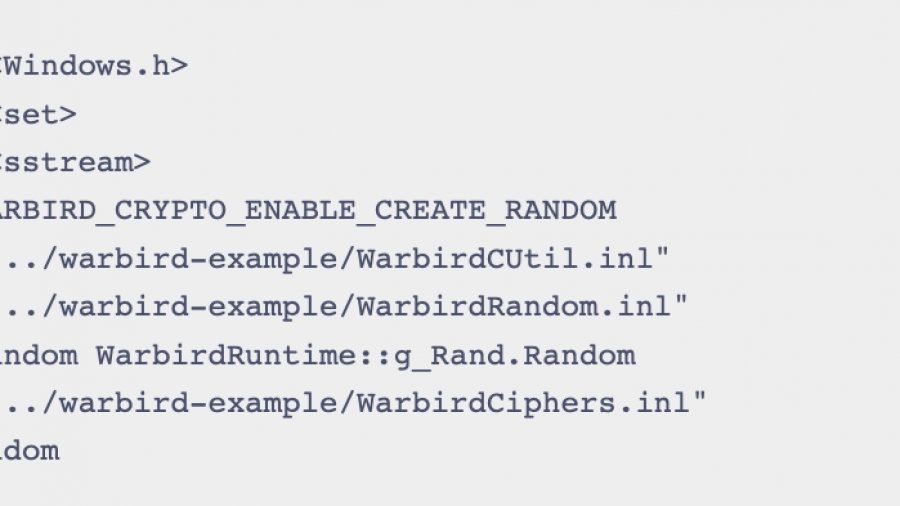
Abusing Microsoft Warbird for Shellcode Execution
The article demonstrates an EDR bypass by using an undocumented Warbird interface to stealthily load shellcode.
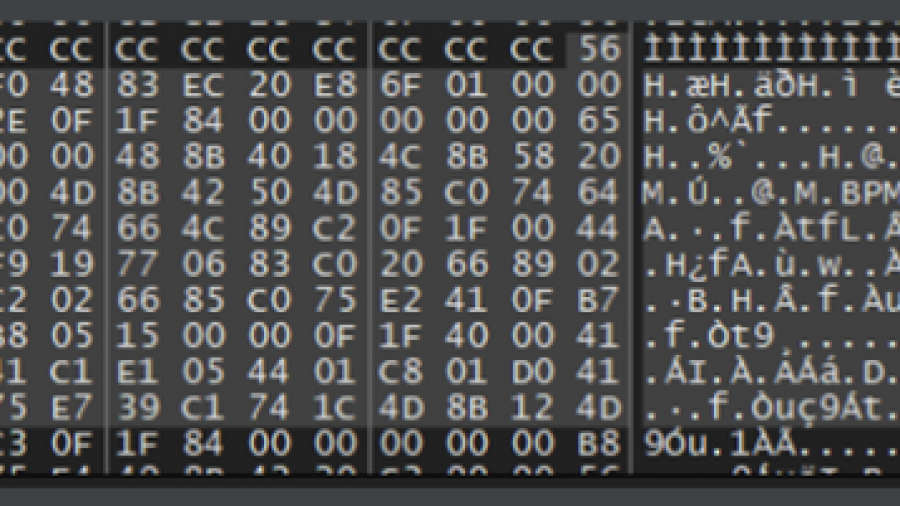
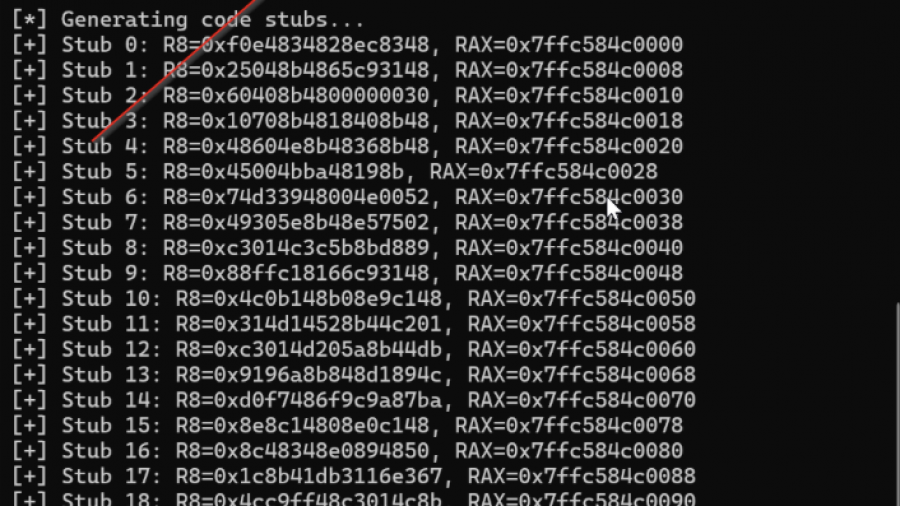
NO ALLOC, NO PROBLEM: LEVERAGING PROGRAM ENTRY POINTS FOR PROCESS INJECTION
Remote process injection and looking for a few under-the-radar techniques that were either not documented well and/or contained minimalist core requirements for functionality.
