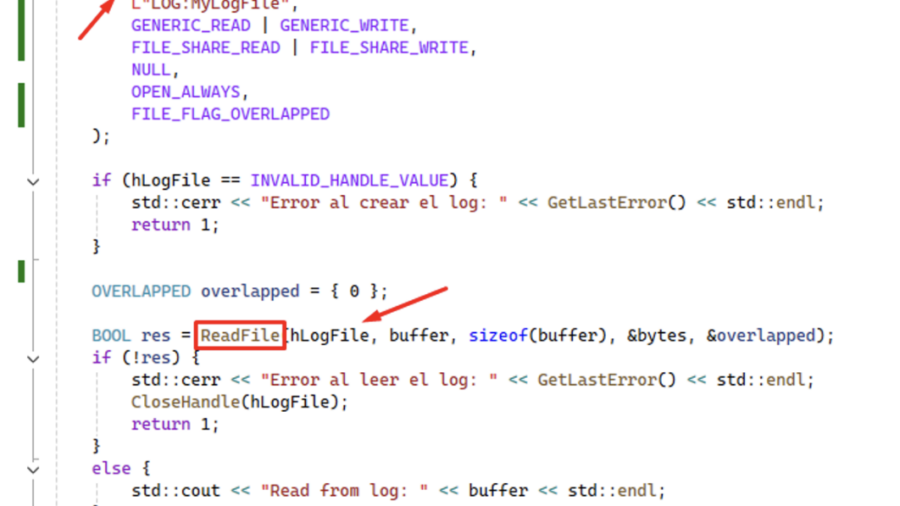
CVE-2026-2636 Logic bug in Windows’ CLFS driver: calling ReadFile on a .blf log handle pushes CLFS.sys into an unrecoverable state and triggers an immediate BSoD — local DoS with only user privileges.
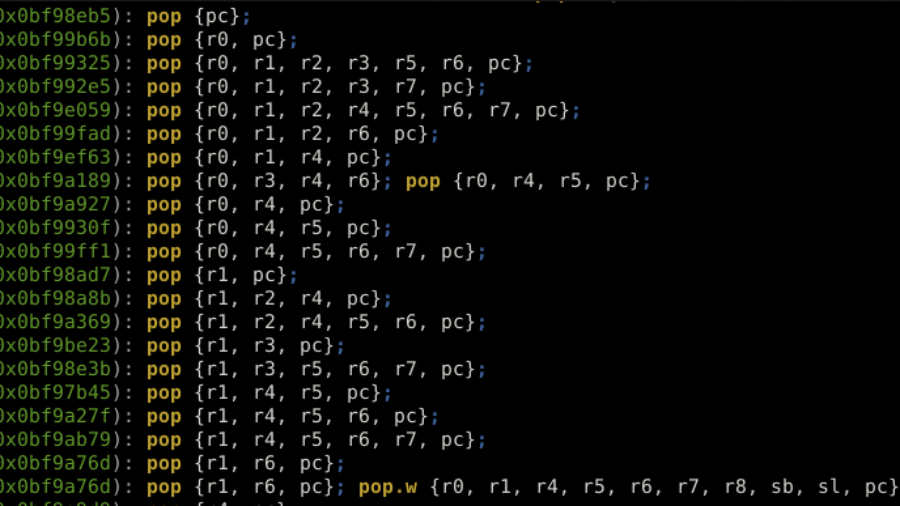
ROP the ROM: Exploiting a Stack Buffer Overflow on STM32H5 in Multiple Ways
Article details exploiting a stack buffer overflow on an STM32H5. It demonstrates basic shellcode injection, then bypassing a non-executable stack (XN/MPU) using Return-Oriented Programming (ROP) with gadgets from the chip’s ROM code to dump firmware, showcasing advanced embedded exploitation techniques.
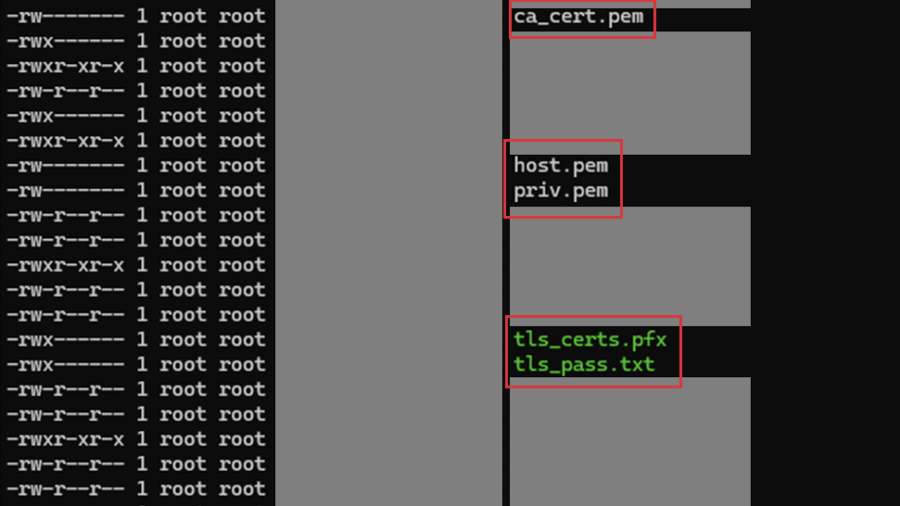
Multiple vulnerabilities in CPSD CryptoPro Secure Disk for BitLocker
SEC Consult found two high-impact vulnerabilities in CryptoPro Secure Disk for BitLocker (<7.6.6/7.7.1). An attacker with physical access can bypass integrity checks to gain root access (CVE-2025-10010) and read sensitive network data stored in cleartext. Patches are available.
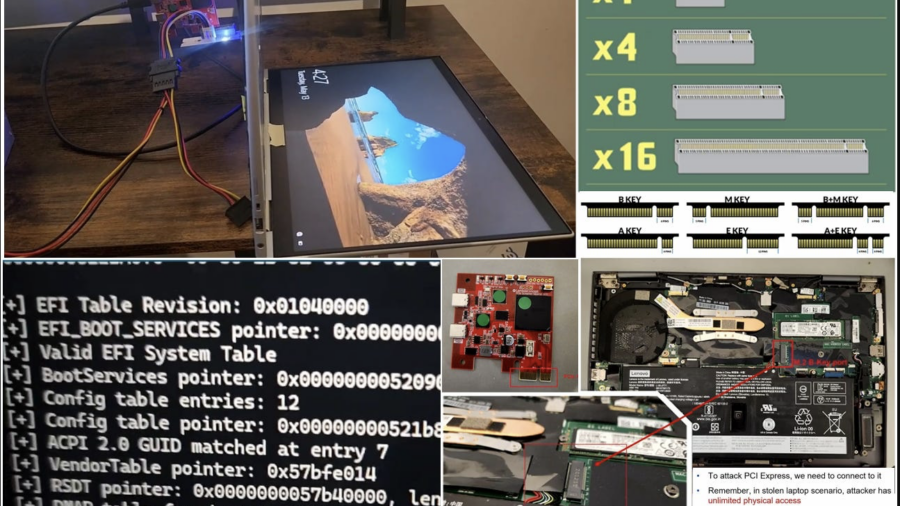
Hacking a stolen laptop: bypassing Windows security (BitLocker etc.) using PCI connector.
The article outlines security researcher Pierre-Nicolas Allard-Coutu’s demonstration of attacking a stolen Windows laptop using a PCIe connector to bypass protections like BitLocker, TPM, and Kernel DMA Protection, showing how to gain SYSTEM access.
Windows Kernel Debugging
The article explains how to set up Windows kernel debugging over a network using WinDBG and a host/target configuration. It covers enabling debug mode, connecting WinDBG to a remote VM, and using kernel debug infrastructure for low-level inspection and manipulation.