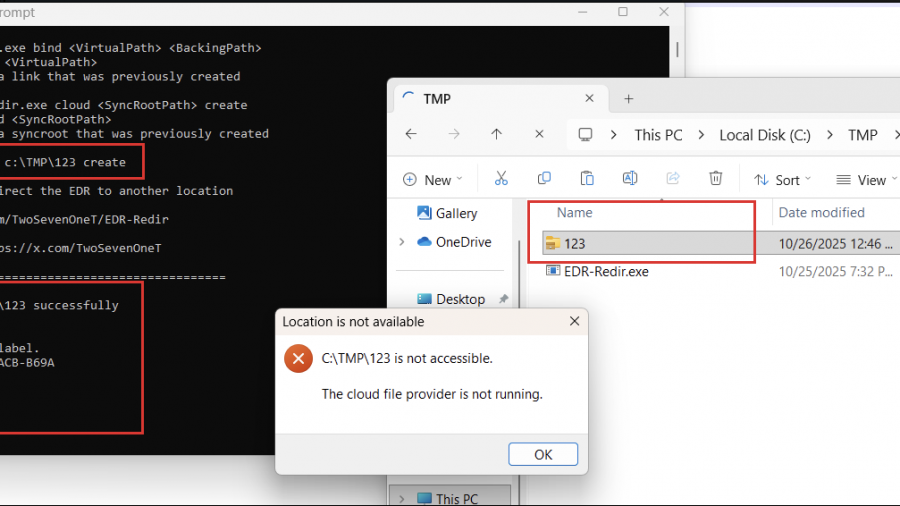
Using EDR-Redir To Break EDR Via Bind Link and Cloud Filter
the technique of exploiting the Bind Filter driver (bindflt.sys) to redirect folders containing the executable files of EDRs to a location that I completely control.
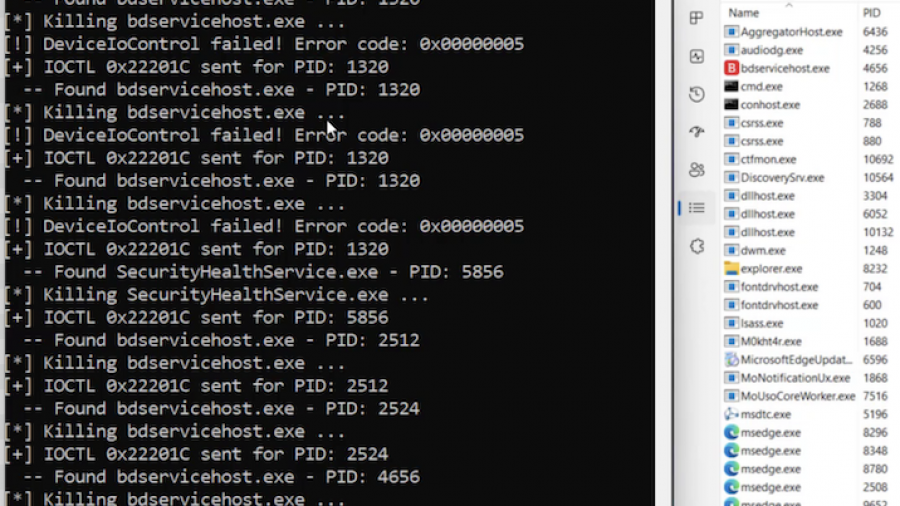
AV EDR Killer Project
av-edr-kill is a BYOVD (Bring Your Own Vulnerable Driver) proof-of-concept whose goal is to terminate security-product processes (AV/EDR), including Protected Process Light (PPL) targets, by abusing a legitimately signed third-party kernel driver.