RPC Proxy Injection Part II: Breaking Elastic EDR Telemetry
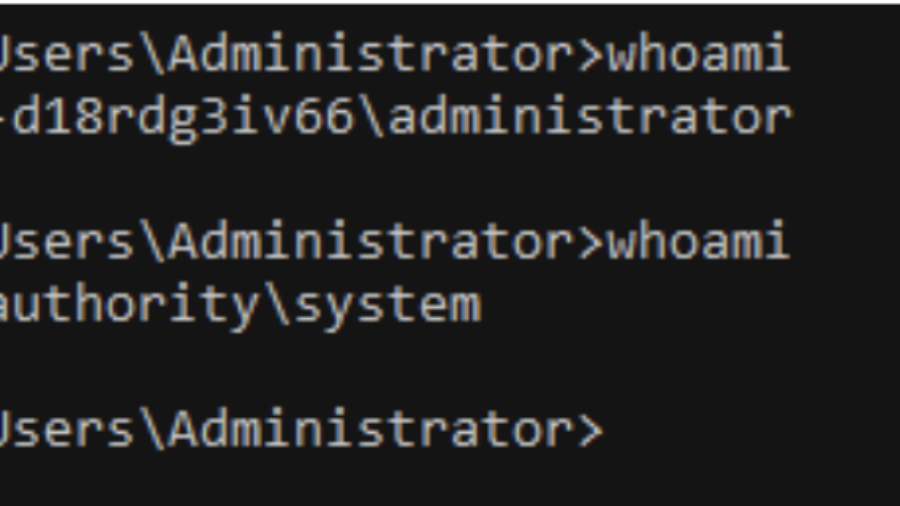
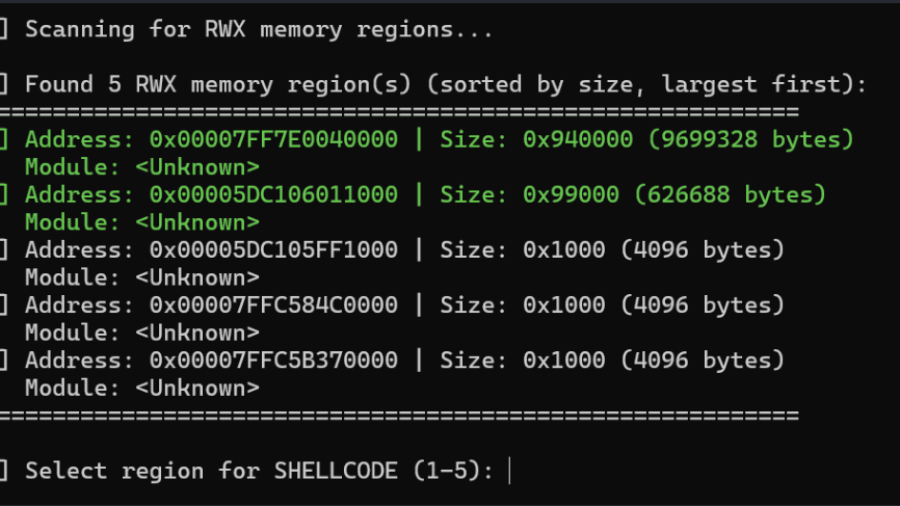
The article explains enhancing RPC Proxy Injection to evade Elastic EDR telemetry by avoiding common API calls like WriteProcessMemory and CreateRemoteThread, using custom shellcode delivery via thread descriptions and APCs to hide malicious behavior.
Living off the Process
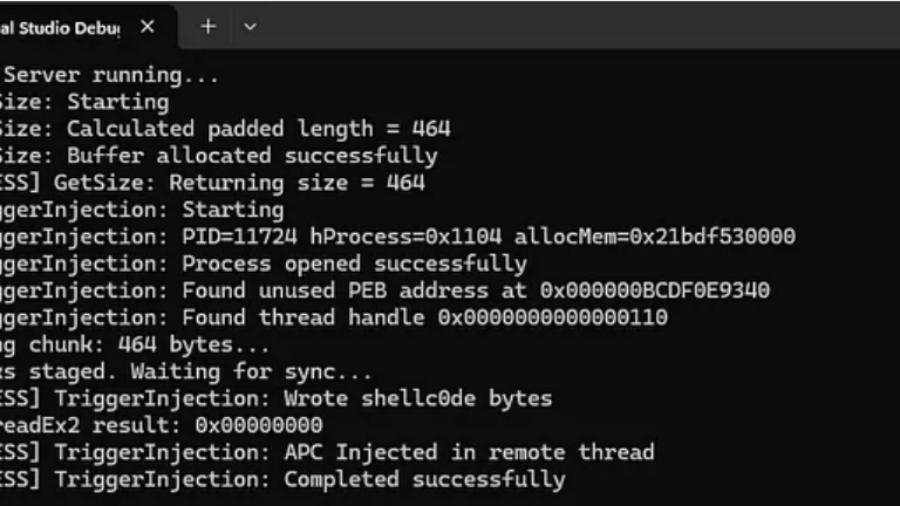
The article “Living off the Process” details a technique to inject and execute shellcode into a remote Windows process by reusing existing RWX memory, ROP gadgets, and threads within that process, avoiding conventional memory allocation and lowering detection footprint.
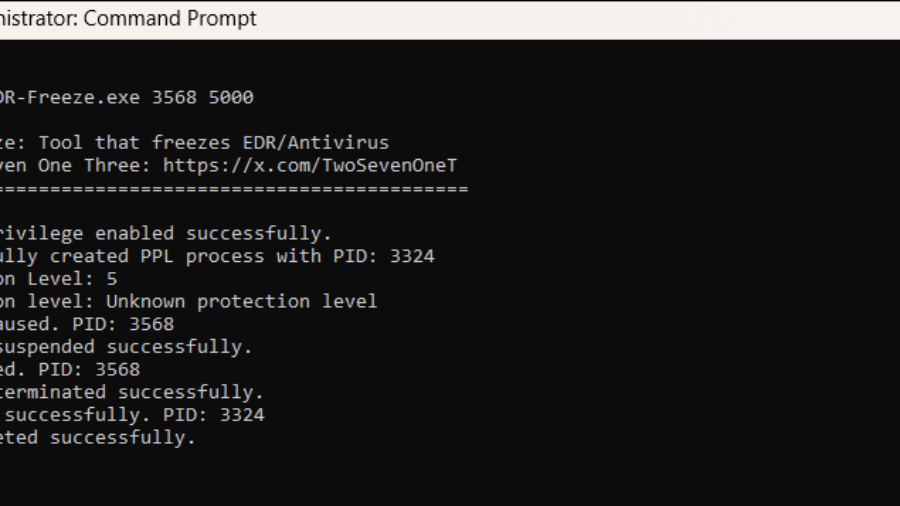
EDR-Freeze: A Tool That Puts EDRs And Antivirus Into A Coma State
The article presents EDR-Freeze, a user-mode tool exploiting Windows Error Reporting to suspend EDR and antivirus processes by abusing MiniDumpWriteDump and WerFaultSecure, leaving security agents in a “coma” and creating a blind spot for attacks.
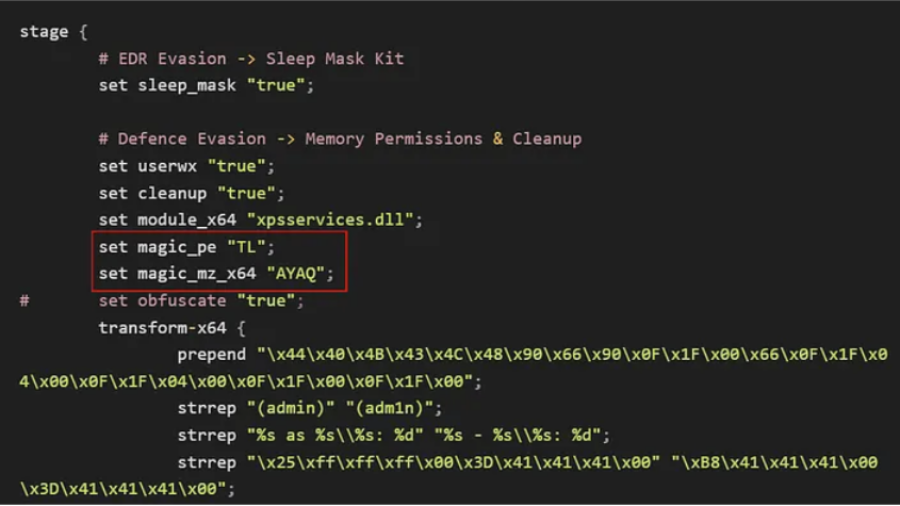
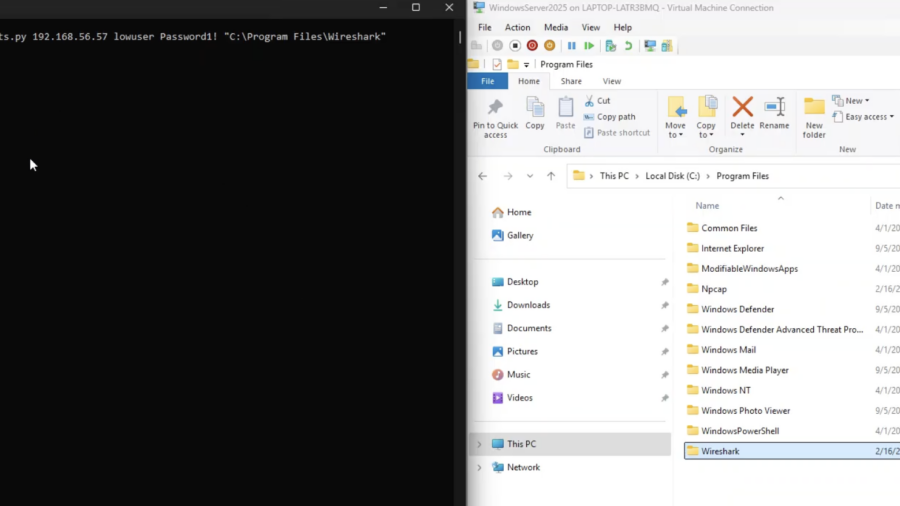
Bypassing Elastic EDR to Perform Lateral Movement
Article demonstrates how lateral movement can still be achieved in a lab with Elastic EDR and Microsoft ASR enabled by modifying payload delivery and execution techniques, bypassing common detection patterns and highlighting gaps in behavior-based defenses.
EventLog-in: Propagating With Weak Credentials Using the Eventlog Service in Microsoft Windows (CVE-2025-29969)
SafeBreach Labs disclosed a critical RCE in the MS-EVEN RPC service (CVE-2025-29969) that lets low-privilege users write arbitrary files remotely on Windows 11/Server 2025, bypassing share limits. Patched May 2025.