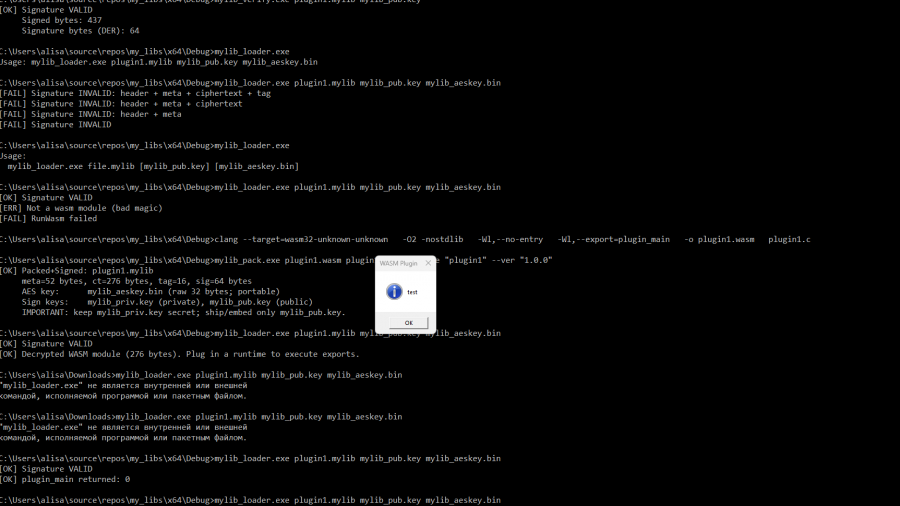
Securely Embedding WASM Plugins in Your Project
libraries for packaging, verifying, decrypting, and executing WebAssembly plugins packaged in a custom container format .mylib (version 2).
Mastering Living off the Process in Offensive Security
No need for overusing WriteProcessMemory, VirtualAlloc, injecting a DLL, etc. This way, everything you need to manipulate the remote process is self-contained and already available to the process.
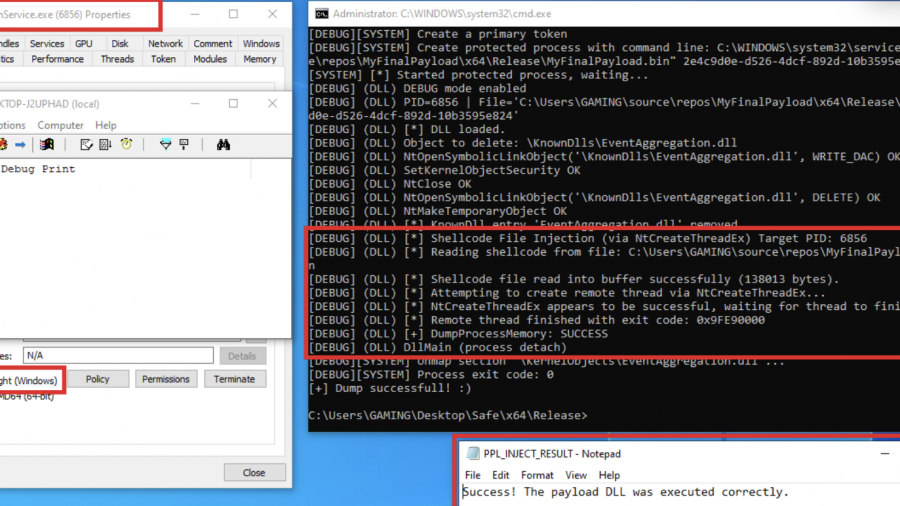
Exploring Protected Process Light and Exploits
Red team technique—process injection—and how to leverage it against Protected Process Light (PPL)